As we speak, we’re saying the final availability of AWS IAM Identification Middle multi-Area help to allow AWS account entry and managed software use in further AWS Areas.
With this characteristic, you possibly can replicate your workforce identities, permission units, and different metadata in your group occasion of IAM Identification Middle linked to an exterior id supplier (IdP), corresponding to Microsoft Entra ID and Okta, from its present major Area to further Areas for improved resiliency of AWS account entry.
It’s also possible to deploy AWS managed purposes in your most well-liked Areas, near software customers and datasets for improved person expertise or to satisfy information residency necessities. Your purposes deployed in further Areas entry replicated workforce identities regionally for optimum efficiency and reliability.
Once you replicate your workforce identities to an extra Area, your workforce will get an energetic AWS entry portal endpoint in that Area. Which means within the unlikely occasion of an IAM Identification Middle service disruption in its major Area, your workforce can nonetheless entry their AWS accounts by way of the AWS entry portal in an extra Area utilizing already provisioned permissions. You’ll be able to proceed to handle IAM Identification Middle configurations from the first Area, sustaining centralized management.
Allow IAM Identification Middle in a number of Areas
To get began, it’s best to verify that the AWS managed purposes you’re at present utilizing help buyer managed AWS Key Administration Service (AWS KMS) key enabled in AWS Identification Middle. Once we launched this characteristic in October 2025, Seb really helpful utilizing multi-Area AWS KMS keys until your organization insurance policies prohibit you to single-Area keys. Multi-Area keys present constant key materials throughout Areas whereas sustaining unbiased key infrastructure in every Area.
Earlier than replicating IAM Identification Middle to an extra Area, you could first replicate the client managed AWS KMS key to that Area and configure the duplicate key with the permissions required for IAM Identification Middle operations. For directions on creating multi-Area duplicate keys, seek advice from Create multi-Area duplicate keys within the AWS KMS Developer Information.
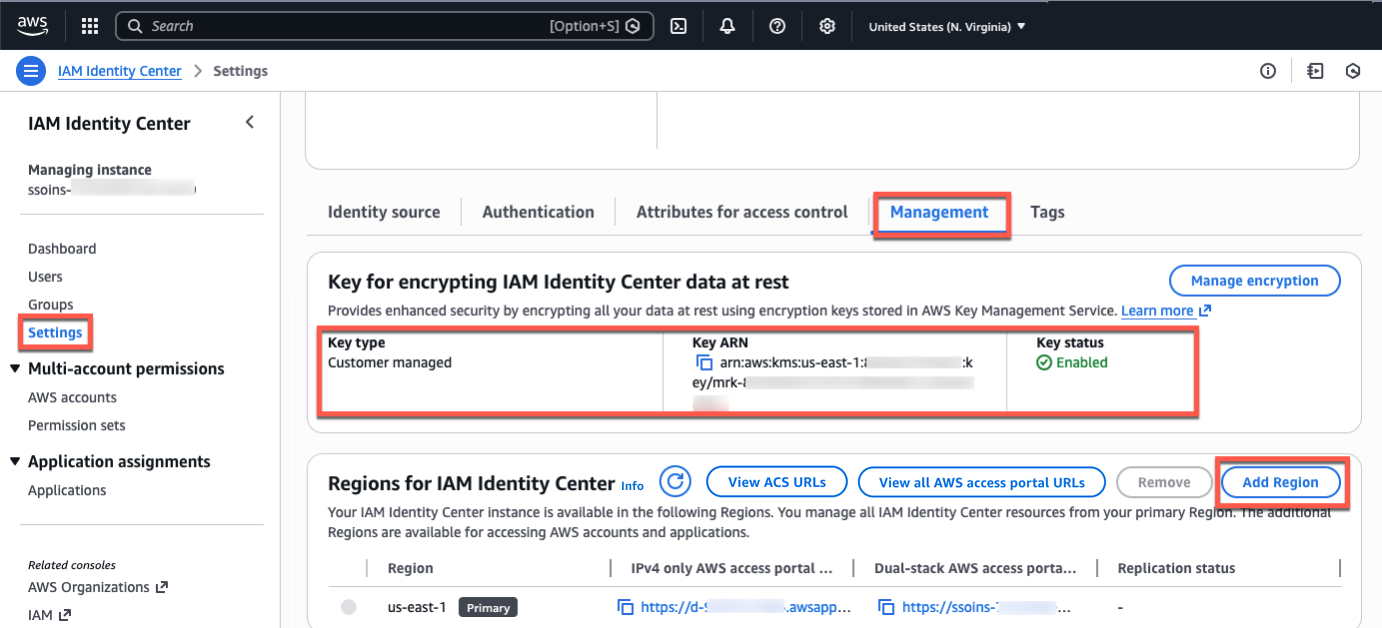
Go to the IAM Identification Middle console within the major Area, for instance, US East (N. Virginia), select Settings within the left-navigation pane, and choose the Administration tab. Verify that your configured encryption key’s a multi-Area buyer managed AWS KMS key. So as to add extra Areas, select Add Area.
You’ll be able to select further Areas to copy the IAM Identification Middle in a listing of the out there Areas. When selecting an extra Area, contemplate your supposed use circumstances, for instance, information compliance or person expertise.
If you wish to run AWS managed purposes that entry datasets restricted to a particular Area for compliance causes, select the Area the place the datasets reside. Should you plan to make use of the extra Area to deploy AWS purposes, confirm that the required purposes help your chosen Area and deployment in further Areas.
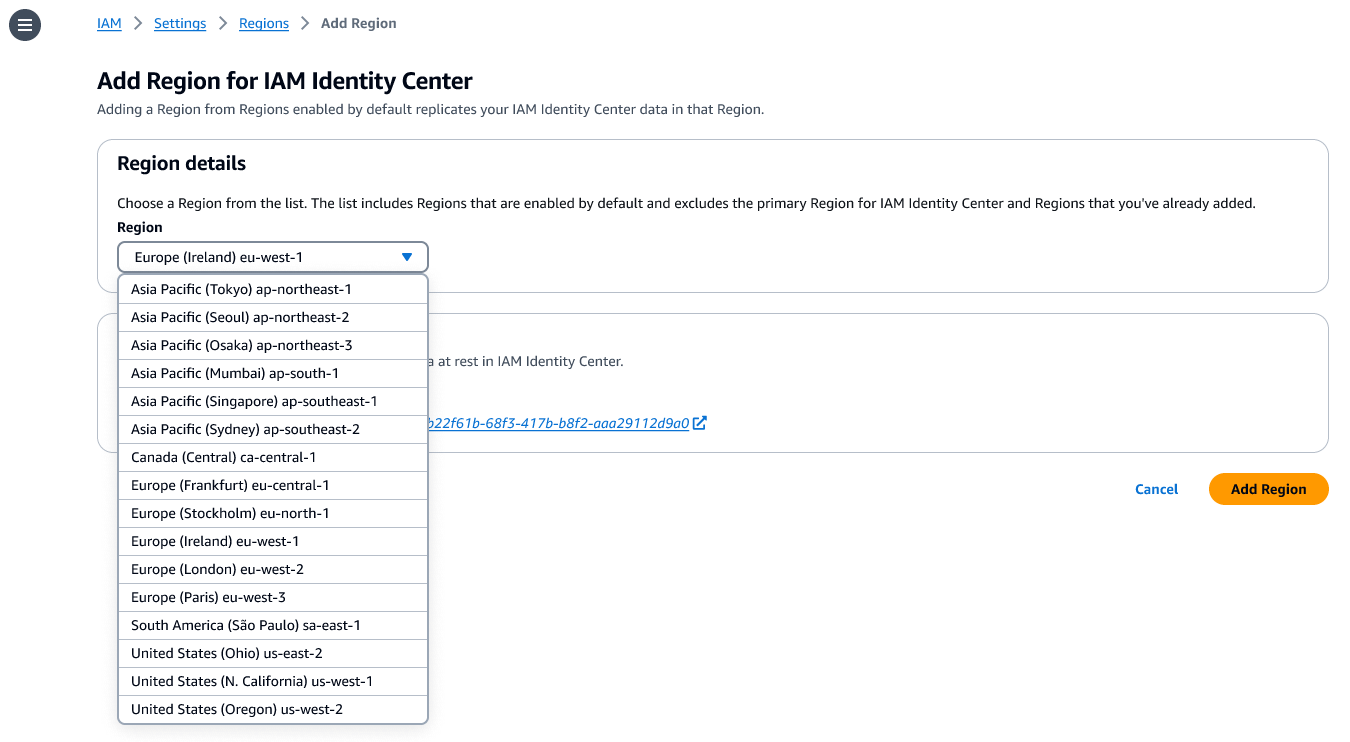
Select Add Area. This begins the preliminary replication whose length is determined by the dimensions of your Identification Middle occasion.
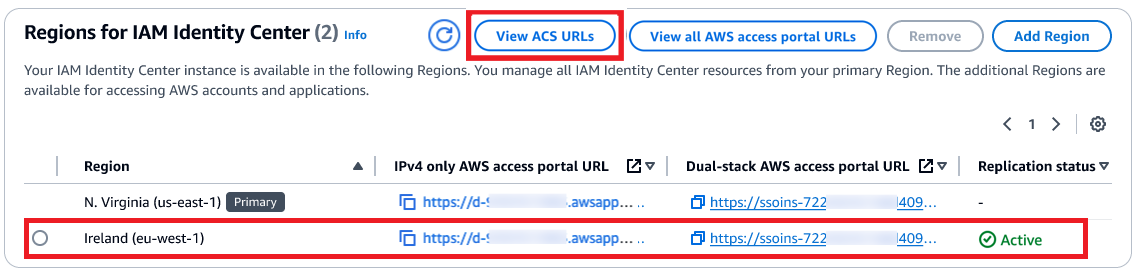
After the replication is accomplished, your customers can entry their AWS accounts and purposes on this new Area. Once you select View ACS URLs, you possibly can view SAML info, corresponding to an Assertion Client Service (ACS) URL, in regards to the major and extra Areas.
How your workforce can use an extra Area
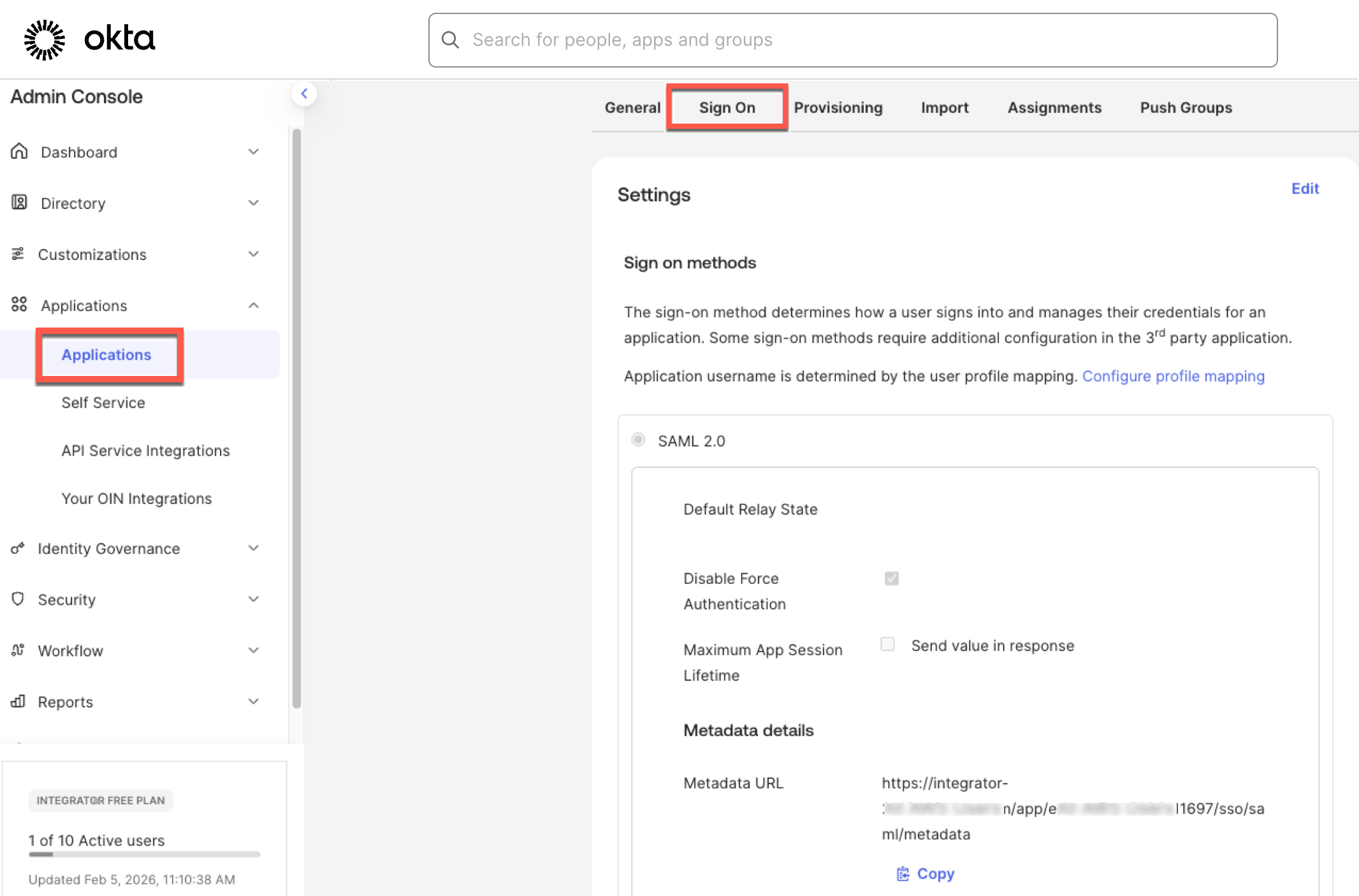
AWS Identification Middle helps SAML single sign-on with exterior IdPs, corresponding to Microsoft Entra ID and Okta. Upon authentication within the IdP, the person is redirected to the AWS entry portal. To allow the person to be redirected to the AWS entry portal within the newly added Area, you must add the extra Area’s ACS URL to the IdP configuration.
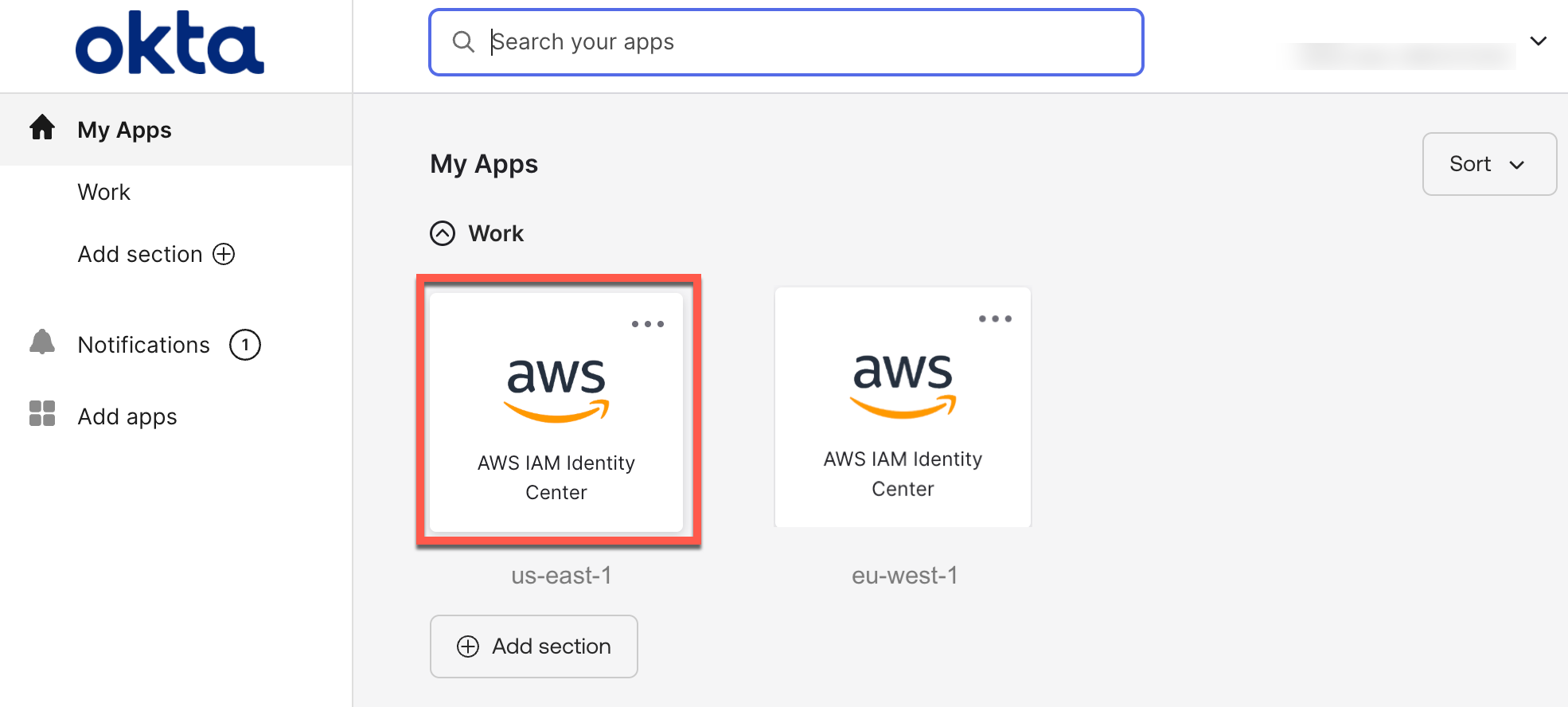
The next screenshots present you ways to do that within the Okta admin console:
Then, you possibly can create a bookmark software in your id supplier for customers to find the extra Area. This bookmark app capabilities like a browser bookmark and incorporates solely the URL to the AWS entry portal within the further Area.
It’s also possible to deploy AWS managed purposes in further Areas utilizing your current deployment workflows. Your customers can entry purposes or accounts utilizing the present entry strategies, such because the AWS entry portal, an software hyperlink, or by way of the AWS Command Line Interface (AWS CLI).
To study extra about which AWS managed purposes help deployment in further Areas, go to the IAM Identification Middle Person Information.
Issues to know
Listed below are key issues to find out about this characteristic:
- Consideration – To reap the benefits of this characteristic at launch, you should be utilizing a company occasion of IAM Identification Middle linked to an exterior IdP. Additionally, the first and extra Areas should be enabled by default in an AWS account. Account situations of IAM Identification Middle, and the opposite two id sources (Microsoft Energetic Listing and IAM Identification Middle listing) are presently not supported.
- Operation – The first Area stays the central place for managing workforce identities, account entry permissions, exterior IdP, and different configurations. You should use the IAM Identification Middle console in further Areas with a restricted characteristic set. Most operations are read-only, aside from software administration and person session revocation.
- Monitoring – All workforce actions are emitted in AWS CloudTrail within the Area the place the motion was carried out. This characteristic enhances account entry continuity. You’ll be able to arrange break-glass entry for privileged customers to entry AWS if the exterior IdP has a service disruption.
Now out there
AWS IAM Identification Middle multi-Area help is now out there within the 17 enabled-by-default business AWS Areas. For Regional availability and a future roadmap, go to the AWS Capabilities by Area. You should use this characteristic at no further value. Normal AWS KMS costs apply for storing and utilizing buyer managed keys.
Give it a strive within the AWS Identification Middle console. To study extra, go to the IAM Identification Middle Person Information and ship suggestions to AWS re:Put up for Identification Middle or by way of your ordinary AWS Help contacts.
— Channy
Up to date on February fifth — Mounted the Okta admin console screenshot.
