The Amazon SageMaker lakehouse structure has expanded its tag-based entry management (TBAC) capabilities to incorporate federated catalogs. This enhancement extends past the default AWS Glue Information Catalog sources to embody Amazon S3 Tables, Amazon Redshift information warehouses. TBAC can also be supported on federated catalogs from information sources Amazon DynamoDB, MySQL, PostgreSQL, SQL Server, Oracle, Amazon DocumentDB, Google BigQuery, and Snowflake. TBAC gives you a classy permission administration that makes use of tags to create logical groupings of catalog sources, enabling directors to implement fine-grained entry controls throughout their whole information panorama with out managing particular person resource-level permissions.
Conventional information entry administration usually requires guide project of permissions on the useful resource stage, creating vital administrative overhead. TBAC solves this by introducing an automatic, inheritance-based permission mannequin. When directors apply tags to information sources, entry permissions are mechanically inherited, eliminating the necessity for guide coverage modifications when new tables are added. This streamlined strategy not solely reduces administrative burden but in addition enhances safety consistency throughout the information ecosystem.
TBAC may be arrange by the AWS Lake Formation console, and accessible utilizing Amazon Redshift, Amazon Athena, Amazon EMR, AWS Glue, and Amazon SageMaker Unified Studio. This makes it priceless for organizations managing advanced information landscapes with a number of information sources and enormous datasets. TBAC is particularly useful for enterprises implementing information mesh architectures, sustaining regulatory compliance, or scaling their information operations throughout a number of departments. Moreover, TBAC permits environment friendly information sharing throughout totally different accounts, making it simpler to keep up safe collaboration.
On this publish, we illustrate tips on how to get began with fine-grained entry management of S3 Tables and Redshift tables within the lakehouse utilizing TBAC. We additionally present tips on how to entry these lakehouse tables utilizing your selection of analytics companies, comparable to Athena, Redshift, and Apache Spark in Amazon EMR Serverless in Amazon SageMaker Unified Studio.
Resolution overview
For illustration, we take into account a fictional firm referred to as Instance Retail Corp, as lined within the weblog publish Speed up your analytics with Amazon S3 Tables and Amazon SageMaker Lakehouse. Instance Retail’s management has determined to make use of the SageMaker lakehouse structure to unify information throughout S3 Tables and their Redshift information warehouse. With this lakehouse structure, they will now conduct analyses throughout their information to determine at-risk prospects, perceive the affect of personalised advertising campaigns on buyer churn, and develop focused retention and gross sales methods.
Alice is an information administrator with the AWS Identification and Entry Administration (IAM) function LHAdmin in Instance Retail Corp, and he or she desires to implement tag-based entry management to scale permissions throughout their information lake and information warehouse sources. She is utilizing S3 Tables with Iceberg transactional functionality to realize scalability as updates are streamed throughout billions of buyer interactions, whereas offering the identical sturdiness, availability, and efficiency traits that S3 is understood for. She already has a Redshift namespace, which comprises historic and present information about gross sales, prospects prospects, and churn info. Alice helps an prolonged workforce of builders, engineers, and information scientists who require entry to the information atmosphere to develop enterprise insights, dashboards, ML fashions, and data bases. This workforce consists of:
- Bob, an information steward with IAM function
DataSteward, is the area proprietor and manages entry to the S3 Tables and warehouse information. He permits different groups who construct experiences to be shared with management. - Charlie, an information analyst with IAM function
DataAnalyst, builds ML forecasting fashions for gross sales progress utilizing the pipeline or buyer conversion throughout a number of touchpoints, and makes these accessible to finance and planning groups. - Doug, a BI engineer with IAM function
BIEngineer, builds interactive dashboards to funnel buyer prospects and their conversions throughout a number of touchpoints, and makes these accessible to hundreds of gross sales workforce members.
Alice decides to make use of the SageMaker lakehouse structure to unify information throughout S3 Tables and Redshift information warehouse. Bob can now convey his area information into one place and handle entry to a number of groups requesting entry to his information. Charlie can shortly construct Amazon QuickSight dashboards and use his Redshift and Athena experience to offer fast question outcomes. Doug can construct Spark-based processing with AWS Glue or Amazon EMR to construct ML forecasting fashions.
Alice’s objective is to make use of TBAC to make fine-grained entry rather more scalable, as a result of they will grant permissions on many sources without delay and permissions are up to date accordingly when tags for sources are added, modified, or eliminated.The next diagram illustrates the answer structure.
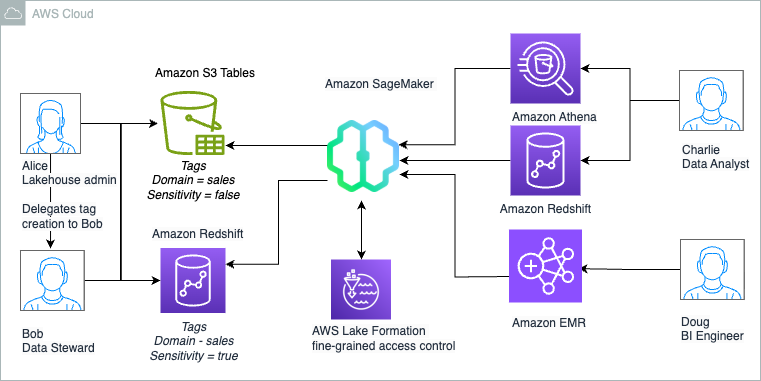
Alice as Lakehouse admin and Bob as Information Steward determines that following high-level steps are wanted to deploy the answer:
- Create an S3 Tables bucket and allow integration with the Information Catalog. This may make the sources accessible underneath the federated catalog
s3tablescatalogwithin the lakehouse structure with Lake Formation for entry management. Create a namespace and a desk underneath the desk bucket the place the information will likely be saved. - Create a Redshift cluster with tables, publish your information warehouse to the Information Catalog, and create a catalog registering the namespace. This may make the sources accessible underneath a federated catalog within the lakehouse structure with Lake Formation for entry management.
- Delegate permissions to create tags and grant permissions on Information Catalog sources to
DataSteward. - As
DataSteward, outline tag ontology based mostly on the use case and create Tags. Assign these LF-Tags to the sources (database or desk) to logically group lakehouse sources for sharing based mostly on entry patterns. - Share the S3 Tables catalog desk and Redshift desk utilizing tag-based entry management to
DataAnalyst, who makes use of Athena for evaluation and Redshift Spectrum for producing the report. - Share the S3 Tables catalog desk and Redshift desk utilizing tag-based entry management to
BIEngineer, who makes use of Spark in EMR Serverless to additional course of the datasets.
Information steward defines the tags and project to sources as proven:
| Tags | Information Assets |
|
Area = gross sales Sensitivity = false |
S3 Desk: buyer( c_salutation, c_preferred_cust_flag,c_first_sales_date_sk, |
|
Area = gross sales Sensitivity = true |
S3 Desk: buyer( c_first_name, c_last_name, c_email_address, c_birth_year) |
|
Area = gross sales Sensitivity = false |
Redshift Desk: gross sales.store_sales |
The next desk summarizes the tag expression that’s granted to roles for useful resource entry:
| Person | Persona | Permission Granted | Entry |
| Bob | DataSteward | SUPER_USER on catalogs | Admin entry on buyer and store_sales. |
| Charlie | DataAnalyst |
Area = gross sales Sensitivity = false |
Entry to non -sensitive information that’s aligned to gross sales area: buyer(non-sensitive columns) and store_sales. |
| Doug | BIEngineer | Area = gross sales | Entry to all datasets that’s aligned to gross sales area: buyer and store_sales. |
Stipulations
To observe together with this publish, full the next prerequisite steps:
- Have an AWS account and admin consumer with entry to the next AWS companies:
- Athena
- Amazon EMR
- IAM
- Lake Formation and the Information Catalog
- Amazon Redshift
- Amazon S3
- IAM Identification Heart
- Amazon SageMaker Unified Studio
- Create an information lake admin (
LHAdmin). For directions, see Create an information lake administrator. - Create an IAM function named
DataStewardand fix permissions for AWS Glue and Lake Formation entry. For directions, seek advice from Information lake administrator permissions. - Create an IAM function named
DataAnalystand fix permissions for Amazon Redshift and Athena entry. For directions, seek advice from Information analyst permissions. - Create an IAM function named
BIEngineerand fix permissions for Amazon EMR entry. That is additionally the EMR runtime function that the Spark job will use to entry the tables. For directions on the function permissions, seek advice from Job runtime roles for EMR serverless. - Create an IAM function named
RedshiftS3DataTransferRolefollowing the directions in Stipulations for managing Amazon Redshift namespaces within the AWS Glue Information Catalog. - Create an EMR Studio and fix an EMR Serverless namespace in a non-public subnet to it, following the directions in Run interactive workloads on Amazon EMR Serverless from Amazon EMR Studio.
Create information lake tables utilizing an S3 Tables bucket and combine with the lakehouse structure
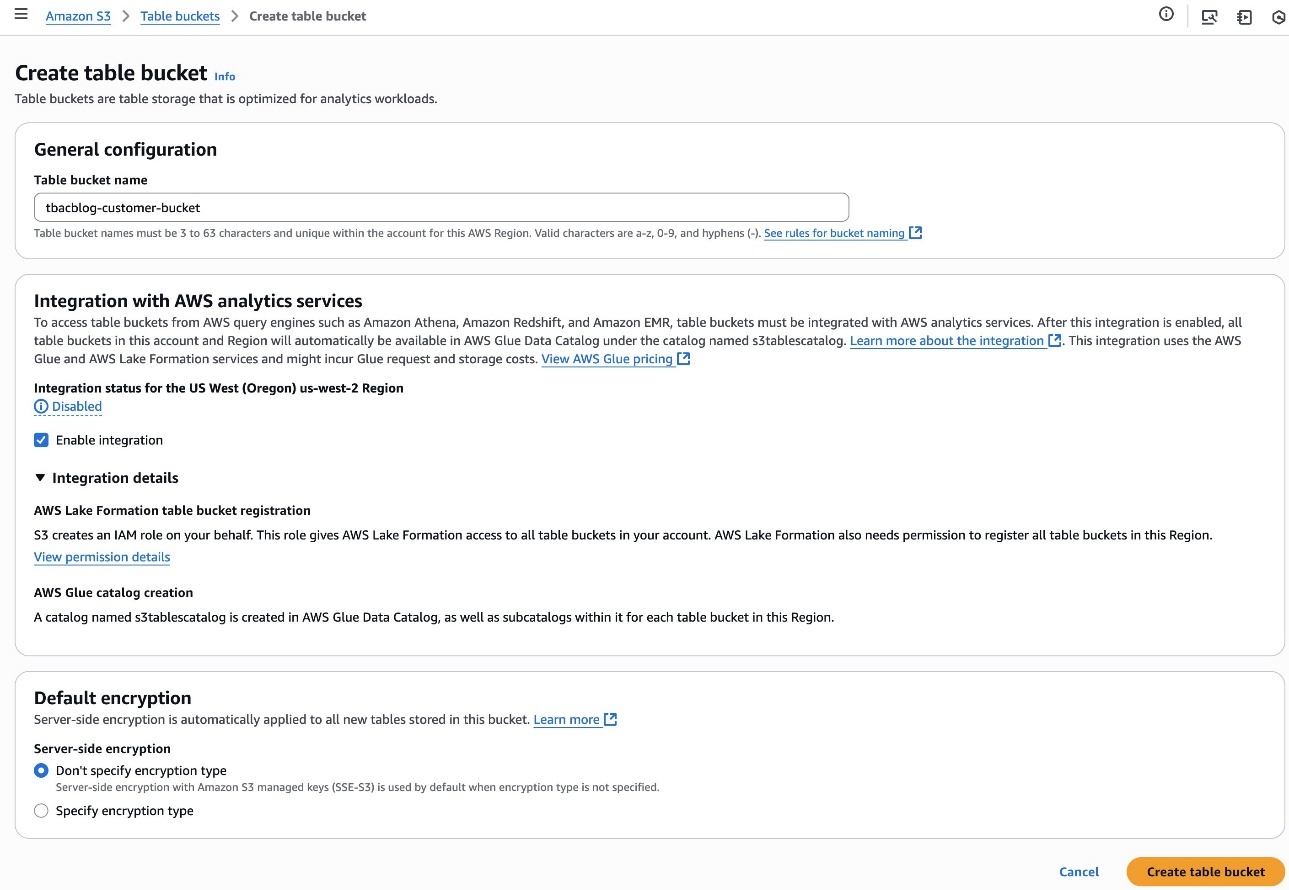
Alice completes the next steps to create a desk bucket and allow integration with analytics companies:
- Register to the Amazon S3 console as
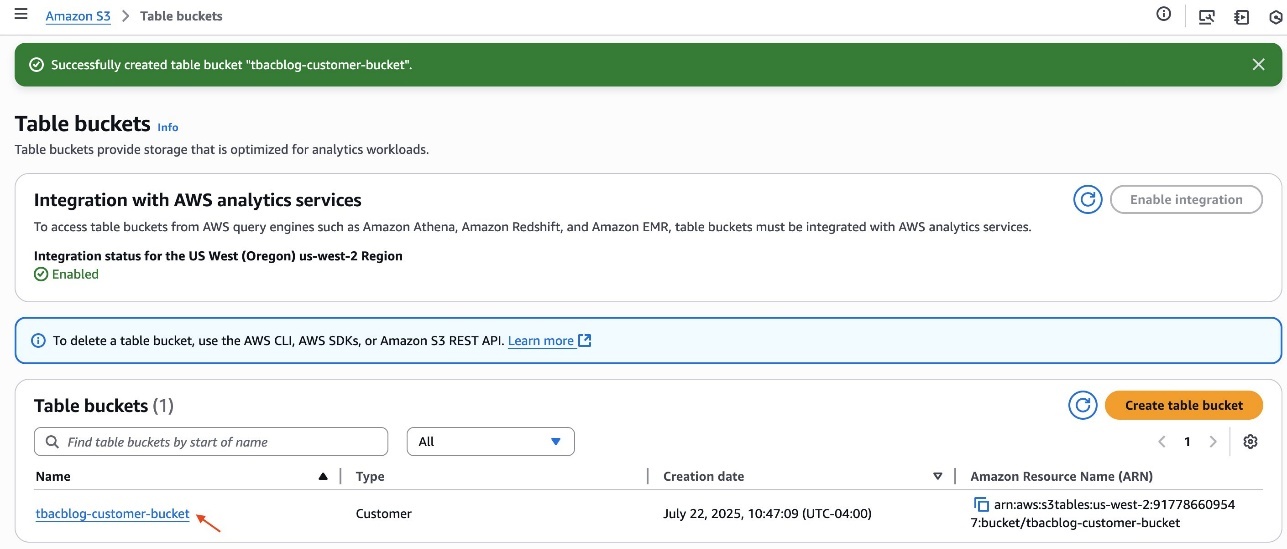
LHAdmin. - Select Desk buckets within the navigation pane and create a desk bucket.
- For Desk bucket identify, enter a reputation, comparable to
tbacblog-customer-bucket. - For Integration with AWS analytics companies, select Allow integration.
- Select Create desk bucket.
- After you create the desk, click on the hyperlink of the desk bucket identify.
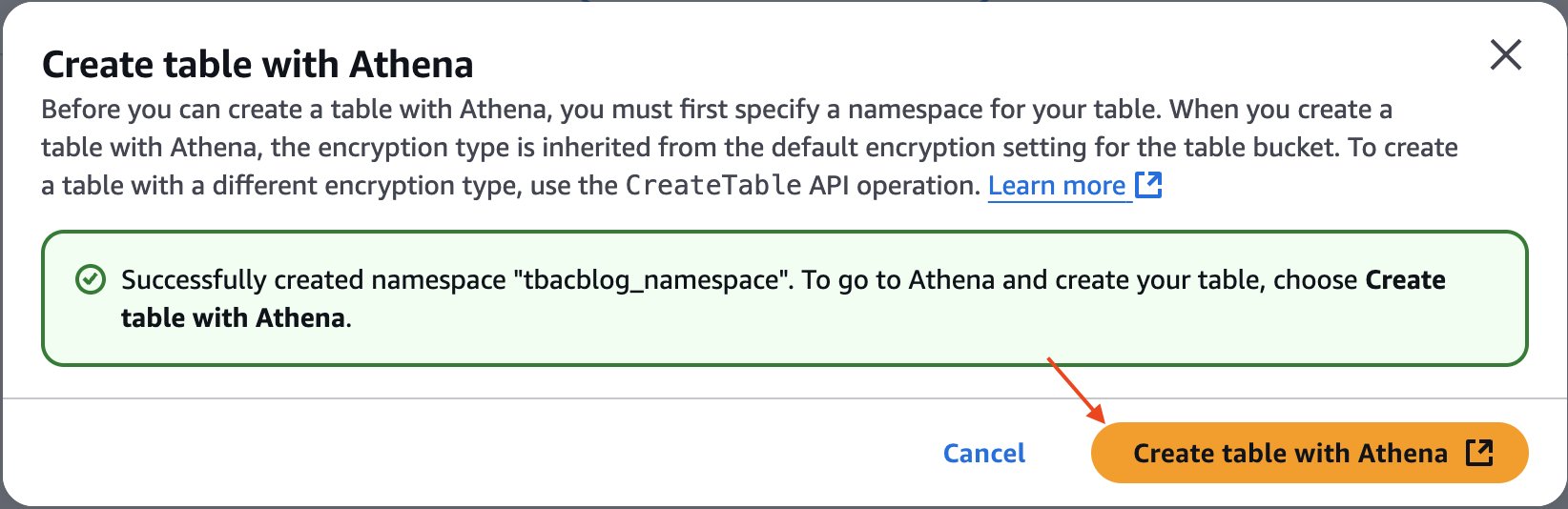
- Select Create desk with Athena.
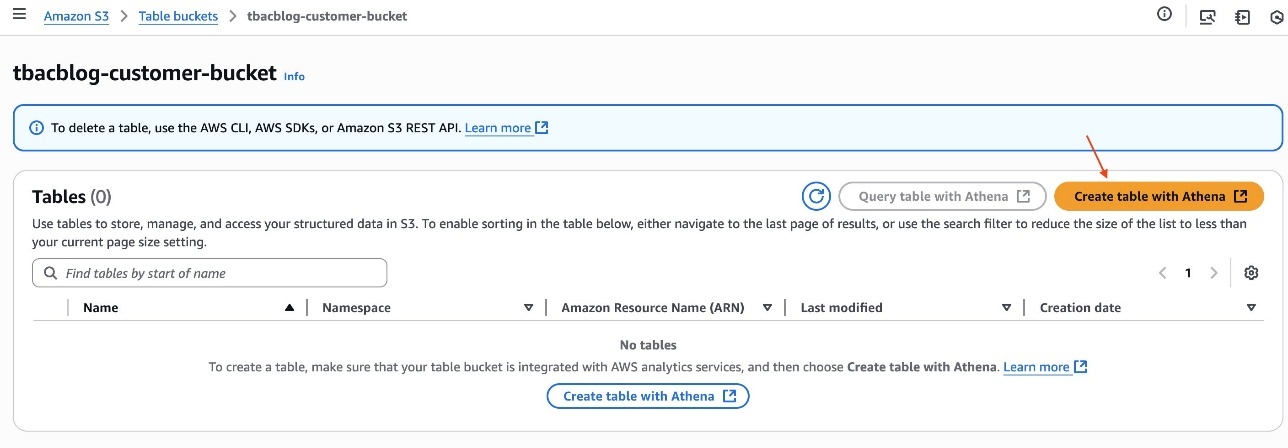
- Create a namespace and supply a namespace identify. For instance,
tbacblog_namespace. - Select Create namespace.
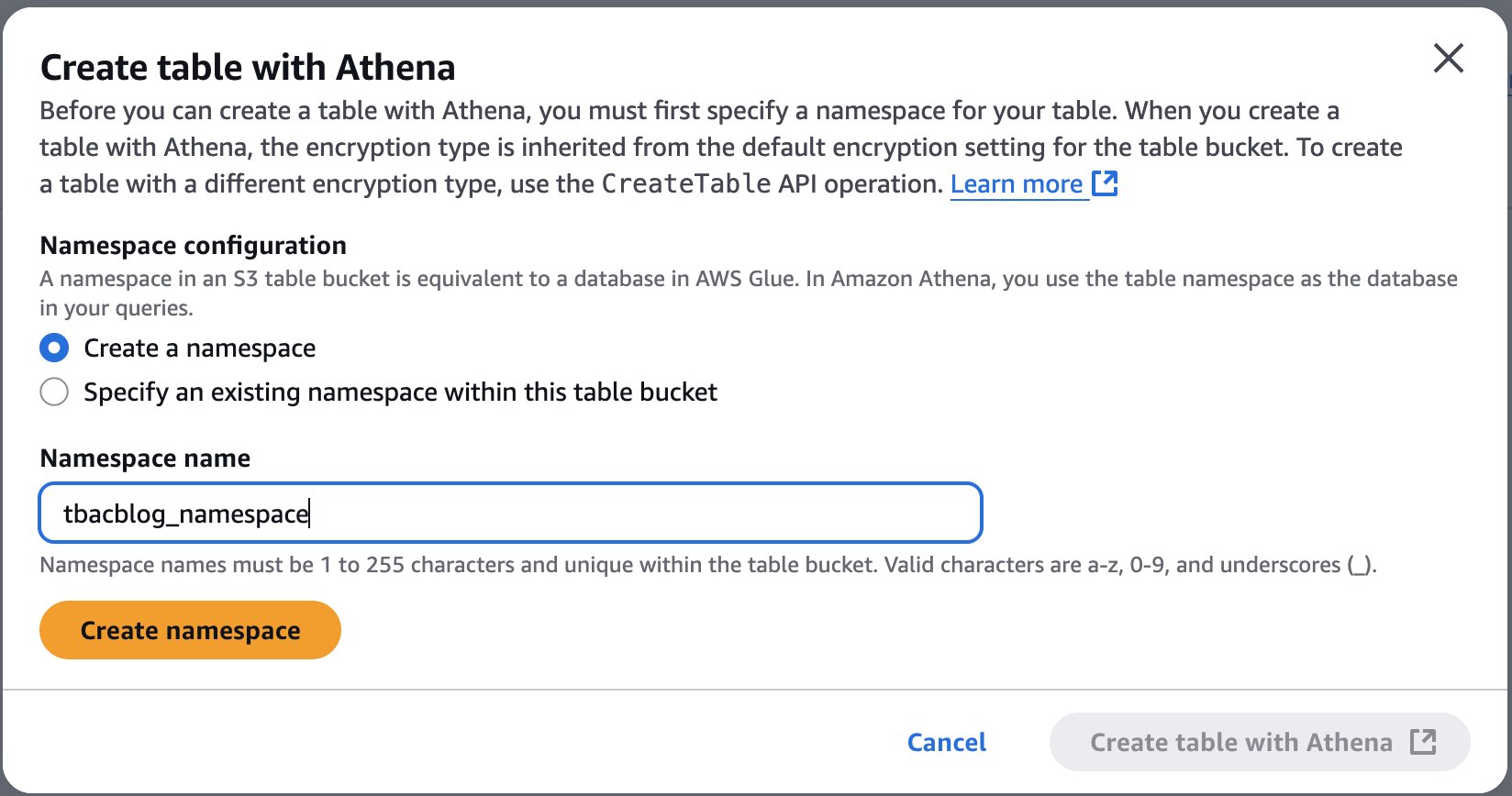
- Now proceed to creating desk schema and populating it by selecting Create desk with Athena.
- On the Athena console, run the next SQL script to create a desk:
You will have now created the S3 Tables desk buyer, populated it with information, and built-in it with the lakehouse structure.
Arrange information warehouse tables utilizing Amazon Redshift and combine them with the lakehouse structure
On this part, Alice units up information warehouse tables utilizing Amazon Redshift and integrates them with the lakehouse structure.
Create a Redshift cluster and publish it to the Information Catalog
Alice completes the next steps to create a Redshift cluster and publish it to the Information Catalog:
- Create a Redshift Serverless namespace referred to as
salescluster. For directions, seek advice from Get began with Amazon Redshift Serverless information warehouses. - Register to the Redshift endpoint
salesclusteras an admin consumer. - Run the next script to create a desk underneath the
devdatabase underneath thepublicschema: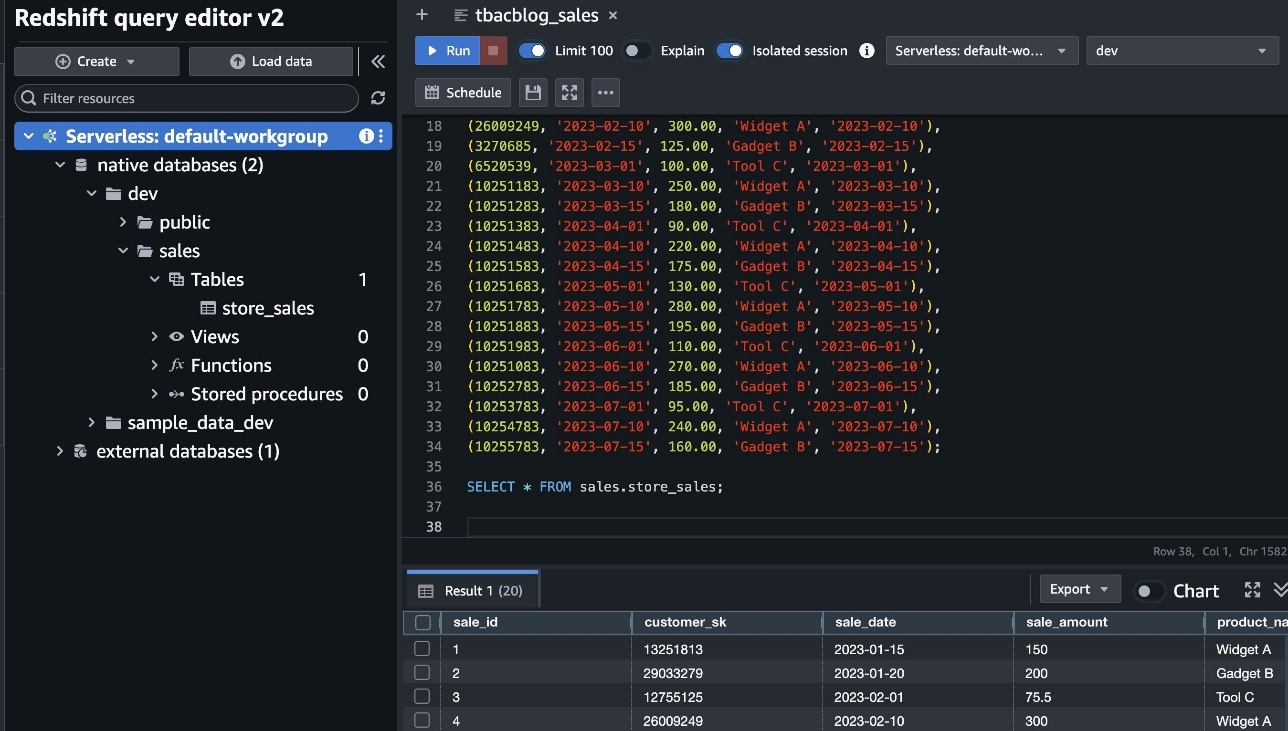
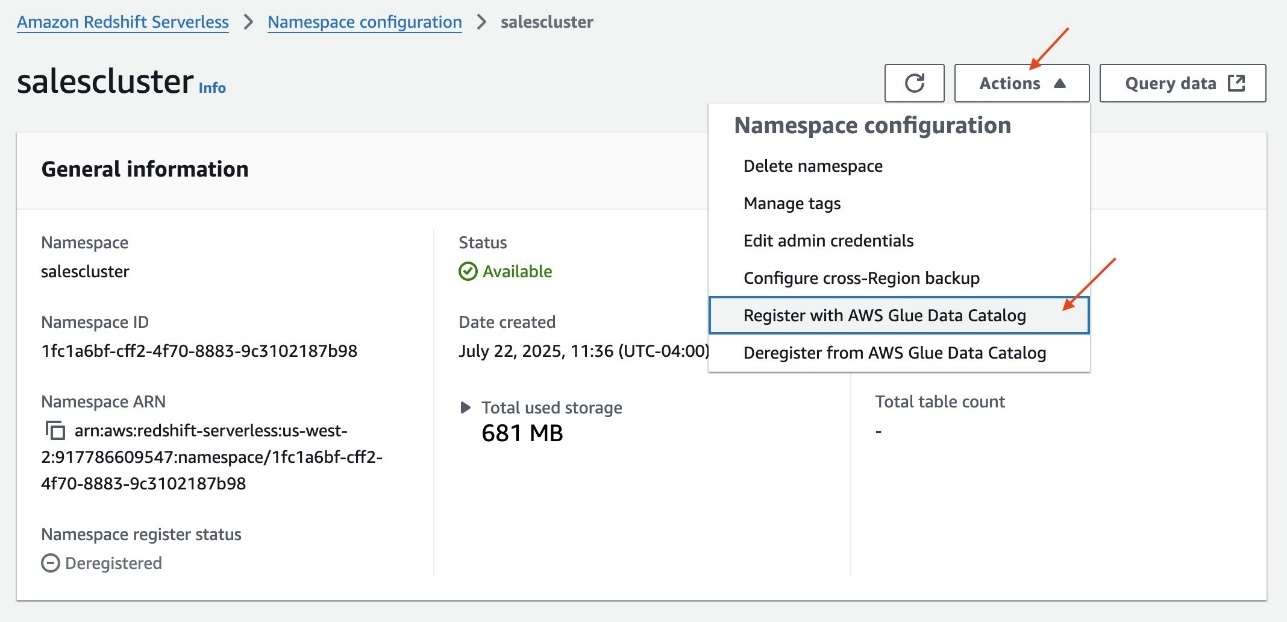
- On the Redshift Serverless console, open the namespace.
- On the Actions dropdown menu, select Register with AWS Glue Information Catalog to combine with the lakehouse structure.
- Choose the identical AWS account and select Register.
Create a catalog for Amazon Redshift
Alice completes the next steps to create a catalog for Amazon Redshift:
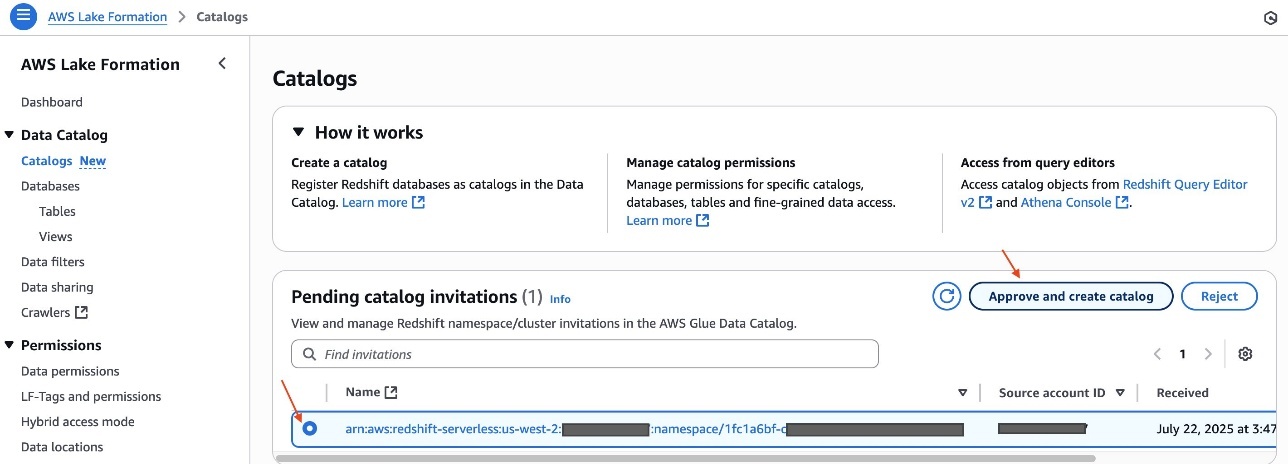
- Register to the Lake Formation console as the information lake administrator
LHAdmin. - Within the navigation pane, underneath Information Catalog, select Catalogs.
Underneath Pending catalog invites, you will note the invitation initiated from the Redshift Serverless namespacesalescluster. - Choose the pending invitation and select Approve and create catalog.
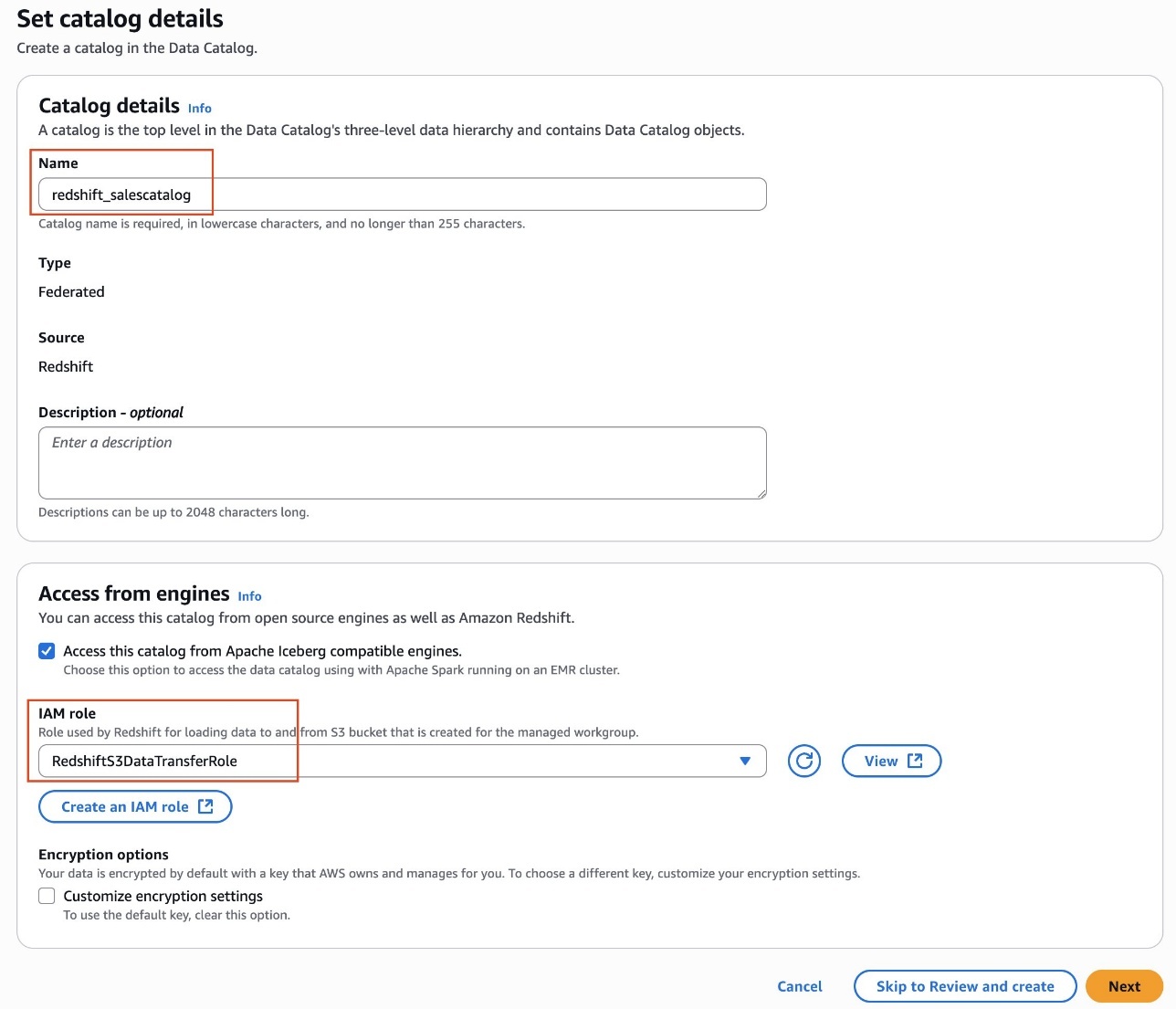
- Present a reputation for the catalog. For instance,
redshift_salescatalog. - Underneath Entry from engines, choose Entry this catalog from Iceberg-compatible engines and select
RedshiftS3DataTransferRolefor IAM function. - Select Subsequent.
- Select Add permissions.
- Underneath Principals, select the
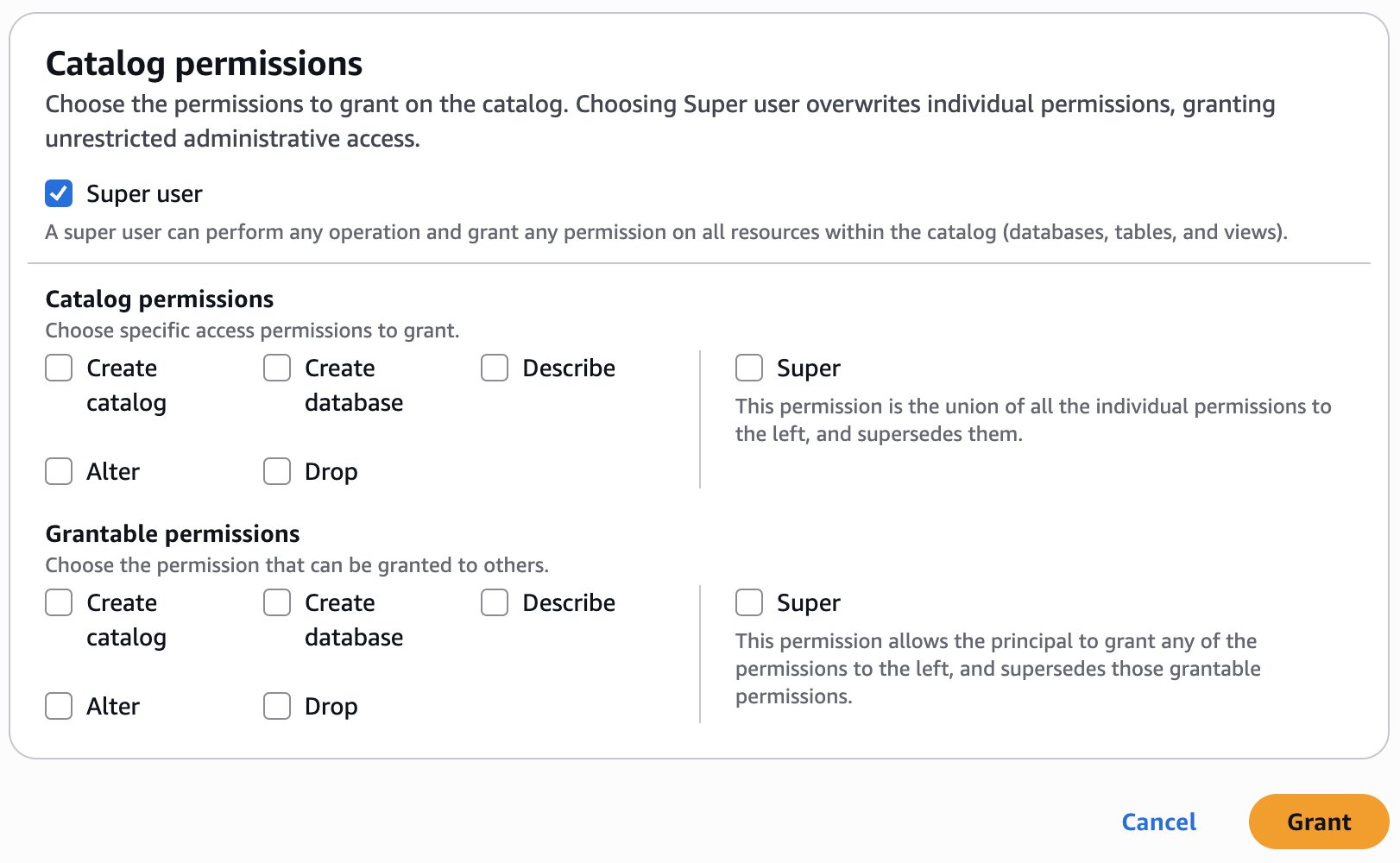
LHAdminfunction for IAM customers and roles, select Tremendous consumer for Catalog permissions, and select Add.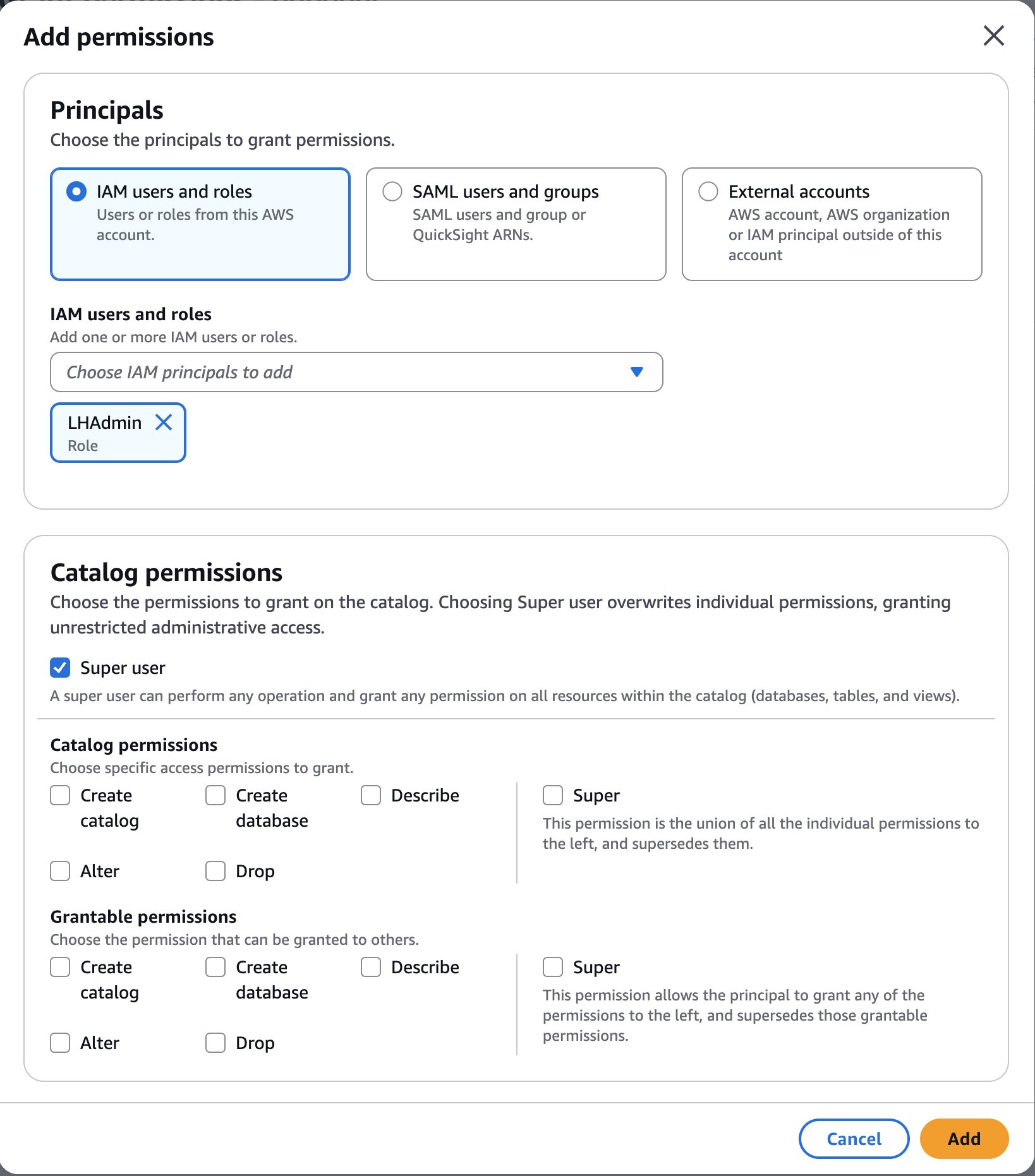
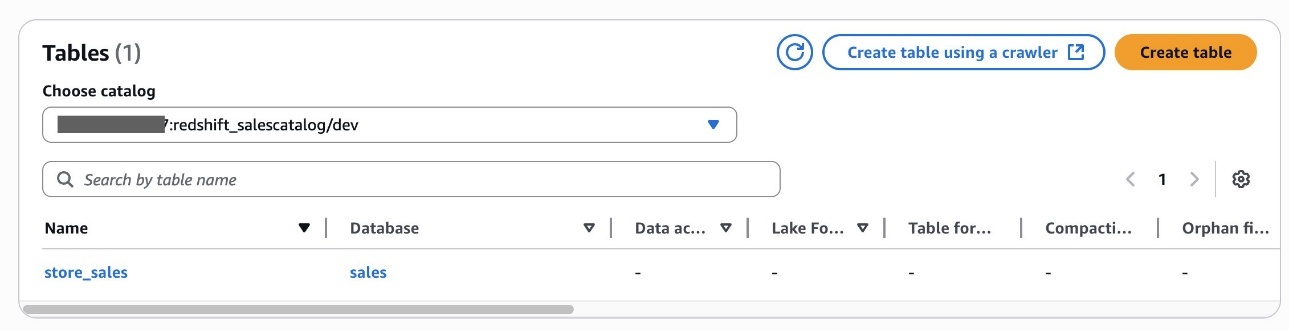
- Select Create catalog.After you create the catalog
redshift_salescatalog, you may examine the sub-catalogdev, namespace and databasegross sales, and deskstore_salesbeneath it.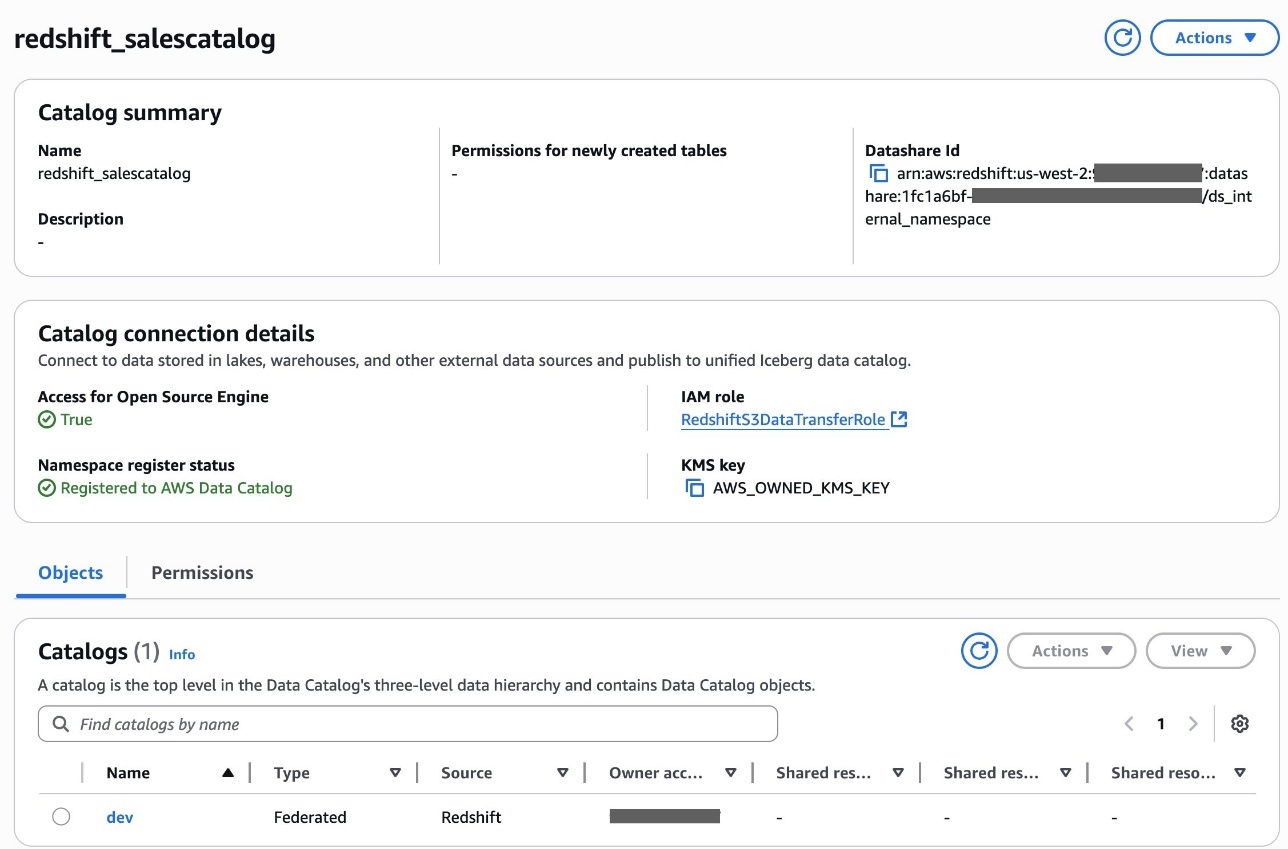
Alice has now accomplished creating an S3table catalog desk and Redshift federated catalog desk within the Information Catalog.
Delegate LF-Tags creation and useful resource permission to the DataSteward function
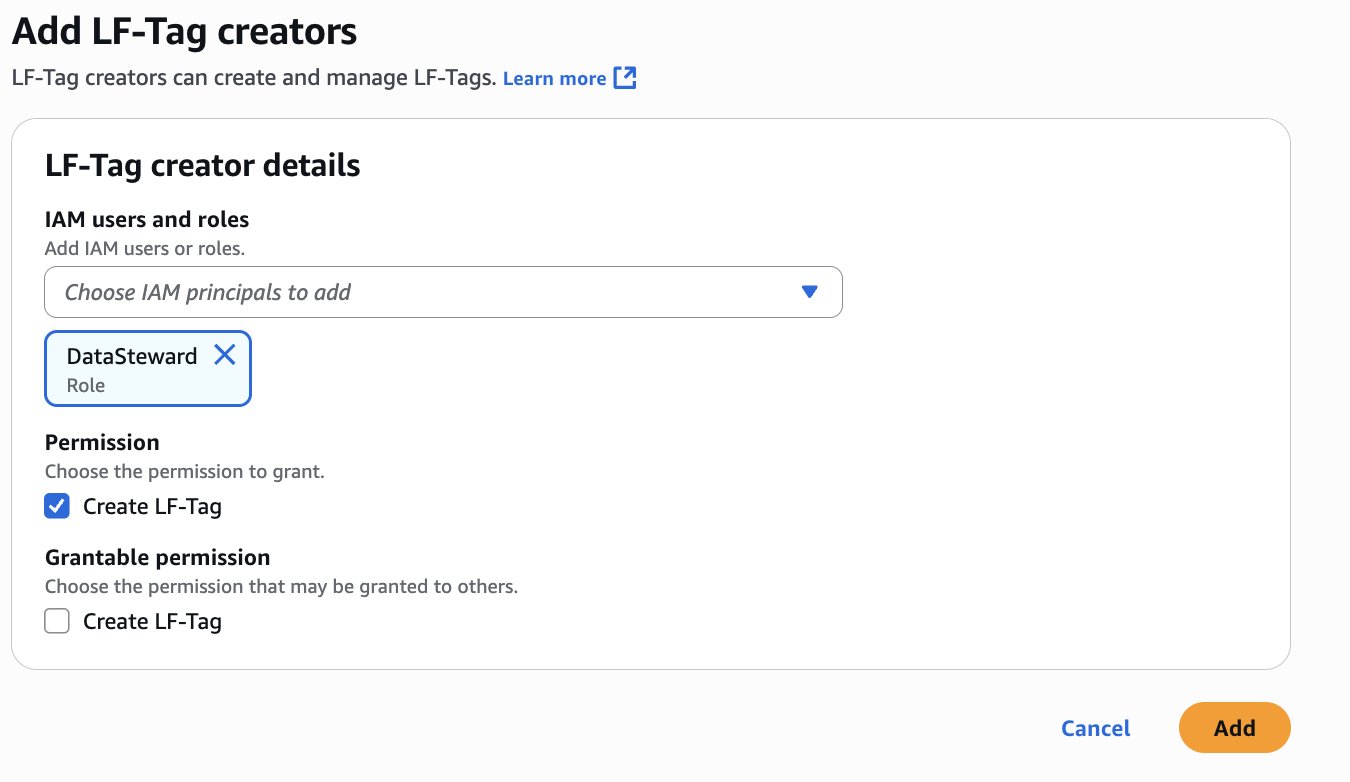
Alice completes the next steps to delegate LF-Tags creation and useful resource permission to Bob as DataSteward:
- Register to the Lake Formation console as the information lake administrator
LHAdmin. - Within the navigation pane, select LF Tags and permissions, then select the LF-Tag creators tab.
- Select Add LF-Tag creators.
- Select DataSteward for IAM customers and roles.
- Underneath Permission, choose Create LF-Tag and select Add.
- Within the navigation pane, select Information permissions, then select Grant.
- Within the Principals part, for IAM customers and roles, select the
DataStewardfunction.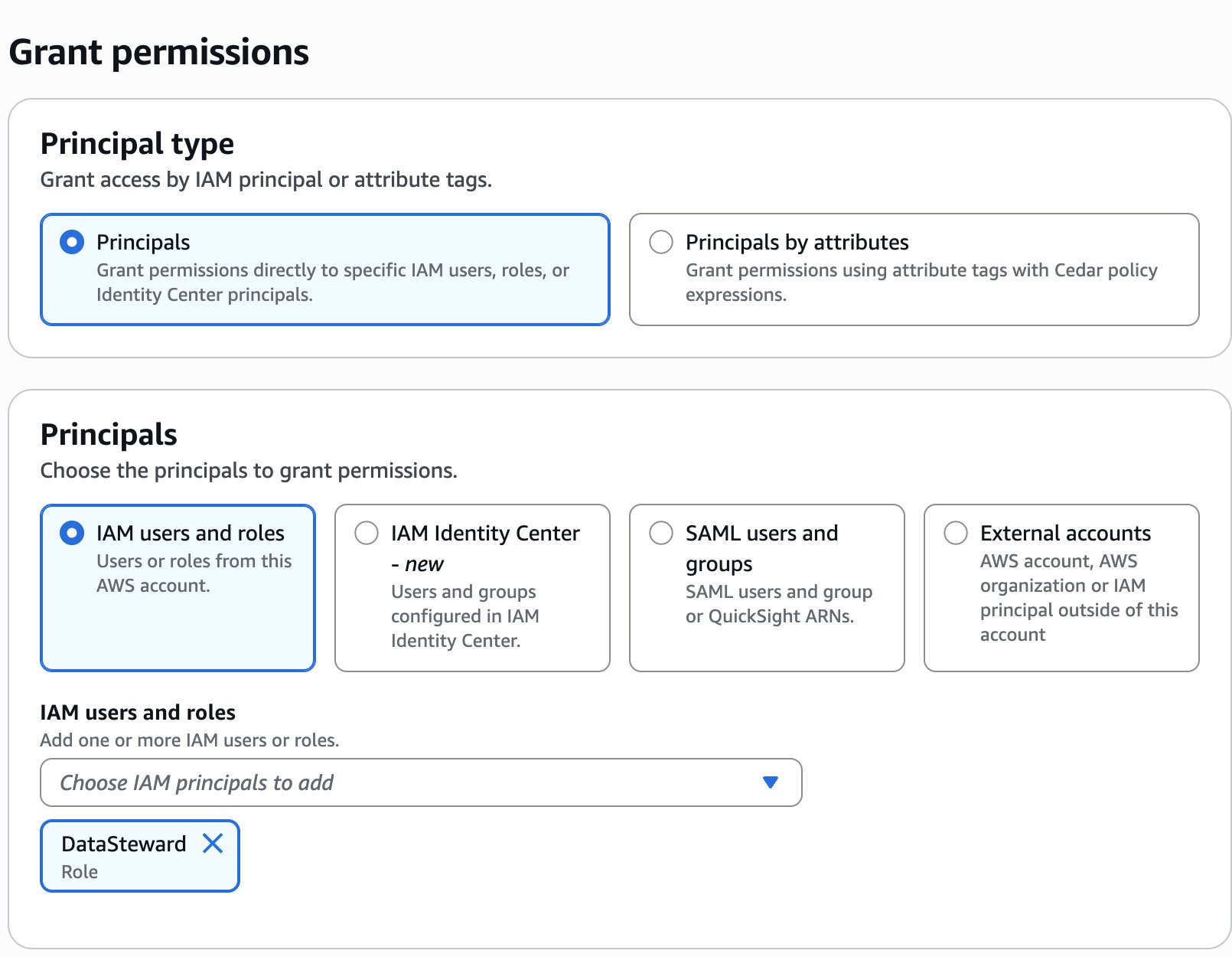
- Within the LF-Tags or catalog sources part, choose Named Information Catalog sources.
- Select
:s3tablescatalog/tbacblog-customer-bucket :redshift_salescatalog/dev 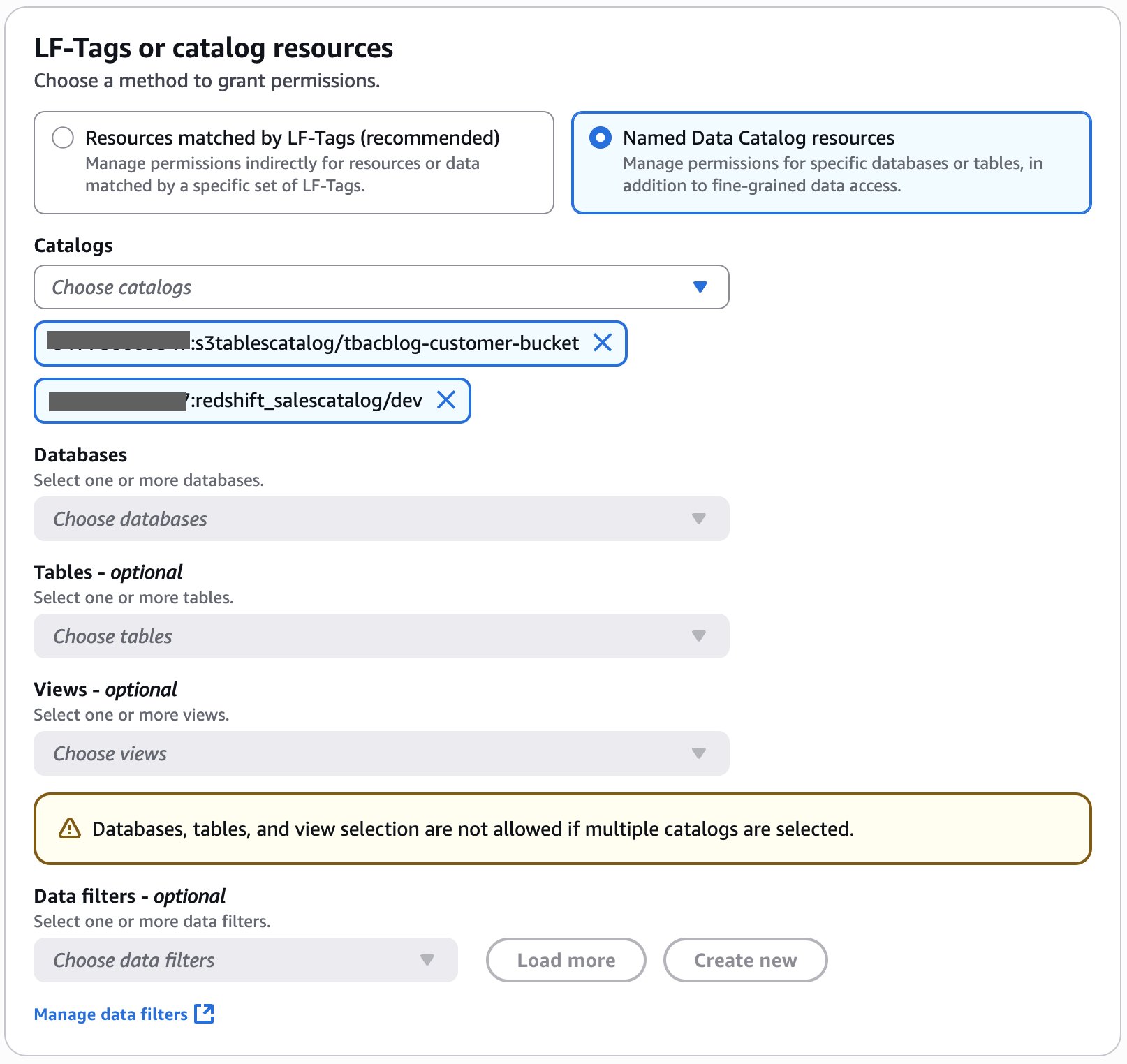
- Within the Catalog permissions part, choose Tremendous consumer for permissions.
- Select Grant.
You may confirm permissions for DataSteward on the Information permissions web page.
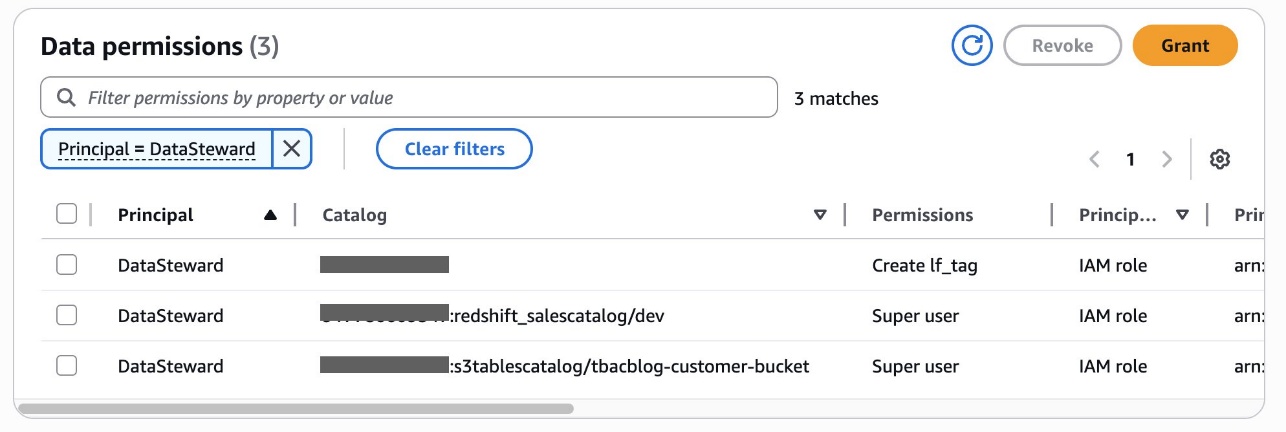
Alice has now accomplished delegating LF-tags creation and project permissions to Bob, the DataSteward. She had additionally granted catalog stage permissions to Bob.
Create LF-Tags
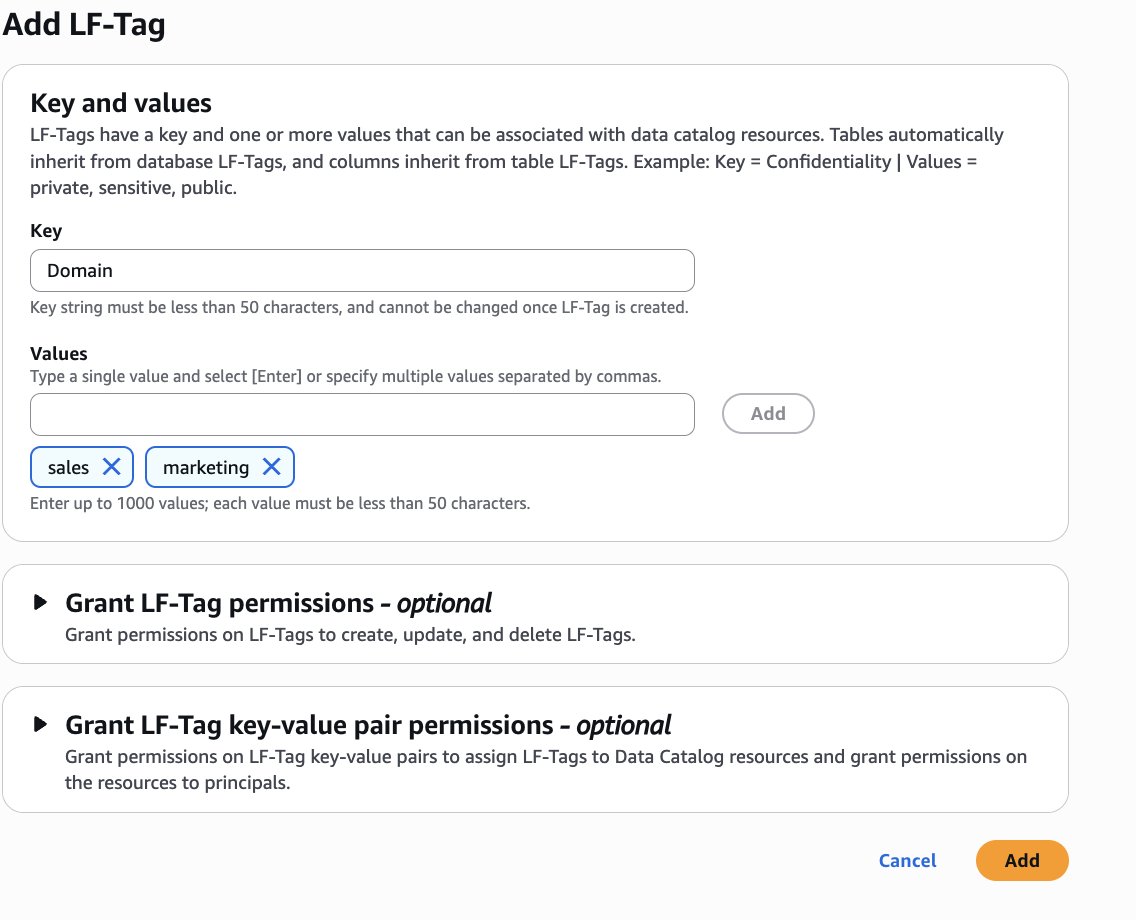
Bob as DataSteward completes the next steps to create LF-Tags:
- Register to the Lake Formation console as
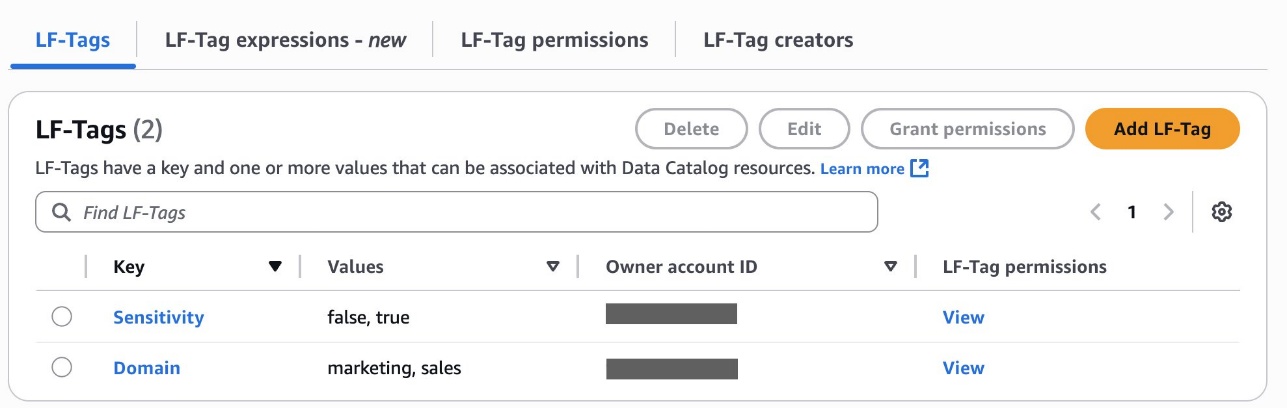
DataSteward. - Within the navigation pane, select LF Tags and permissions, then select the LF-tags tab.
- Select Add-LF-Tag.
- Create LF tags as follows:
- Key:
Areaand Values:gross sales,advertising - Key:
Sensitivityand Values:true,false
- Key:
Assign LF-Tags to the S3 Tables database and desk
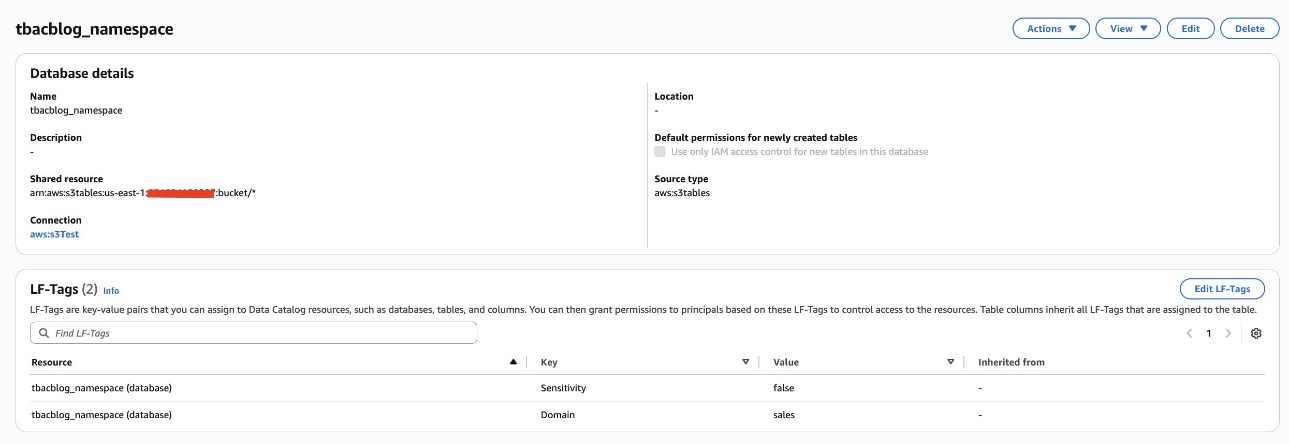
Bob as DataSteward completes the next steps to assign LF-Tags to the S3 Tables database and desk:
- Within the navigation pane, select Catalogs and select
s3tablescatalog. - Select
tbacblog-customer-bucketand selecttbacblog_namespace. - Select Edit LF-Tags.
- Assign the next tags:
- Key: Area and Worth: gross sales
- Key: Sensitivity and Worth: false
- Select Save.
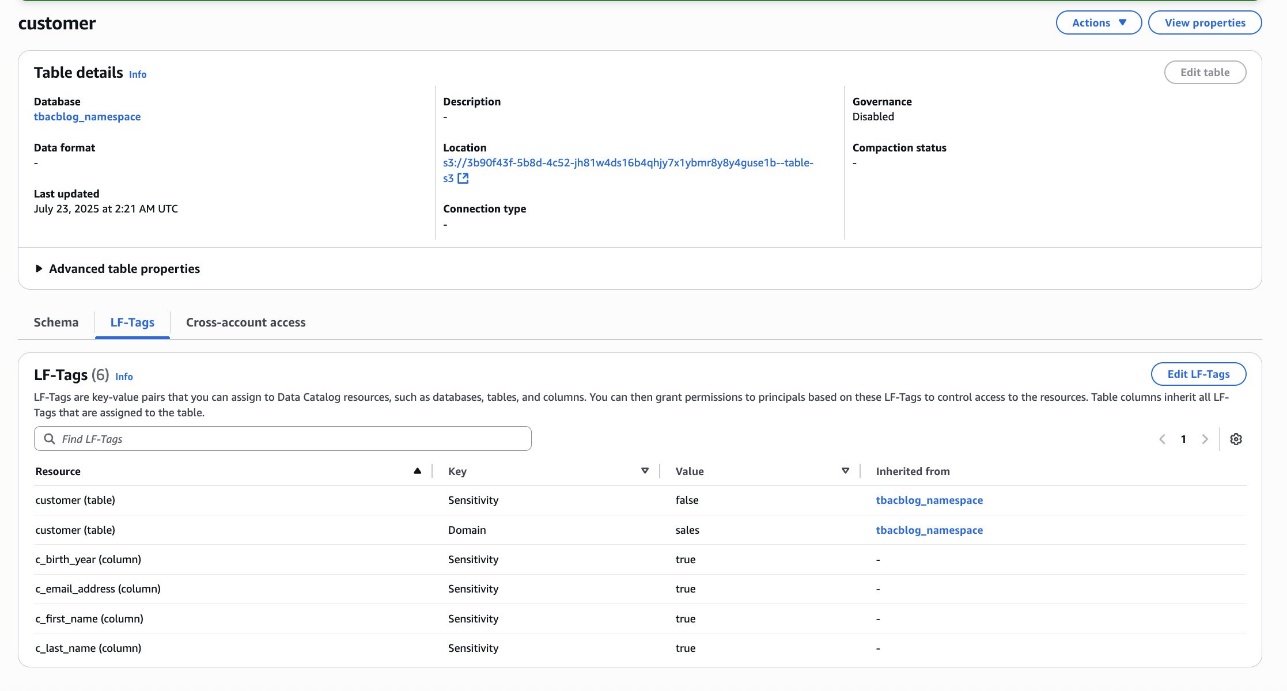
- On the View dropdown menu, select Tables.
- Select the client desk and select the Schema tab.
- Select Edit schema and choose the columns
c_first_name,c_last_name,c_email_address, andc_birth_year. - Select Edit LF-Tags and modify the tag worth:
- Key:
Sensitivityand Worth:true
- Key:
- Select Save.
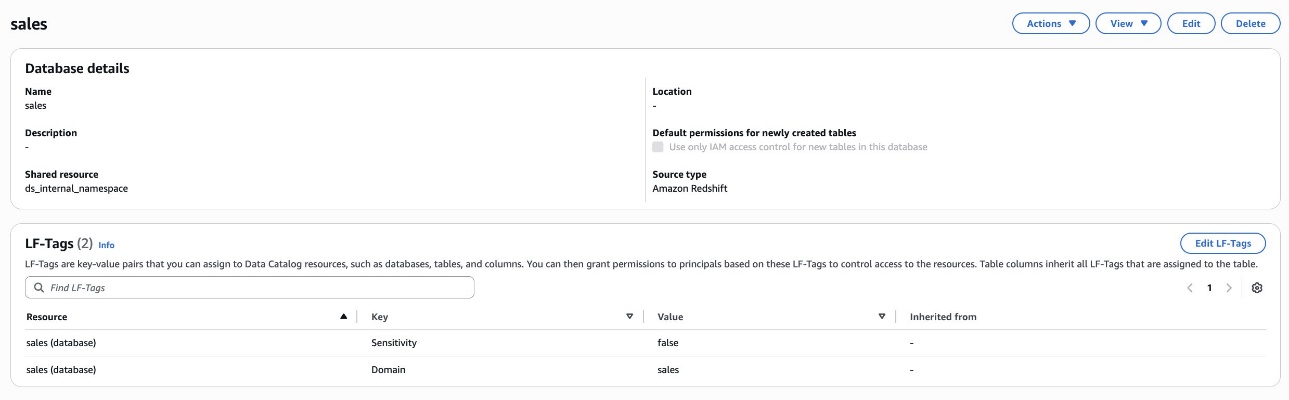
Assign LF-Tags to the Redshift database and desk
Bob as DataSteward completes the next steps to assign LF-Tags to the Redshift database and desk:
- Within the navigation pane, select Catalogs and select
salescatalog. - Select
devand choosegross sales. - Select Edit LF-Tags and assign the next tags:
- Key:
Areaand Worth:gross sales - Key:
Sensitivityand Worth:false
- Key:
- Select Save.
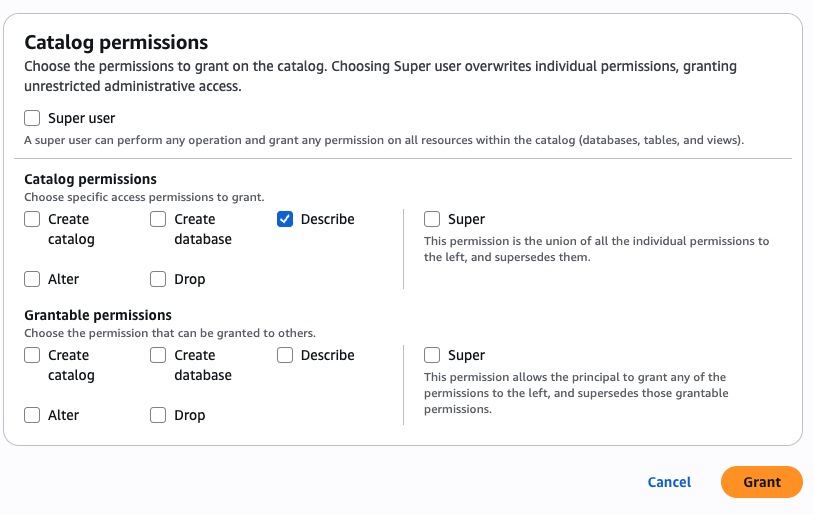
Grant catalog permission to the DataAnalyst and BIEngineer roles
Bob as DataSteward completes the next steps to grant catalog permission to the DataAnalyst and BIEngineer roles (Charlie and Doug, respectively):
- Within the navigation pane, select Datalake permissions, then select Grant.
- Within the Principals part, for IAM customers and roles, select the
DataAnalystandBIEngineerroles. - Within the LF-Tags or catalog sources part, choose Named Information Catalog sources.
- For Catalogs, select
:s3tablescatalog/tbacblog-customer-bucket :salescatalog/dev 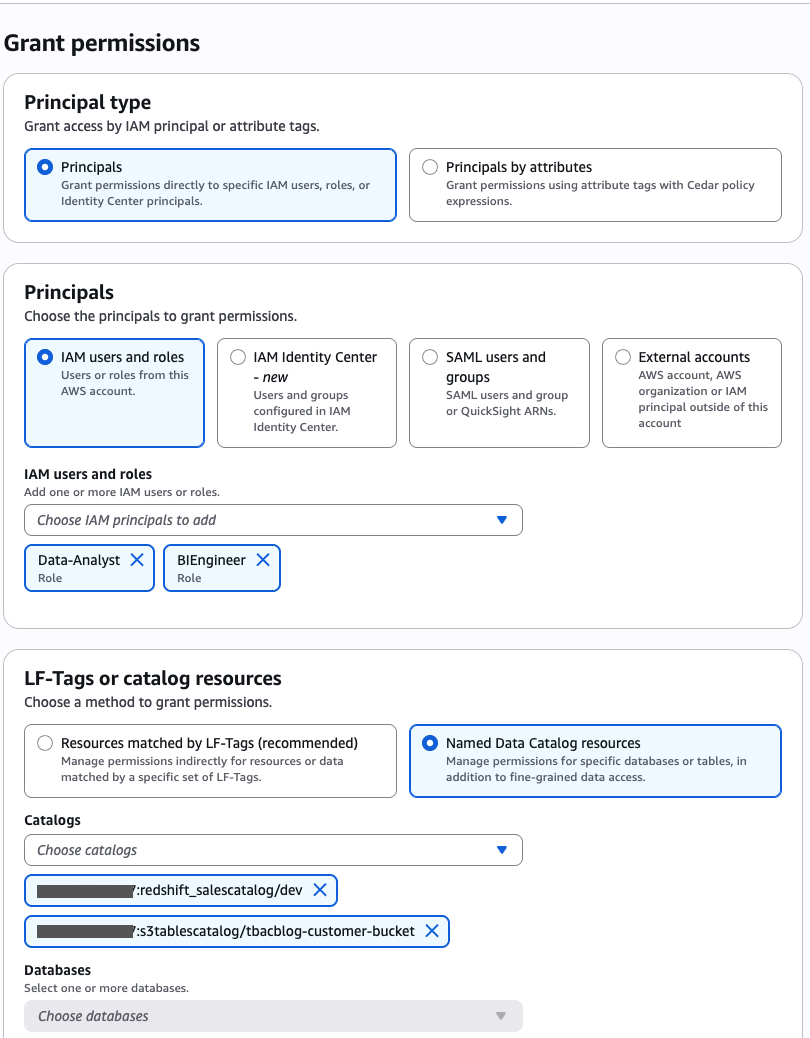
- Within the Catalog permissions part, select Describe for permissions.
- Select Grant.
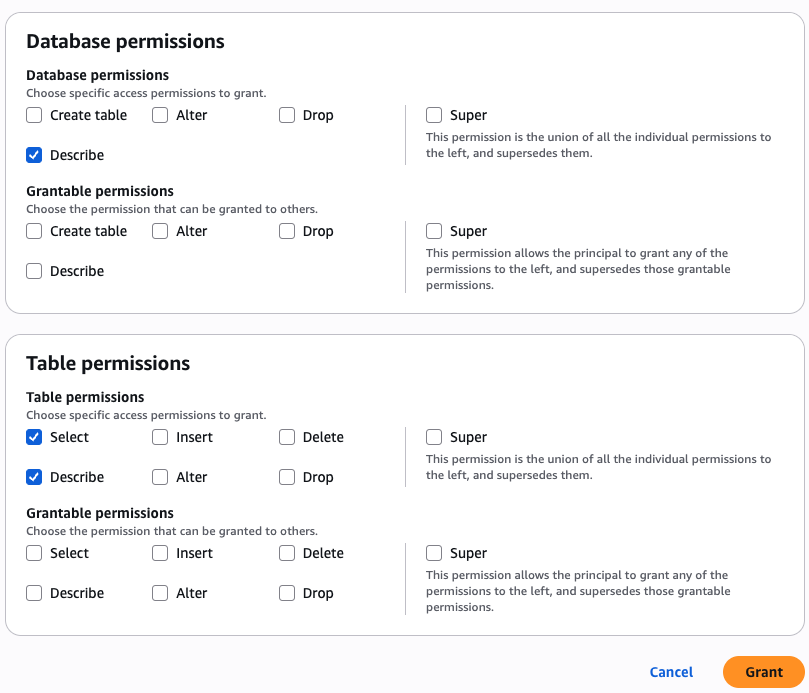
Grant permission to the DataAnalyst function for the gross sales area and non-sensitive information
Bob as DataSteward completes the next steps to grant permission to the DataAnalyst function (Charlie) for the gross sales area for non-sensitive information:
- Within the navigation pane, select Datalake permissions, then select Grant.
- Within the Principals part, for IAM customers and roles, select the
DataAnalystfunction. - Within the LF-Tags or catalog sources part, choose Assets matched by LF-Tags and supply the next values:
- Key:
Areaand Worth:gross sales - Key:
Sensitivityand Worth:false
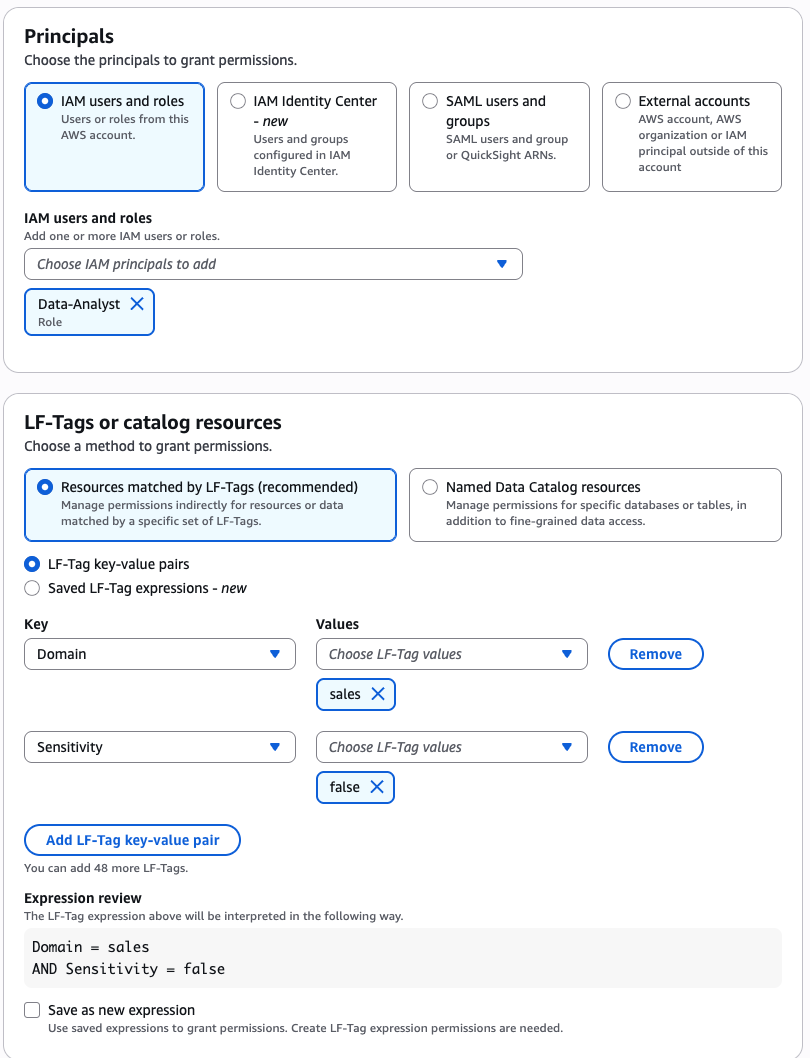
- Key:
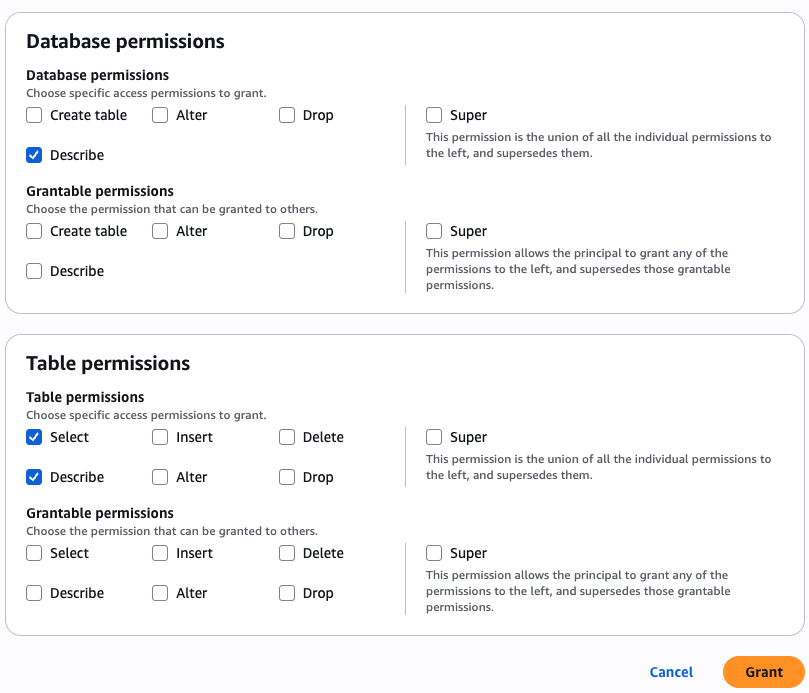
- Within the Database permissions part, select Describe for permissions.
- Within the Desk permissions part, choose Choose and Describe for permissions.
- Select Grant.
Grant permission to the BIEngineer function for gross sales area information
Bob as DataSteward completes the next steps to grant permission to the BIEngineer function (Doug) for all gross sales area information:
- Within the navigation pane, select Datalake permissions, then select Grant.
- Within the Principals part, for IAM customers and roles, select the
BIEngineerfunction. - Within the LF-Tags or catalog sources part, choose Assets matched by LF-Tags and supply the next values:
- Key:
Areaand Worth:gross sales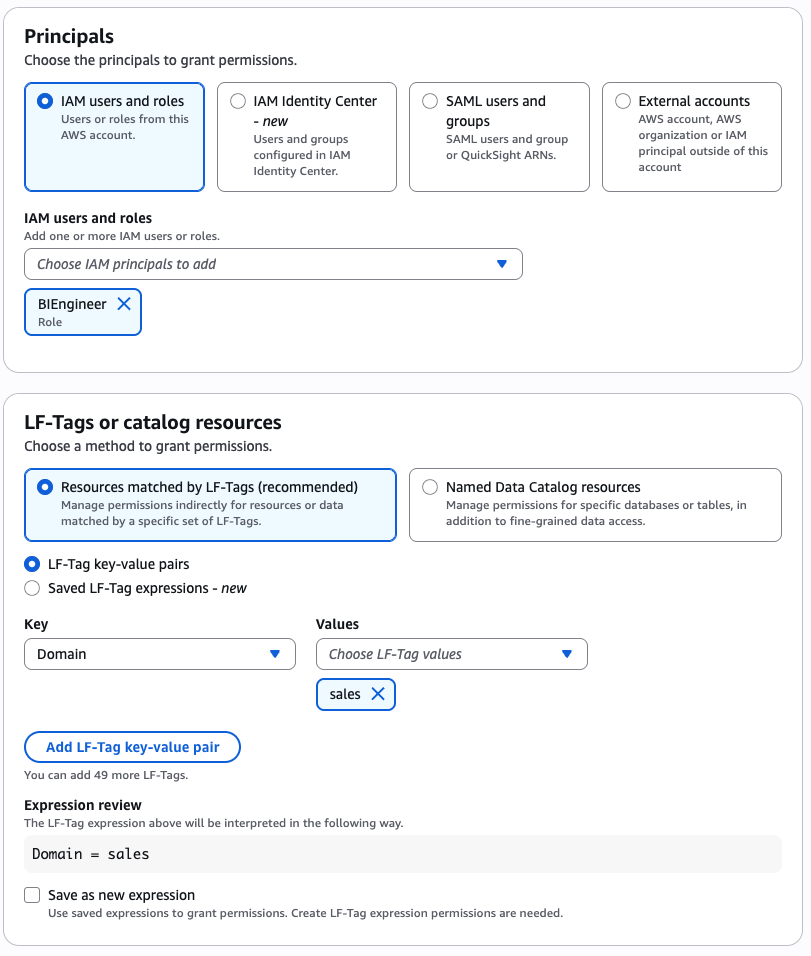
- Key:
- Within the Database permissions part, select Describe for permissions.
- Within the Desk permissions part, choose Choose and Describe for permissions.
- Select Grant.
This completes the steps to grant S3 Tables and Redshift federated tables permissions to varied information personas utilizing LF-TBAC.
Confirm information entry
On this step, we log in as particular person information personas and question the lakehouse tables which can be accessible to every persona.
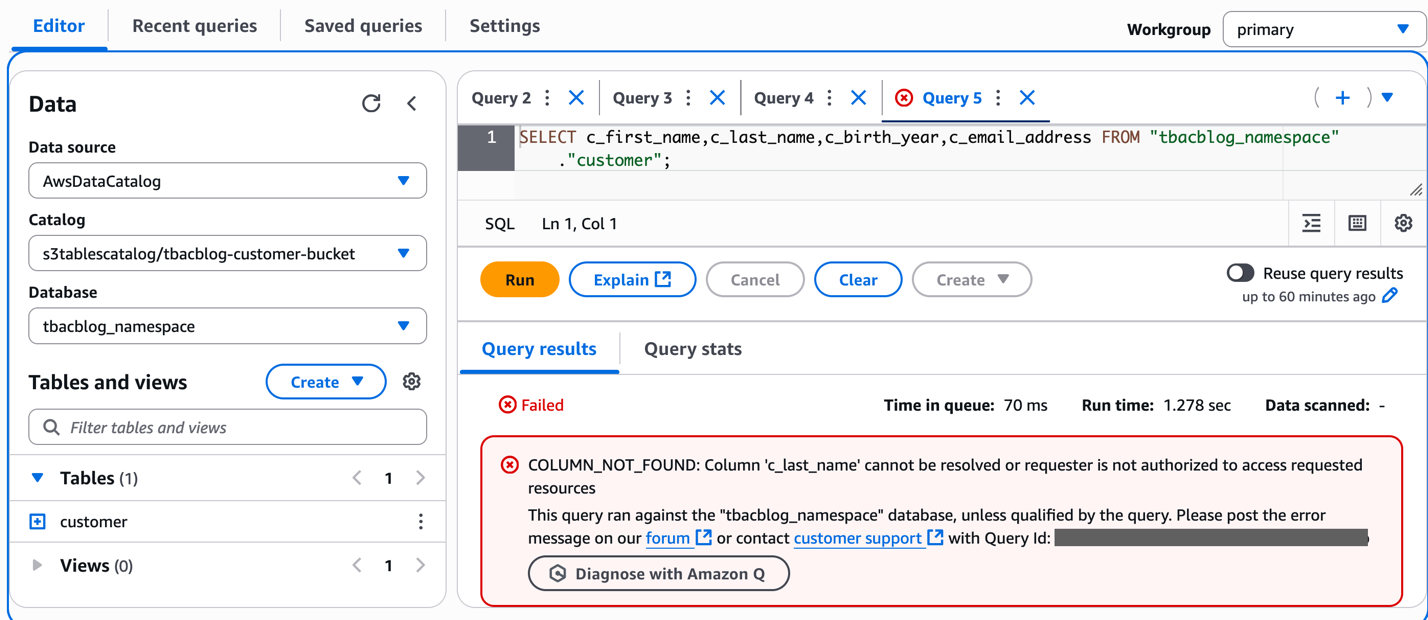
Use Athena to investigate buyer info because the DataAnalyst function
Charlie indicators in to the Athena console because the DataAnalyst function. He runs the next pattern SQL question:
Run a pattern question to entry the 4 columns within the S3table buyer that DataAnalyst doesn’t have entry to. You need to obtain an error as proven within the screenshot. This verifies column stage positive grained entry utilizing LF-tags on the lakehouse tables.
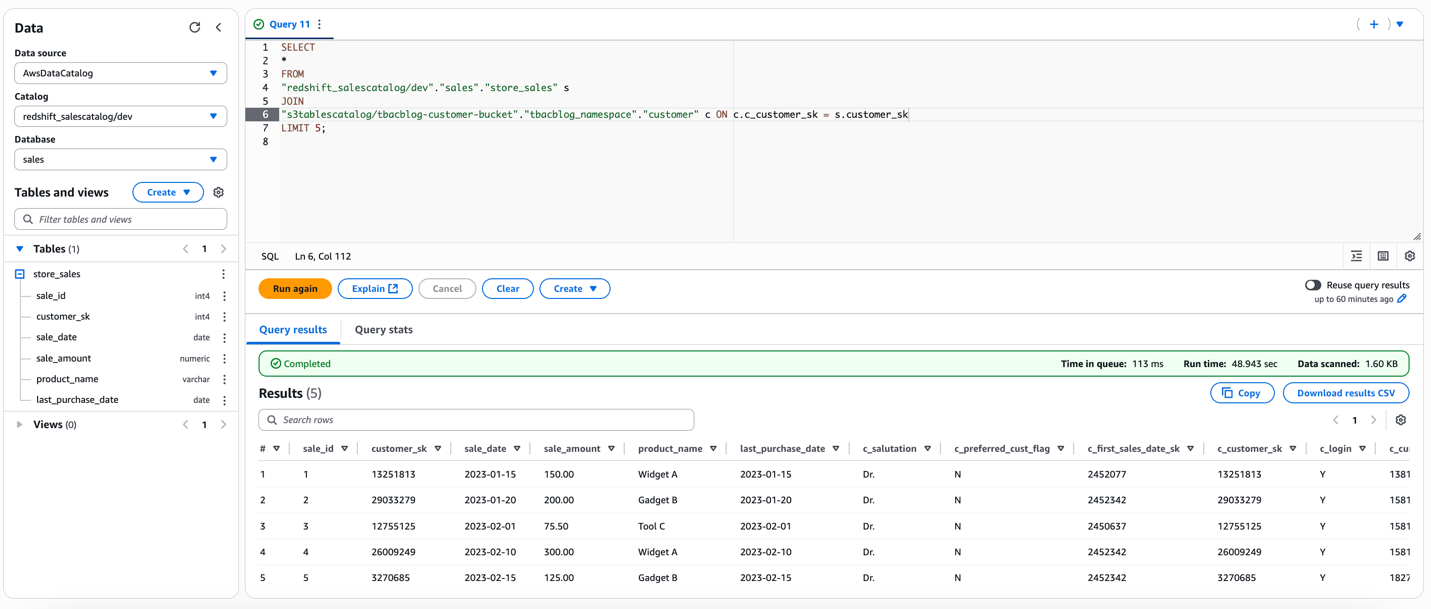
Use the Redshift question editor to investigate buyer information because the DataAnalyst function
Charlie indicators in to the Redshift question editor v2 because the DataAnalyst function and runs the next pattern SQL question:
This verifies the DataAnalyst entry to the lakehouse tables with LF-tags based mostly permissions, utilizing Redshift Spectrum
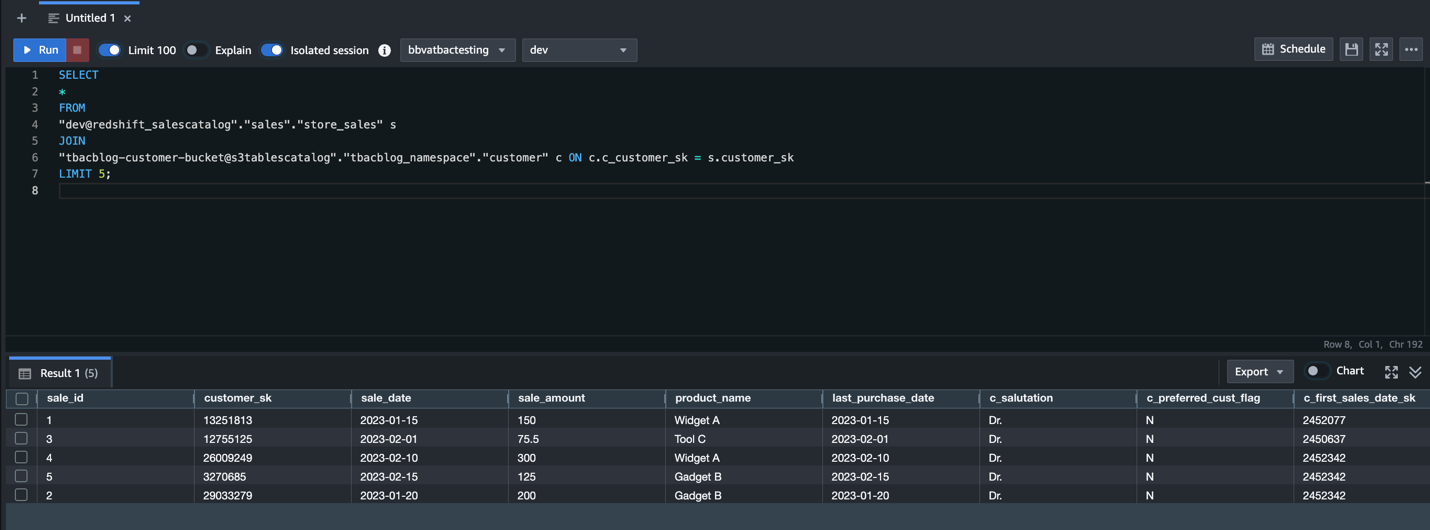
Use Amazon EMR to course of buyer information because the BIEngineer function
Doug makes use of Amazon EMR to course of buyer information with the BIEngineer function:
- Signal-in to the EMR Studio as Doug, with
BIEngineerfunction. Guarantee EMR Serverless utility is hooked up to the workspace withBIEngineerbecause the EMR runtime function.
Obtain the PySpark pocket book tbacblog_emrs.ipynb. Add to your studio atmosphere. - Change the account id, AWS Area and useful resource names as per your setup. Restart kernel and clear output.
- As soon as your pySpark kernel is prepared, run the cells and confirm entry.This verifies entry utilizing LF-tags to the lakehouse tables because the EMR runtime function. For demonstration, we’re additionally offering the pySpark script tbacblog_sparkscript.py that you may run as EMR batch job and Glue 5.0 ETL.
Doug has additionally arrange Amazon SageMaker Unified Studio as lined within the weblog publish Speed up your analytics with Amazon S3 Tables and Amazon SageMaker Lakehouse. Doug logs in to SageMaker Unified Studio and choose beforehand created undertaking to carry out his evaluation. He navigates to the Construct choices and select JupyterLab underneath IDE & Functions. He makes use of the downloaded pyspark pocket book and updates it as per his Spark question necessities. He then runs the cells by choosing compute as undertaking.spark.fineGrained.
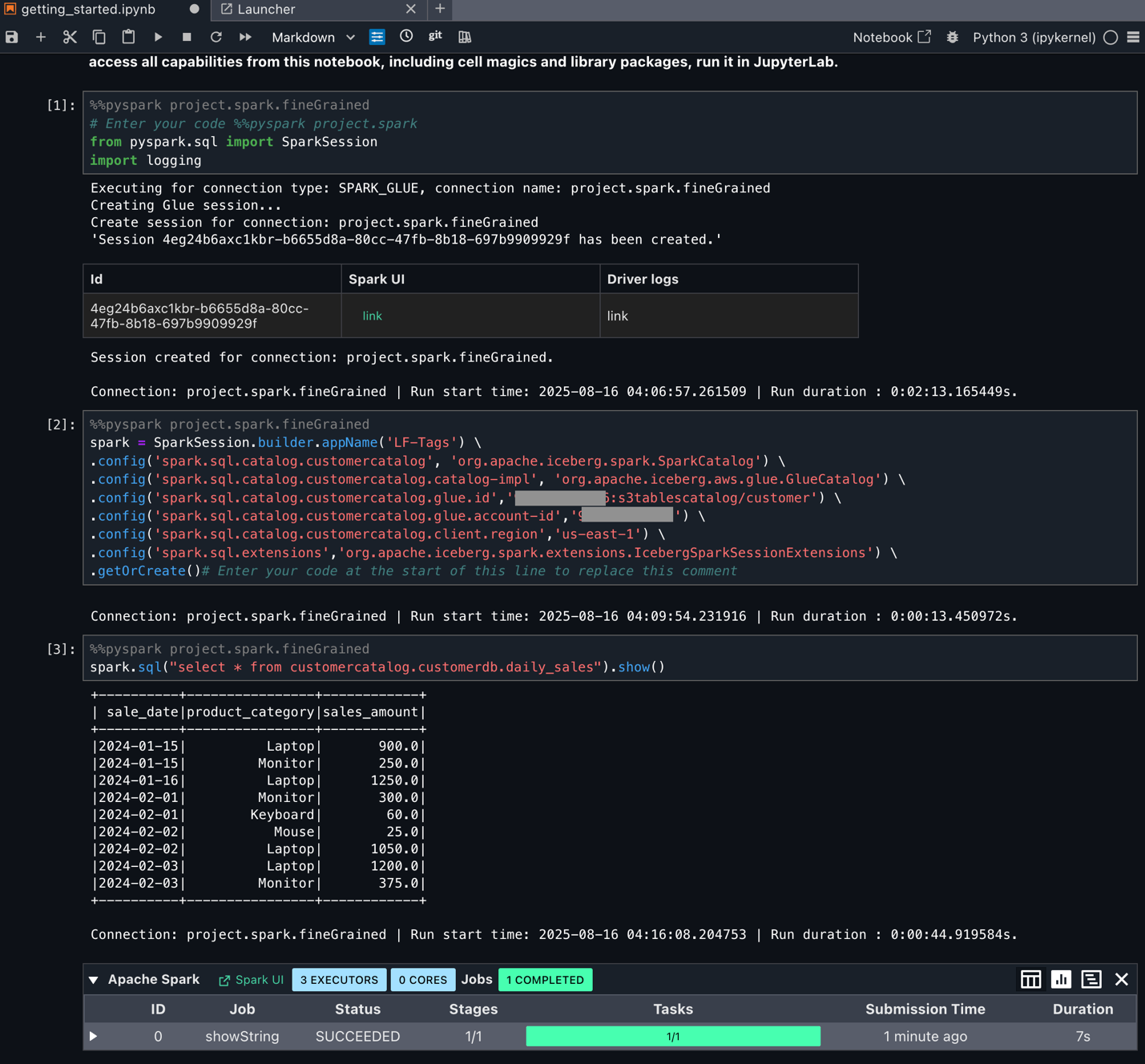
Doug can now begin utilizing Spark SQL and begin processing information as per positive grained entry managed by the Tags.
Clear up
Full the next steps to delete the sources you created to keep away from surprising prices:
- Delete the Redshift Serverless workgroups.
- Delete the Redshift Serverless related namespace.
- Delete the EMR Studio and EMR Serverless occasion.
- Delete the AWS Glue catalogs, databases, and tables and Lake Formation permissions.
- Delete the S3 Tables bucket.
- Empty and delete the S3 bucket.
- Delete the IAM roles created for this publish.
Conclusion
On this publish, we demonstrated how you should utilize Lake Formation tag-based entry management with the SageMaker lakehouse structure to realize unified and scalable permissions to your information warehouse and information lake. Now directors can add entry permissions to federated catalogs utilizing attributes and tags, creating automated coverage enforcement that scales naturally as new property are added to the system. This eliminates the operational overhead of guide coverage updates. You should use this mannequin for sharing sources throughout accounts and Areas to facilitate information sharing inside and throughout enterprises.
We encourage AWS information lake prospects to do this characteristic and share your suggestions within the feedback. To study extra about tag-based entry management, go to the Lake Formation documentation.
Acknowledgment: A particular because of everybody who contributed to the event and launch of TBAC: Joey Ghirardelli, Xinchi Li, Keshav Murthy Ramachandra, Noella Jiang, Purvaja Narayanaswamy, Sandya Krishnanand.
In regards to the Authors
 Sandeep Adwankar is a Senior Product Supervisor with Amazon SageMaker Lakehouse . Primarily based within the California Bay Space, he works with prospects across the globe to translate enterprise and technical necessities into merchandise that assist prospects enhance how they handle, safe, and entry information.
Sandeep Adwankar is a Senior Product Supervisor with Amazon SageMaker Lakehouse . Primarily based within the California Bay Space, he works with prospects across the globe to translate enterprise and technical necessities into merchandise that assist prospects enhance how they handle, safe, and entry information.
 Srividya Parthasarathy is a Senior Huge Information Architect with Amazon SageMaker Lakehouse. She works with the product workforce and prospects to construct strong options and options for his or her analytical information platform. She enjoys constructing information mesh options and sharing them with the neighborhood.
Srividya Parthasarathy is a Senior Huge Information Architect with Amazon SageMaker Lakehouse. She works with the product workforce and prospects to construct strong options and options for his or her analytical information platform. She enjoys constructing information mesh options and sharing them with the neighborhood.
 Aarthi Srinivasan is a Senior Huge Information Architect with Amazon SageMaker Lakehouse. She works with AWS prospects and companions to architect lakehouse options, improve product options, and set up finest practices for information governance.
Aarthi Srinivasan is a Senior Huge Information Architect with Amazon SageMaker Lakehouse. She works with AWS prospects and companions to architect lakehouse options, improve product options, and set up finest practices for information governance.