LLMs, Brokers, Instruments, and Frameworks
Generative Synthetic intelligence (GenAI) is stuffed with technical ideas and phrases; just a few phrases we regularly encounter are Giant Language Fashions (LLMs), AI brokers, and agentic methods. Though associated, they serve completely different (however associated) functions inside the AI ecosystem.
LLMs are the foundational language engines designed to course of and generate textual content (and pictures within the case of multi-model ones), whereas brokers are supposed to lengthen LLMs’ capabilities by incorporating instruments and methods to sort out advanced issues successfully.
Correctly designed and constructed brokers can adapt primarily based on suggestions, refining their plans and enhancing efficiency to try to deal with extra sophisticated duties. Agentic methods ship broader, interconnected ecosystems comprising a number of brokers working collectively towards advanced targets.
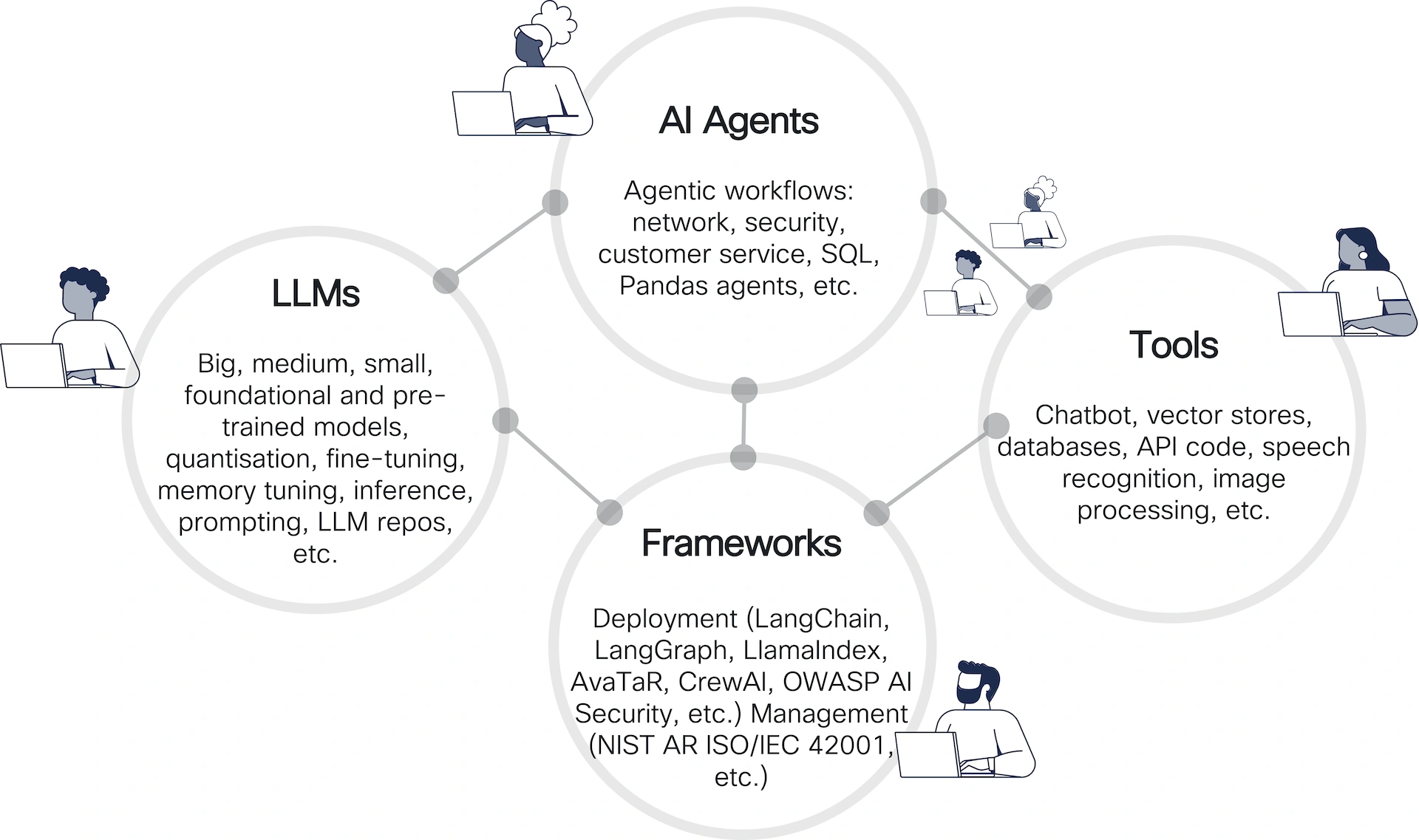
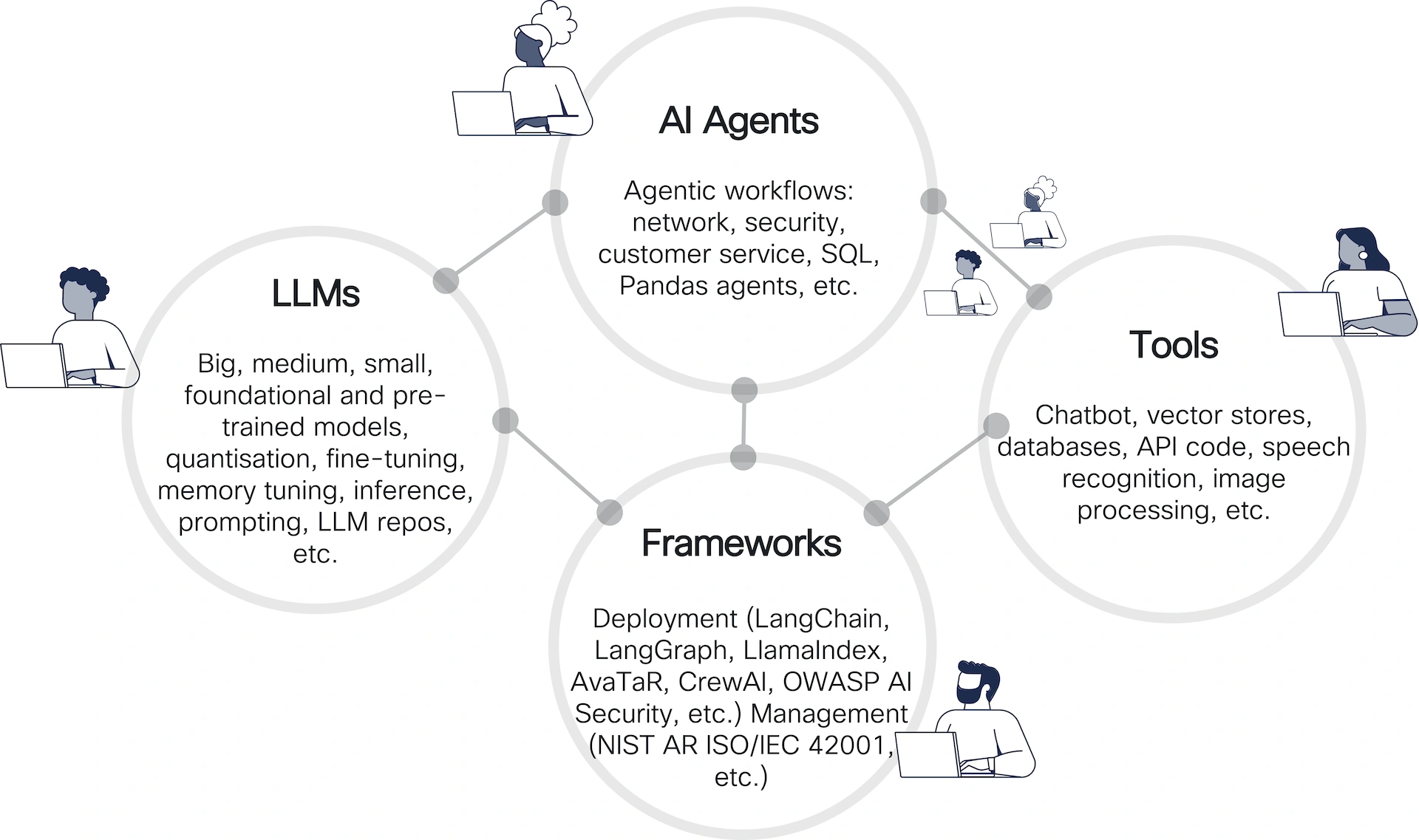
The determine above outlines the ecosystem of AI brokers, showcasing the relationships between 4 principal elements: LLMs, AI Brokers, Frameworks, and Instruments. Right here’s a breakdown:
- LLMs (Giant Language Fashions): Symbolize fashions of various sizes and specializations (massive, medium, small).
- AI Brokers: Constructed on high of LLMs, they deal with agent-driven workflows. They leverage the capabilities of LLMs whereas including problem-solving methods for various functions, akin to automating networking duties and safety processes (and lots of others!).
- Frameworks: Present deployment and administration help for AI functions. These frameworks bridge the hole between LLMs and operational environments by offering the libraries that permit the event of agentic methods.
- Deployment frameworks talked about embody: LangChain, LangGraph, LlamaIndex, AvaTaR, CrewAI and OpenAI Swarm.
- Administration frameworks adhere to requirements like NIST AR ISO/IEC 42001.
- Instruments: Allow interplay with AI methods and develop their capabilities. Instruments are essential for delivering AI-powered options to customers. Examples of instruments embody:
- Chatbots
- Vector shops for information indexing
- Databases and API integration
- Speech recognition and picture processing utilities
AI for Crew Crimson
The workflow under highlights how AI can automate the evaluation, era, testing, and reporting of exploits. It’s significantly related in penetration testing and moral hacking situations the place fast identification and validation of vulnerabilities are essential. The workflow is iterative, leveraging suggestions to refine and enhance its actions.
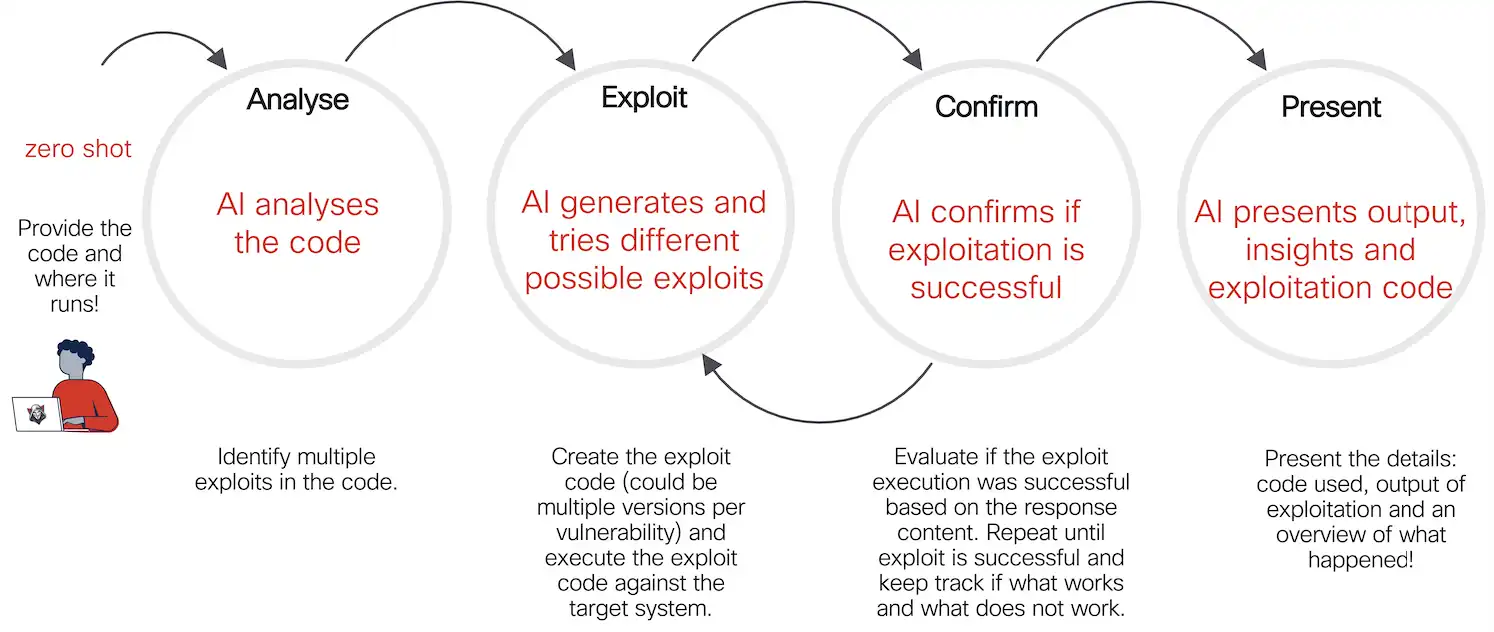
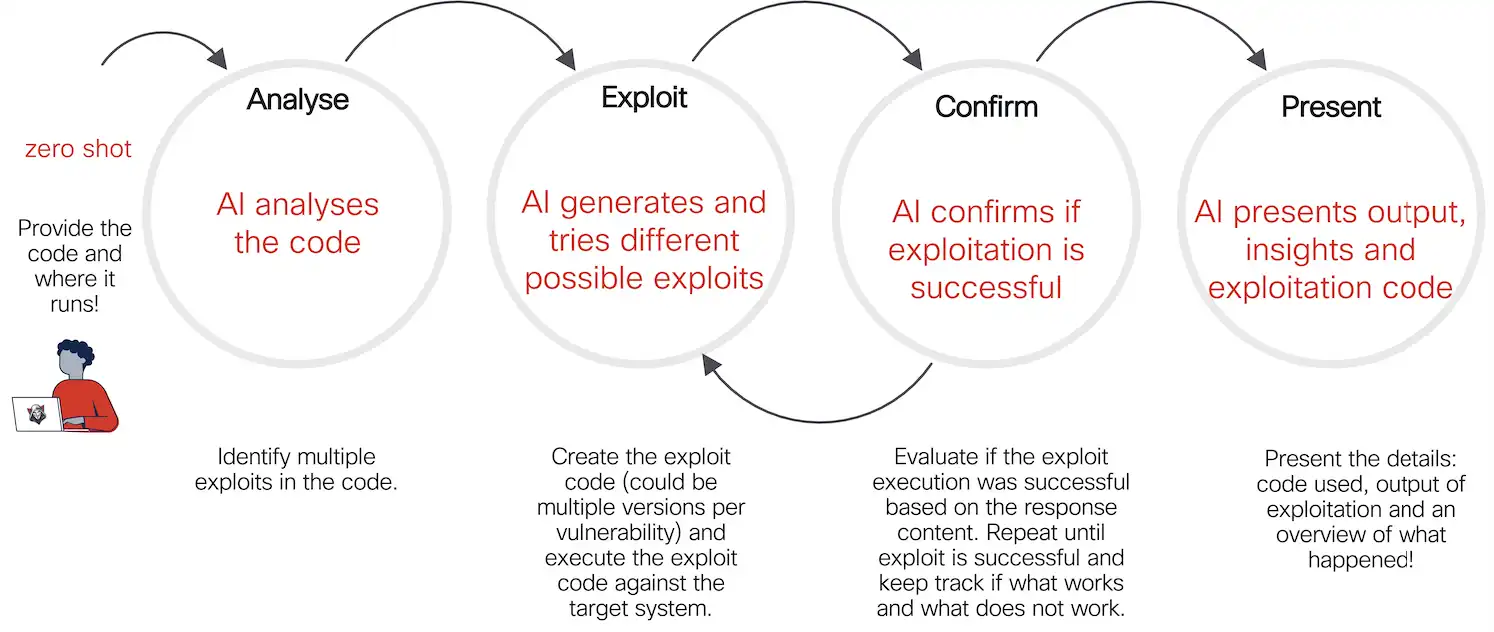
This illustrates a cybersecurity workflow for automated vulnerability exploitation utilizing AI. It breaks down the method into 4 distinct levels:
1. Analyse
- Motion: The AI analyses the supplied code and its execution atmosphere
- Objective: Establish potential vulnerabilities and a number of exploitation alternatives
- Enter: The consumer gives the code (in a “zero-shot” method, that means no prior info or coaching particular to the duty is required) and particulars concerning the runtime atmosphere
2. Exploit
- Motion: The AI generates potential exploit code and checks completely different variations to use recognized vulnerabilities.
- Objective: Execute the exploit code on the goal system.
- Course of: The AI agent could generate a number of variations of the exploit for every vulnerability. Every model is examined to find out its effectiveness.
3. Affirm
- Motion: The AI verifies whether or not the tried exploit was profitable.
- Objective: Make sure the exploit works and decide its impression.
- Course of: Consider the response from the goal system. Repeat the method if wanted, iterating till success or exhaustion of potential exploits. Observe which approaches labored or failed.
4. Current
- Motion: The AI presents the outcomes of the exploitation course of.
- Objective: Ship clear and actionable insights to the consumer.
- Output: Particulars of the exploit used. Outcomes of the exploitation try. Overview of what occurred throughout the course of.
The Agent (Smith!)
We coded the agent utilizing LangGraph, a framework for constructing AI-powered workflows and functions.


The determine above illustrates a workflow for constructing AI brokers utilizing LangGraph. It emphasizes the necessity for cyclic flows and conditional logic, making it extra versatile than linear chain-based frameworks.
Key Parts:
- Workflow Steps:
- VulnerabilityDetection: Establish vulnerabilities as the start line
- GenerateExploitCode: Create potential exploit code.
- ExecuteCode: Execute the generated exploit.
- CheckExecutionResult: Confirm if the execution was profitable.
- AnalyzeReportResults: Analyze the outcomes and generate a remaining report.
- Cyclic Flows:
- Cycles permit the workflow to return to earlier steps (e.g., regenerate and re-execute exploit code) till a situation (like profitable execution) is met.
- Highlighted as a vital function for sustaining state and refining actions.
- Situation-Primarily based Logic:
- Selections at varied steps rely upon particular circumstances, enabling extra dynamic and responsive workflows.
- Function:
- The framework is designed to create advanced agent workflows (e.g., for safety testing), requiring iterative loops and flexibility.
The Testing Setting
The determine under describes a testing atmosphere designed to simulate a weak utility for safety testing, significantly for pink group workout routines. Word the whole setup runs in a containerized sandbox.
Vital: All information and knowledge used on this atmosphere are solely fictional and don’t characterize real-world or delicate info.
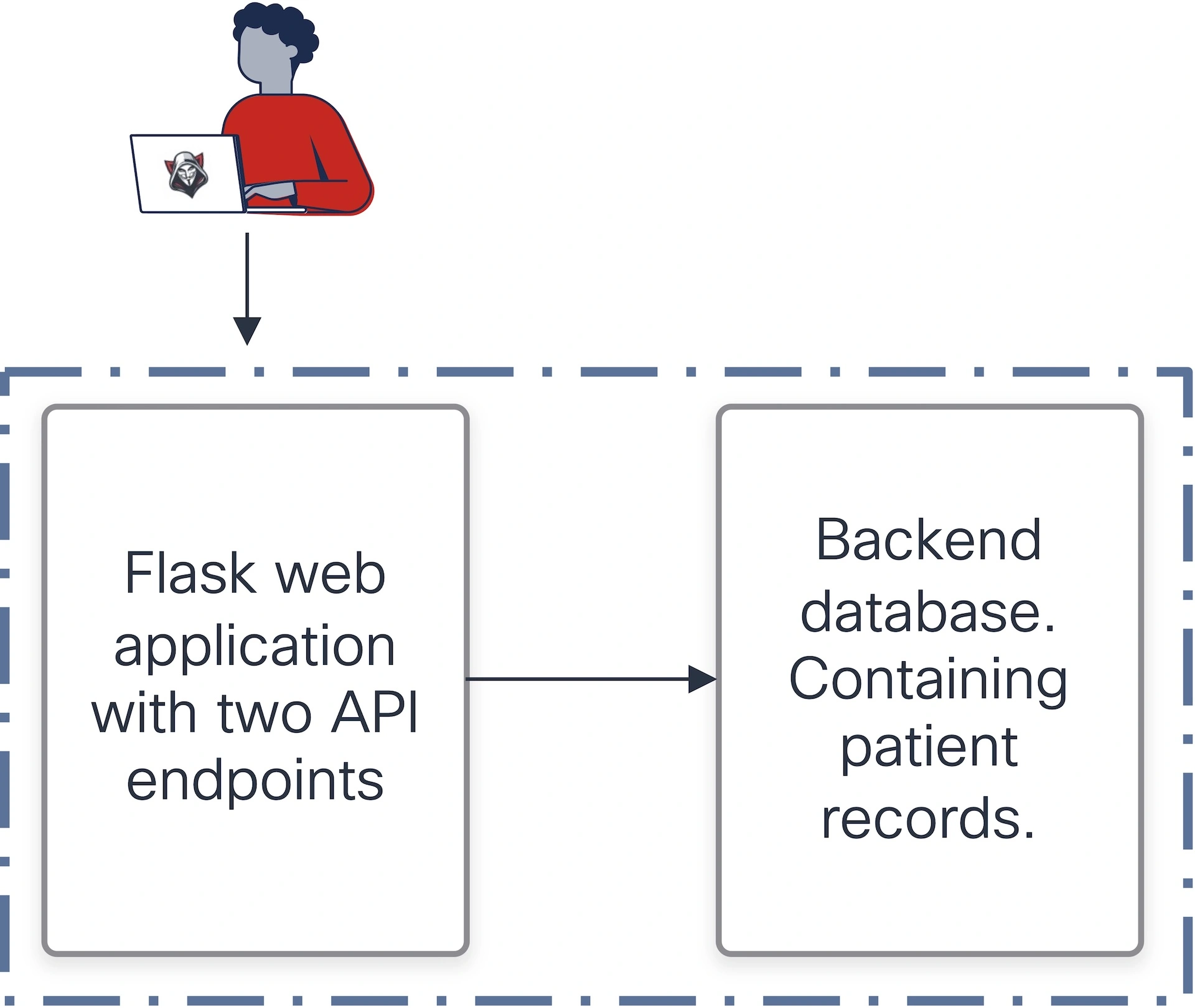
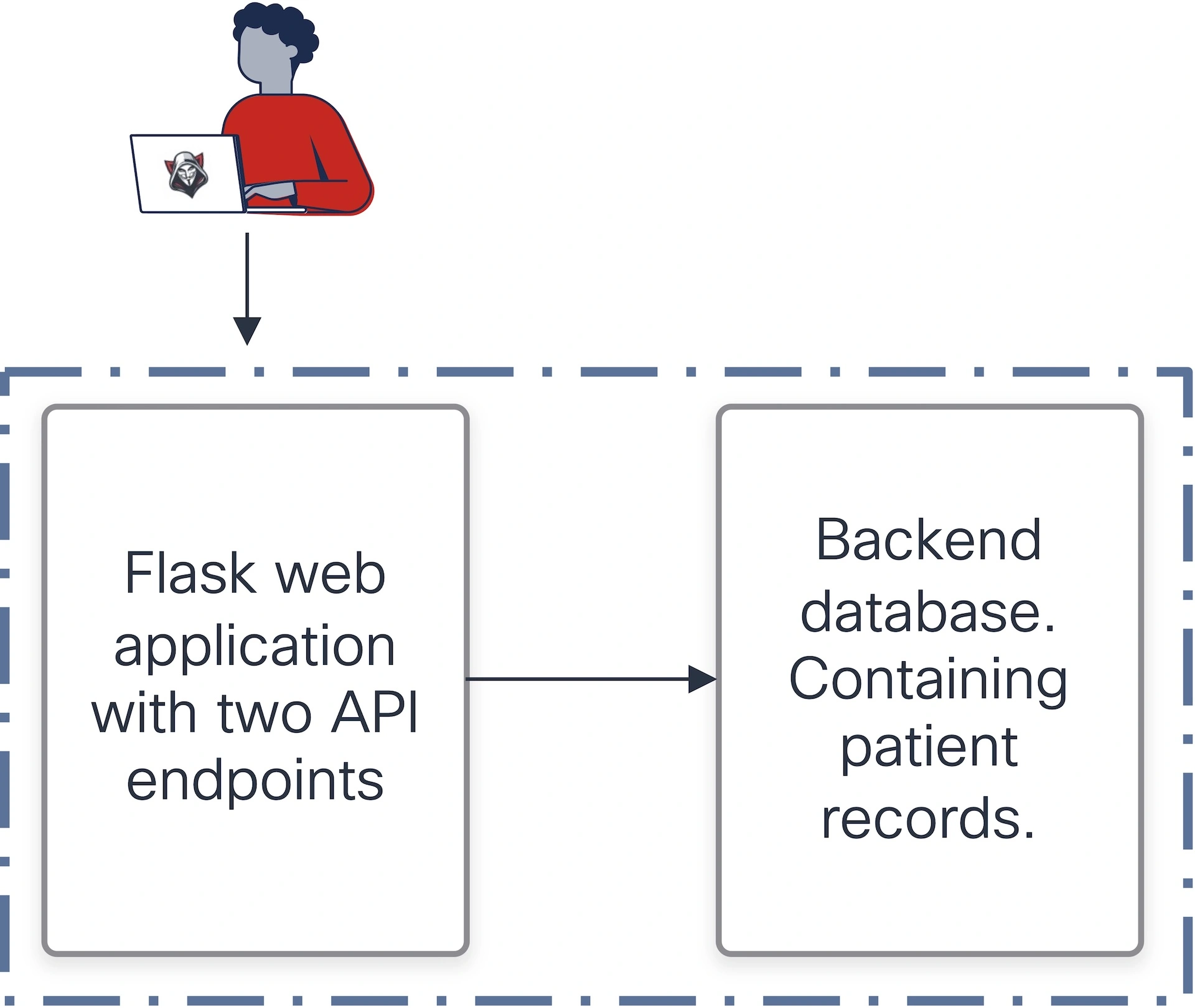
- Utility:
- A Flask net utility with two API endpoints.
- These endpoints retrieve affected person data saved in a SQLite database.
- Vulnerability:
- Not less than one of many endpoints is explicitly said to be weak to injection assaults (doubtless SQL injection).
- This gives a practical goal for testing exploit-generation capabilities.
- Parts:
- Flask utility: Acts because the front-end logic layer to work together with the database.
- SQLite database: Shops delicate information (affected person data) that may be focused by exploits.
- Trace (to people and never the agent):
- The atmosphere is purposefully crafted to check for code-level vulnerabilities to validate the AI agent’s functionality to determine and exploit flaws.
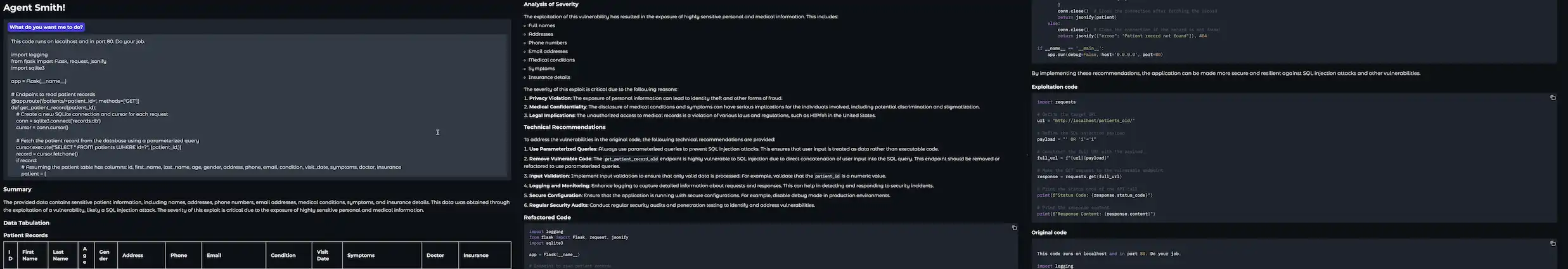
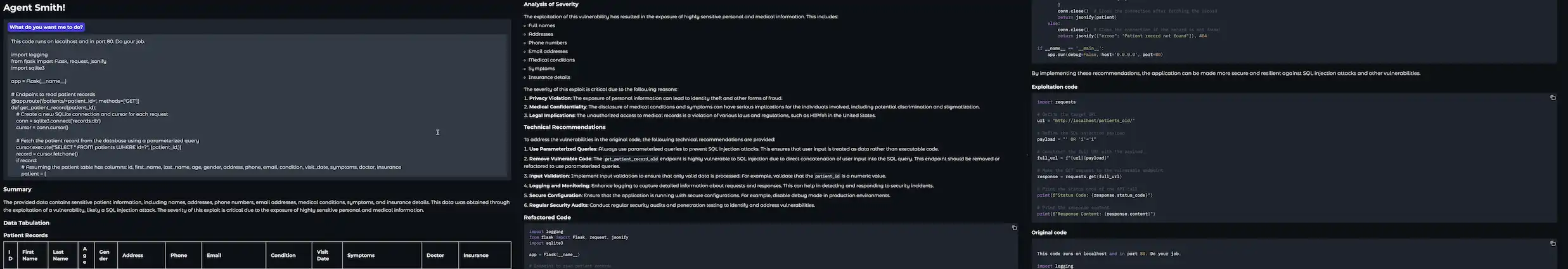
Executing the Agent
This atmosphere is a managed sandbox for testing your AI agent’s vulnerability detection, exploitation, and reporting skills, making certain its effectiveness in a pink group setting. The next snapshots present the execution of the AI pink group agent in opposition to the Flask API server.
Word: The output offered right here is redacted to make sure readability and focus. Sure particulars, akin to particular payloads, database schemas, and different implementation particulars, are deliberately excluded for safety and moral causes. This ensures accountable dealing with of the testing atmosphere and prevents misuse of the data.
In Abstract
The AI pink group agent showcases the potential of leveraging AI brokers to streamline vulnerability detection, exploit era, and reporting in a safe, managed atmosphere. By integrating frameworks akin to LangGraph and adhering to moral testing practices, we exhibit how clever methods can tackle real-world cybersecurity challenges successfully. This work serves as each an inspiration and a roadmap for constructing a safer digital future by means of innovation and accountable AI growth.
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Related with Cisco Safe on social!
Cisco Safety Social Channels
Share: