Constructing on the teachings realized within the Safety Operations Heart (SOC) at main occasions, we challenged ourselves to construct one thing new at Cisco Stay Amsterdam 2026, a closed-loop integration with Cisco XDR and Splunk Enterprise Safety.
Planning a profitable SOC begins with robust collaboration with the Community Operations Heart (NOC). It additionally started with a spotlight, utilizing the Splunk Safety Maturity Methodology (S2M2).
The core missions of the SOC stay:
- Defend: Safeguard the community from threats and assaults, each inner and exterior
- Educate: Inform and interact attendees via SOC excursions and weblog content material, and our white paper
- Innovate: Develop and implement new integrations, processes, workflows, and automations


Harnessing the Energy of Splunk Safety
A significant objective for EMEA 2026 was breaking down the silos between “triage / investigating” and “risk looking / incident response.”
By embedding Splunk Safety Integration Engineers instantly into the SOC, we curated particular workflows that allowed Tier 1 interns and Tier 2 analysts to carry out advanced investigations that had been beforehand the area of Tier 3 responders.
Configurations and different knowledge had been able to go from earlier occasions, together with dashboards in Splunk, from the improvements for the Nationwide Soccer League Tremendous Bowl LX SOC.
We refined the SOC Supervisor dashboard in Splunk from the expertise on the Tremendous Bowl SOC, exhibiting the Incidents generated from detections within the safety sources, and the standing of the incidents, together with escalations to Splunk Enterprise Safety (ES).


The Splunk Safety Product Labs staff labored to make the most of the ability of the Cisco XDR correlation engine, to convey Splunk ES Threat index logs as Sources into the XDR Information Analytics Platform. These logs had been correlated with different detections to provide Incidents for Triage and Investigation by Tier 1 /2 SOC analysts.


The mixing between Cisco XDR and Splunk ES delivers a seamless expertise for safety operations groups by combining native XDR detections with Splunk’s intensive knowledge backend and customized OCSF detections. Key improvements embrace:
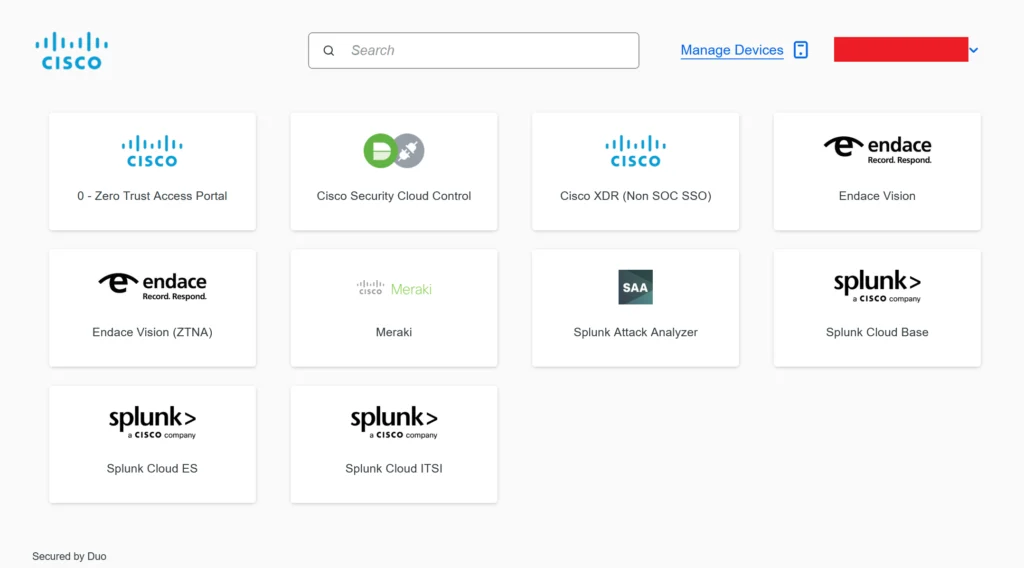
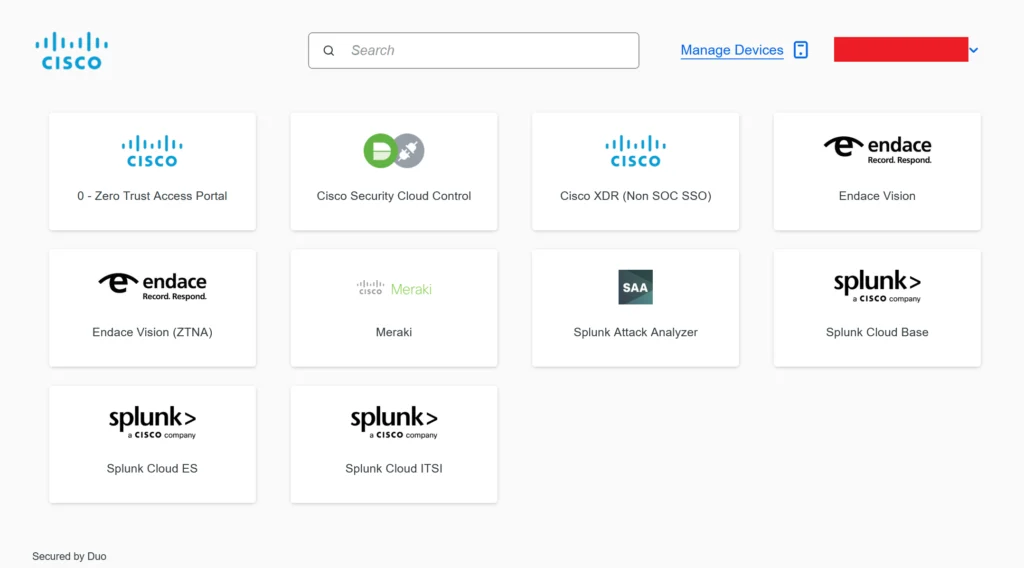
- Fast Onboarding: New SOC analysts might be skilled on XDR in underneath an hour, together with integration pivot factors with Splunk and Endace packet seize.
- Unified Incident Administration: Detections from each Cisco XDR and Splunk had been correlated inside XDR, permitting analysts to see the supply of detections in incidents, however sustaining a constant person expertise. This reduces the necessity for retraining earlier than effectiveness in a mature SOC.
- Environment friendly Analyst Workflow: Tier 1/2 analysts triaged and investigated incidents in XDR, with the flexibility to pivot to Splunk logs and Endace packet knowledge. When escalation is required, enriched incident knowledge is robotically despatched to Splunk ES for Tier 3 analysts to proceed investigations in Mission Management.
- Closed-Loop Automation: Incident standing was robotically up to date in XDR when the case was resolved in Splunk ES, closing the loop and making certain synchronized information.
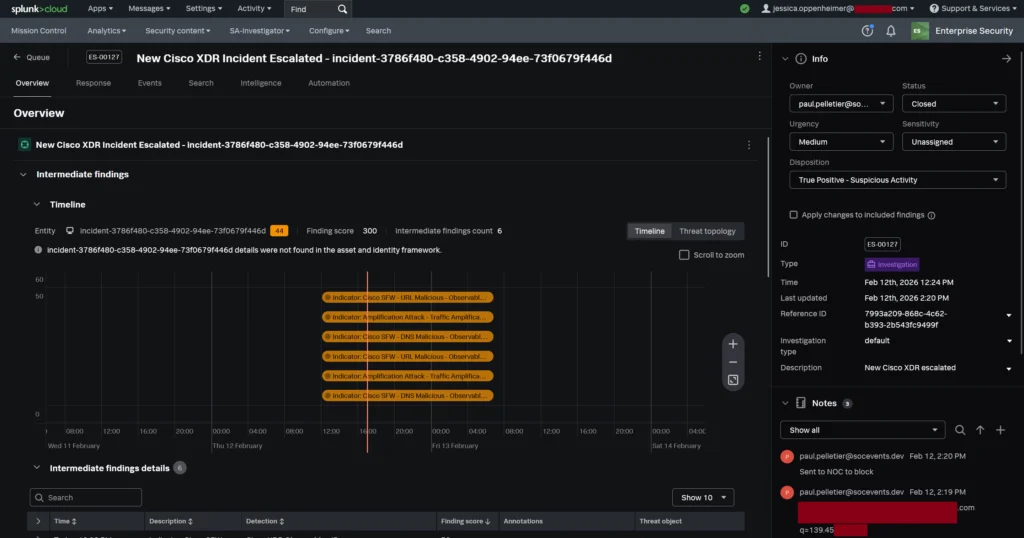
- Studying & Collaboration: Tier 1/2 analysts had position based mostly entry to Splunk ES through Duo Listing, empowering them to view the Tier 3 investigation notes and findings, and upleveling their expertise.
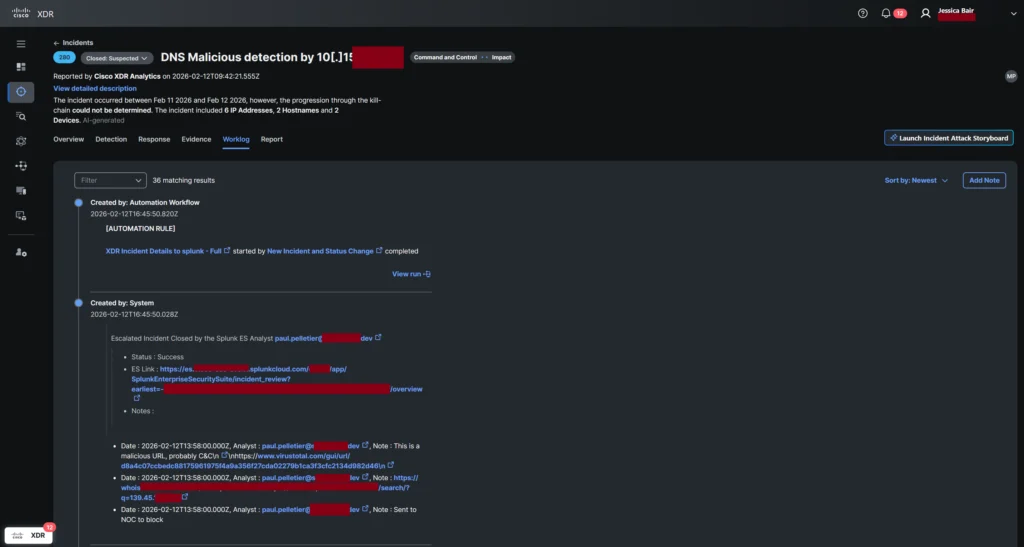
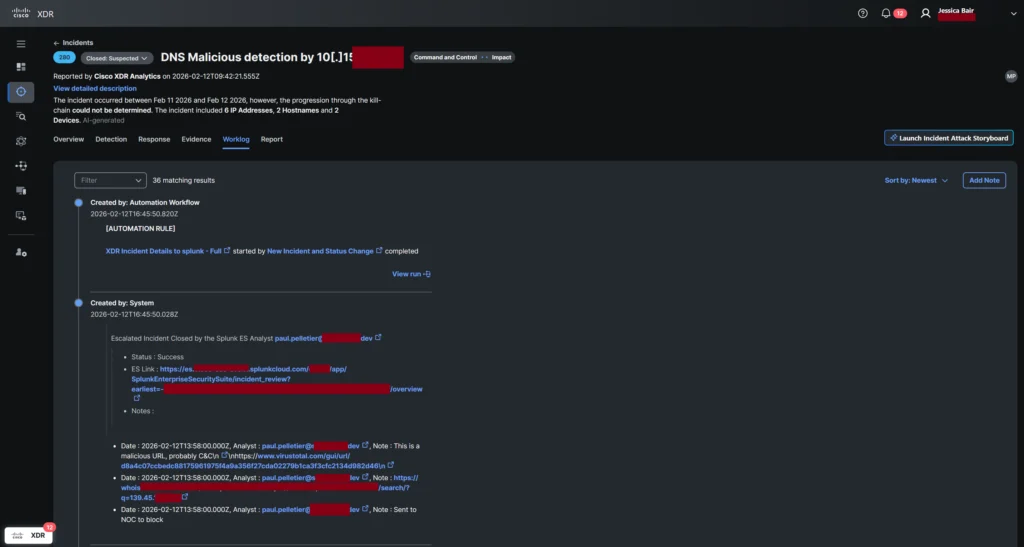
- Openness & Customization: The mixing leverages the open structure of each Cisco XDR and Splunk, supporting customized detections and versatile workflows, as confirmed in high-profile SOC deployments.
This innovation allows safety operations facilities to maximise detection protection, streamline incident response, scale back coaching overhead, and foster analyst progress, via tightly built-in, automated workflows.
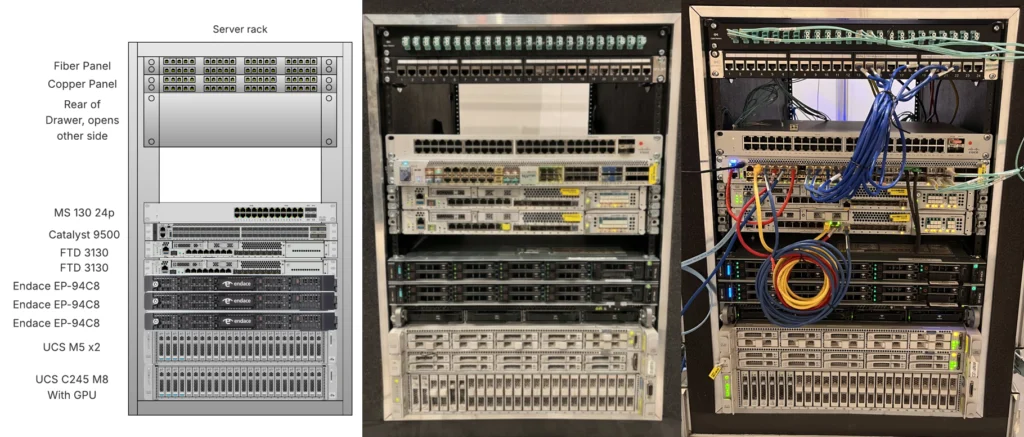
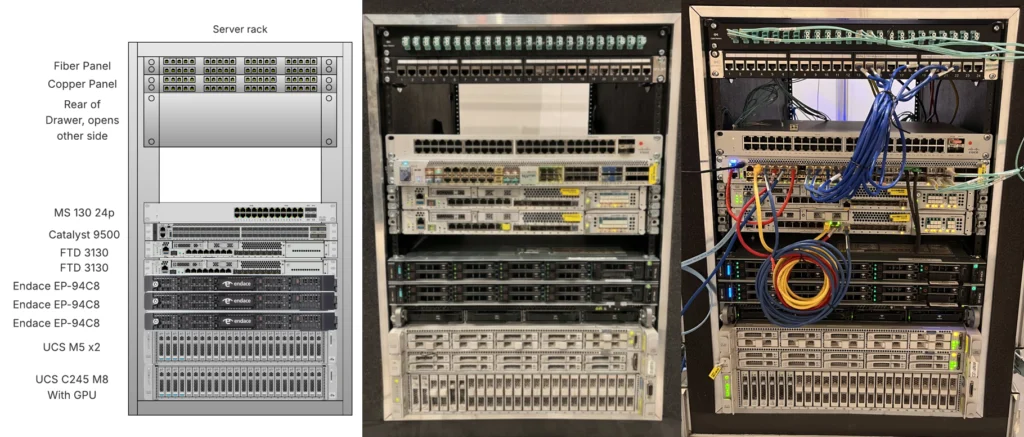
The Deployment: SOC in a Field
The SOC was efficiently deployed in simply 12 hours over 1 ½ days. This pace was not unintended; it was architectural. We utilized our moveable “SOC in a Field”, a pre-configured {hardware} stack designed to be delivered prematurely to the venue, related to the NOC and instantly started producing actionable telemetry.
Key elements enabling this fast setup included:
- Pre-validated Information Paths: Instantaneous connectivity between the Cisco Stay NOC, Splunk Enterprise Safety and the Cisco Safety Cloud.
- Battle-Examined Innovation: We built-in superior safety practices developed whereas safeguarding the Black Hat community, acknowledged because the world’s most hostile setting.
- Confirmed Workflows: We drew upon experience and playbooks refined on the Tremendous Bowl LX, RSAC, GovWare and prior Cisco Stay SOCs.
The SOC Structure: A “System of Techniques”
The Amsterdam SOC was designed to beat particular occasion constraints, akin to the lack to put in endpoint brokers on attendee units (BYOD) and the necessity to detect malware in encrypted visitors.
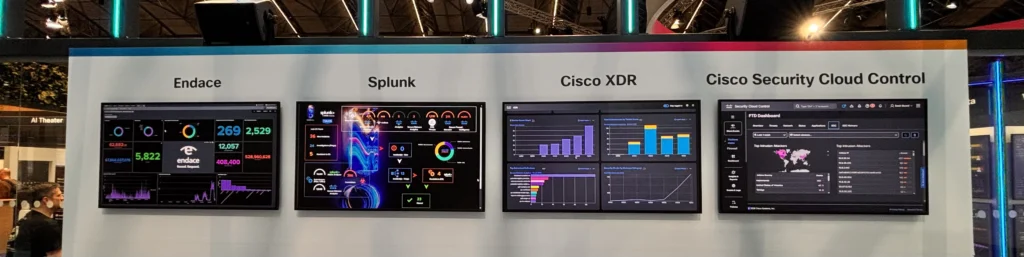
The Visibility Layer: The SOC staff labored with the NOC to attach the ‘SOC within the Field’ and Cisco Safe Entry for DNS safety. We obtained a Switched Port Analyzer (SPAN) feed of community visitors.
The Investigation Layer: We deployed the EndaceProbe packet seize platform to report all community visitors. This allowed us to pivot from a Splunk alert on to full packet seize (PCAP) to validate investigative hypotheses. Endace additionally generated Zeek logs for Splunk Enterprise Safety (ES), whereas file content material was reconstructed on the wire and streamed to Splunk Assault Analyzer and Cisco Safe Malware Analytics for sandboxing.
The Evaluation & Identification Layer:
- Splunk Cloud and Splunk ES served because the SOC platform, aggregating danger scores and normalizing knowledge into the Widespread Info Mannequin (CIM).
- Cisco XDR acted as investigation visualization instrument, utilizing AI to substantiate threats quicker with Instantaneous Assault Verification, enriched with risk intelligence supplied by Cisco Talos, and licenses donated by alphaMountain, Pulsedive, and StealthMole, together with neighborhood sources.
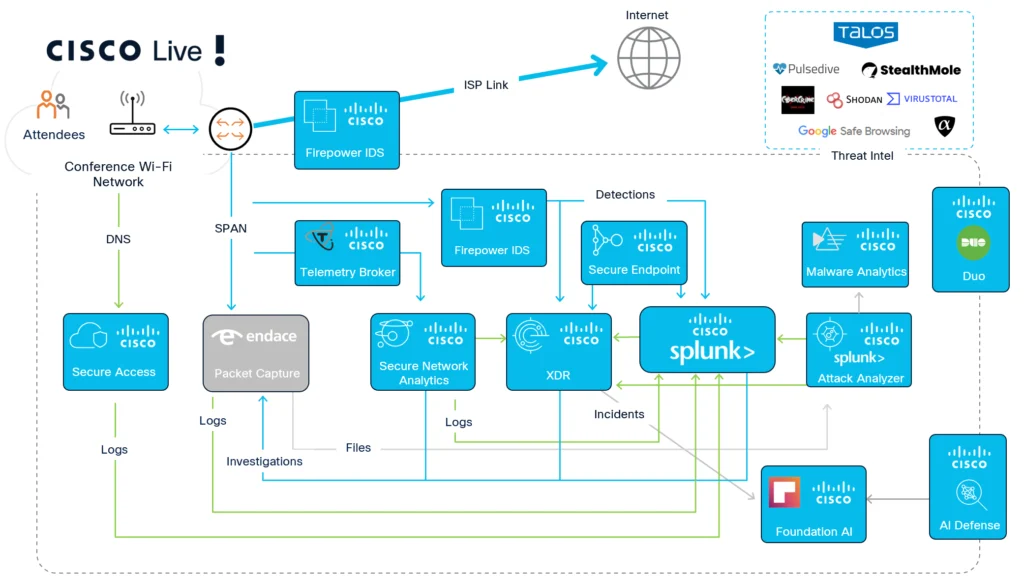
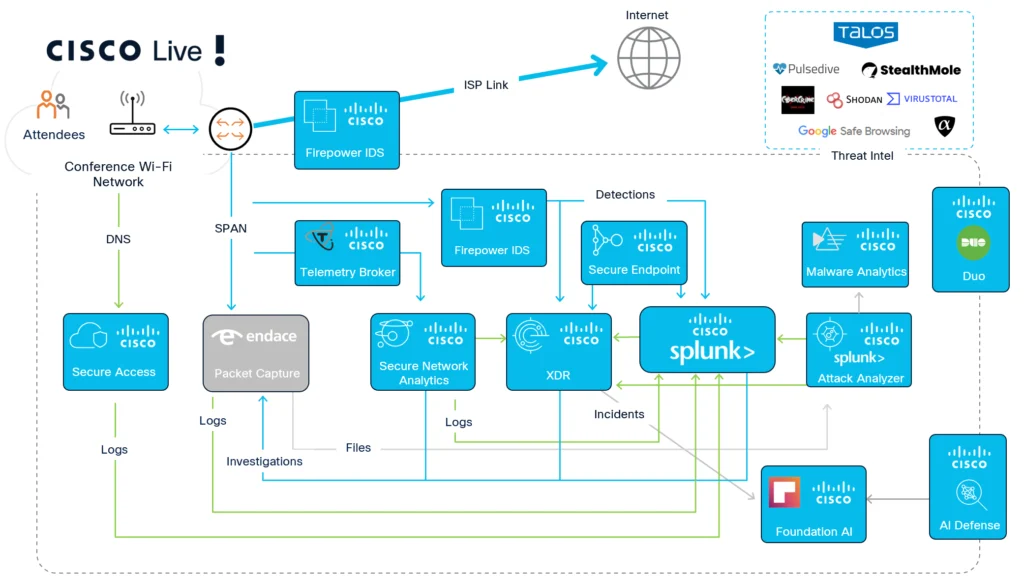
- Duo Listing and Identification Intelligence supplied the id aircraft, securing entry to our instruments through Single Signal-On and making certain our analysts had been authenticated and licensed inside minutes of becoming a member of the shift.
The Statistics
Statistics are all the time a preferred a part of the SOC Excursions. Under are the stats from this 12 months’s occasion.
| 12 months | 2026 |
| Attendees (Cisco Stay) | 21,000 |
| Complete packets captured (Endace) | 130 billion |
| Complete logs captured (Splunk) | 6.96 billion |
| Complete classes (Endace) | 911.3 million |
| Complete distinctive units (Endace in Splunk) | 32,434 |
| Complete packets written to disk (Endace) | 120 TBs |
| Complete logs written to cloud (Splunk) | 3.233 TBs |
| Peak bandwidth utilization (Endace) | 7 Gbps |
| DNS Requests (Cisco Safe Entry) | 105 million / 29.3k blocked |
| Complete clear textual content username/passwords (Endace) |
5,634 |
| Distinctive units / accounts with clear textual content usernames / passwords (Endace) |
575 |
| Recordsdata despatched for malware evaluation (Endace) | – 1.7m file objects reconstructed by Endace. – 55,471 despatched to Splunk Assault Analyzer – 45,514 despatched to Safe Malware Analytics |


SOC Findings and Classes Realized
The SOC staff focuses on steady innovation—the “OODA loop” of observing, orienting, deciding, and performing. We take time to doc our experiences for the edification of the neighborhood.
Try the deep-dive technical blogs beneath from the engineers who labored contained in the SOC:
Acknowledgements
A heartfelt thanks to the engineers whose experience made the primary Cisco Stay Amsterdam 2026 SOC an amazing success.


Community Operations Heart Liaisons
- Remco Kamerman, Luke Hebditch, Mark Bremner and Scott Neuman
Cisco Safety and Splunk SOC Staff
- SOC in a Field: Adi Sankar
- Splunk Safety Integrations: Paul Pelletier and Kenneth Bouchard, with Josh Wilson and Duane Waddle
- Splunk Menace Researchers: Nasreddine Bencherchali and Paul Pang
- Breach Safety Suite: Mark Pleunes, Ibrahim Yusuf, Piotr Jarzynka, Matt Vander Horst, Yannis Steiakogiannakis and Eric Rennie, with Bilal Qamar
- Consumer Safety Suite: Aaron Woland
- Firewall and Safety Cloud Management: Adam Kilgore and Christopher Grabowski
Endace SOC Staff
- Co-SOC Chief: Cary Wright Endace Engineering: Owen Gallagher, Sundarram Paravastu and Sam Brockelsby
We’d love to listen to what you assume! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media