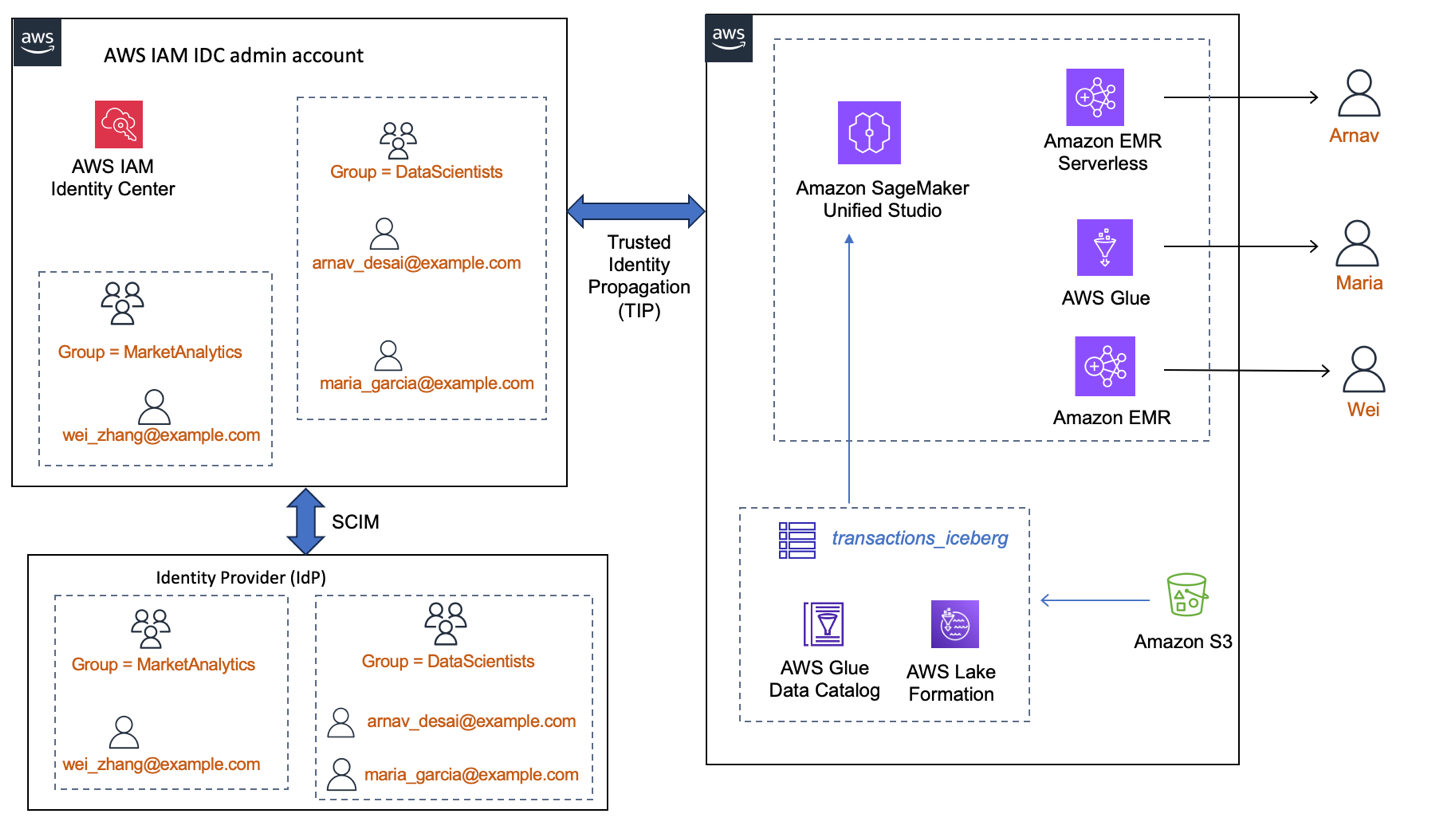
Amazon SageMaker Unified Studio introduces assist for working interactive Apache Spark classes along with your company identities via trusted identification propagation. These Spark interactive classes can be found utilizing Amazon EMR, Amazon EMR Serverless, and AWS Glue. Enterprises with their workforce company identification supplier (IdP) built-in with AWS IAM Id Middle can now use their IAM Id Middle person and group identification seamlessly with SageMaker Unified Studio to entry AWS Glue Knowledge Catalog databases and tables.
Directors of AWS companies can use trusted identification propagation in IAM Id Middle to grant permissions primarily based on person attributes, resembling person ID or group associations. With trusted identification propagation, identification context is added to an IAM function to establish the person requesting entry to AWS sources and is additional propagated to different AWS companies when requests are made. Till now, Spark classes in SageMaker Unified Studio used the undertaking IAM function for managing information entry permissions for all members of the undertaking. This offered fine-grained entry management on the undertaking IAM function degree and never on the person degree. Now, with the trusted identification propagation enabled within the SageMaker Unified Studio area, the info entry could be fine-grained on the person or group degree.
The trusted identification propagation assist for Spark interactive classes makes the SageMaker Unified Studio a holistic providing for enterprise information customers. Enabling trusted identification propagation in SageMaker Unified Studio saves time by avoiding the repeated permission grants to new undertaking IAM roles and enhances safety auditing with the IAM Id Middle person or group ID within the AWS CloudTrail logs.
The next are a few of the use circumstances for trusted identification propagation in Spark classes for SageMaker Unified Studio:
- Single sign-on expertise with AWS analytics – For patrons utilizing enterprise information mesh constructed utilizing AWS Lake Formation, single sign-on expertise with trusted identification propagation is out there for Spark purposes via EMR Studio hooked up with Amazon EMR on EC2 and SQL expertise via Amazon Athena question editor inside EMR Studio. With the addition of EMR Serverless, Amazon EMR on EC2, and AWS Glue for Spark classes with trusted identification propagation enabled in SageMaker Unified Studio, the one sign-on expertise is expanded to offer simpler choices for the info scientists and builders.
- Fantastic-grained entry management primarily based on person identification or group membership– Use a single undertaking throughout the SageMaker Unified Studio area throughout a number of information scientists, with the fine-grained permissions of AWS Lake Formation. When a knowledge scientist accesses the AWS Glue Knowledge Catalog desk, the session is now enabled by their IAM Id Middle person or group permissions. Additional, every can use their most well-liked software, resembling EMR Serverless, AWS Glue, or Amazon EMR on Amazon Elastic Compute Cloud (Amazon EC2), for the Spark classes inside SageMaker Unified Studio.
- Remoted person classes – The Spark interactive classes in SageMaker Unified Studio are securely remoted for every IAM Id Middle person. With safe classes, information groups can focus extra on enterprise information exploration and quicker improvement cycles, somewhat than constructing guardrails.
- Auditing and reporting – Clients in regulated industries want strict compliance reviews displaying fine-grained particulars of their information entry. CloudTrail logs present the
additionalContextdiscipline with the main points of IAM Id Middle person ID or group ID and the analytics engine that accessed the Knowledge Catalog tables from SageMaker Unified Studio. - Develop and scale with unified governance mannequin – Clients who’re already utilizing Amazon Redshift, Amazon QuickSight and AWS Lake Formation permissions built-in with IAM Id Middle can now broaden their ML and information analytics platform to incorporate Spark classes with EMR Serverless and AWS Glue choices in SageMaker Unified Studio. They don’t have to take care of IAM role-based coverage permissions. Trusted identification propagation for Spark classes in SageMaker Unified Studio scales the prevailing permissions mechanism to a wider neighborhood of knowledge scientists and builders.
On this submit, we offer step-by-step directions to arrange Amazon EMR on EC2, EMR Serverless, and AWS Glue inside SageMaker Unified Studio, enabled with trusted identification propagation. We use the setup as an instance how totally different IAM Id Middle customers can run their Spark classes, utilizing every compute setup, throughout the identical undertaking in SageMaker Unified Studio. We present how every person will see solely tables or a part of tables that they’re granted entry to in Lake Formation.
Answer overview
A monetary companies firm processes information from tens of millions of retail banking transactions per day, pooled into their centralized information lake and accessed by conventional company identities. Their machine studying (ML) platform crew wish to allow 1000’s of their information scientists, working throughout totally different groups, with the best dataset and instruments in a safe, scalable and auditable trend. The platform crew chooses to make use of SageMaker Unified Studio, combine their IdP with IAM Id Middle, and handle entry for his or her information scientists on the info lake tables utilizing fine-grained Lake Formation permissions.
In our pattern implementation, we present how you can allow three totally different information scientists—Arnav, Maria, and Wei—belonging to 2 totally different groups, to entry the identical datasets, however with totally different ranges of entry. We use Lake Formation tags to grant column restricted entry and have the three information scientists run their Spark classes throughout the identical SageMaker Unified Studio undertaking. When the person customers register to the SageMaker Unified Studio undertaking, their IDC person or group identification context is added to the SageMaker Unified Studio undertaking execution function, and their fine-grained permissions from Lake Formation on the catalog tables are efficient. We present how their information exploration is remoted and distinctive.
The next diagram reveals an occasion of how an enterprise workforce IdP, built-in with IAM Id Middle, would make the customers and teams accessible to be used by AWS companies. Right here, Lake Formation and SageMaker Unified Studio area are built-in with IAM Id Middle and trusted identification propagation is enabled. On this setup, (a) information permissions are granted to the IDC person or group identities immediately as an alternative of IAM roles (b) the person identification context is out there end-to-end (c) information entry management is centralized in Lake Formation regardless of which analytics service the person makes use of.
Conditions
Working with IAM Id Middle and the AWS companies that combine with IAM Id Middle requires a number of steps. On this submit we use one AWS account with IAM Id Middle enabled and a SageMaker Unified Studio area created. We advocate that you simply use a take a look at account to comply with alongside the weblog.
You want the next stipulations:
Create a undertaking in SageMaker Unified Studio
Now that DataScientists and MarketAnalytics teams are granted entry to the area, IAM Id Middle customers belonging to these two teams can register to the SageMaker Unified Studio portal for the subsequent steps. Observe these steps:
- Sign up to the SageMaker Unified Studio portal as single sign-on person Arnav.
- Create a undertaking
blogproject_tip_enabledbelow the area, as proven within the following screenshot. For particulars, comply with the directions in Create a undertaking. - Choose All capabilities for Mission profile, as proven within the following screenshot. Depart the opposite parameters to default values.
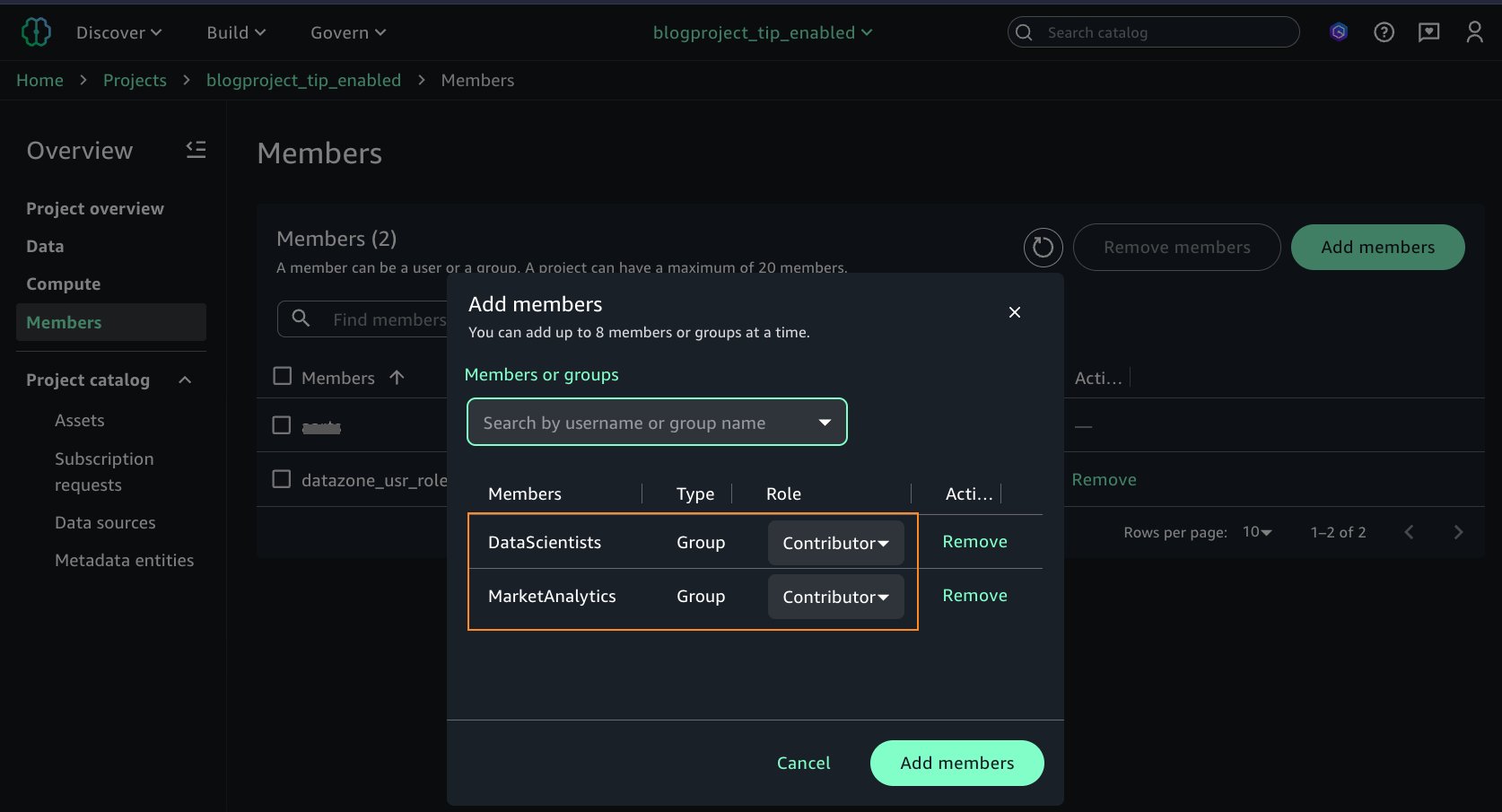
Arnav wish to collaborate with different crew members. After creating the undertaking, he grants entry on the undertaking to extra IAM Id Middle teams. He provides the 2 IAM Id Middle teams, DataScientists and MarketAnalytics, as Members of sort Contributor to the undertaking, as proven within the following screenshot.
To this point, you’ve arrange IAM Id Middle, created customers and teams, created a SageMaker Unified Studio area and undertaking, and added the IAM Id Middle teams as customers to the area and the undertaking. In the remainder of the sections, we arrange the three sorts of computes for Spark interactive session and enter a question on the Lake Formation managed tables as particular person IAM Id Middle customers Arnav, Maria, and Wei.
Arrange EMR Serverless
On this part, we arrange an EMR Serverless compute and run a Spark interactive session as Arnav.
- Sign up to the SageMaker Unified Studio area as the one sign-on person Arnav. Consult with the area’s element web page to get the URL.
- After signing in as Arnav, choose the undertaking
blogproject_tip_enabled. From the left navigation pane, select Compute. On the Knowledge processing tab, select Add compute.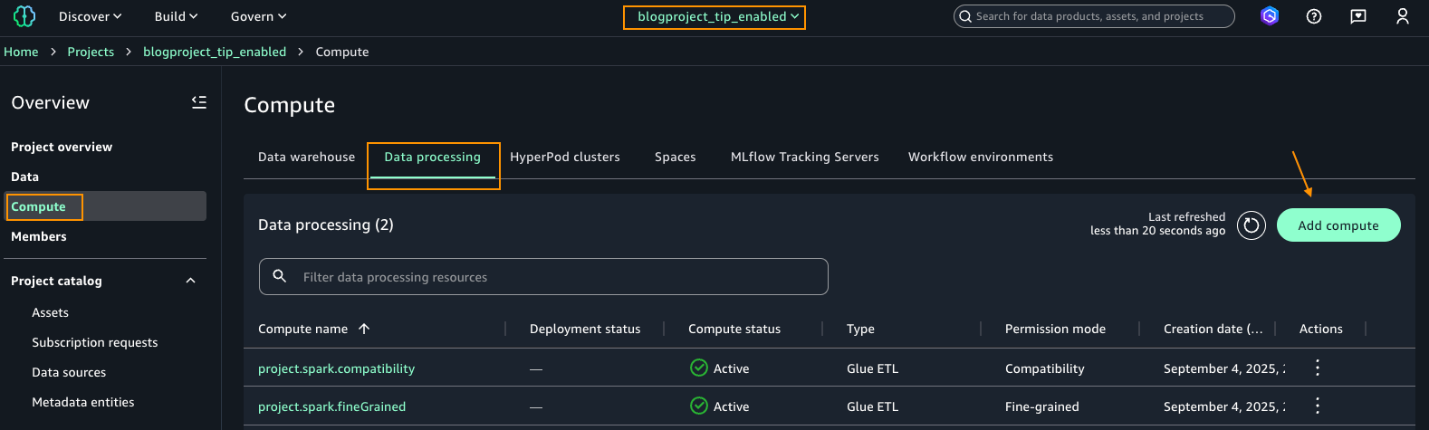
- Beneath Add compute, select Create new compute sources, as proven within the following screenshot.
- Select EMR Serverless.
- Beneath Launch label, select minimal model 7.8.0 and select Fantastic-grained.
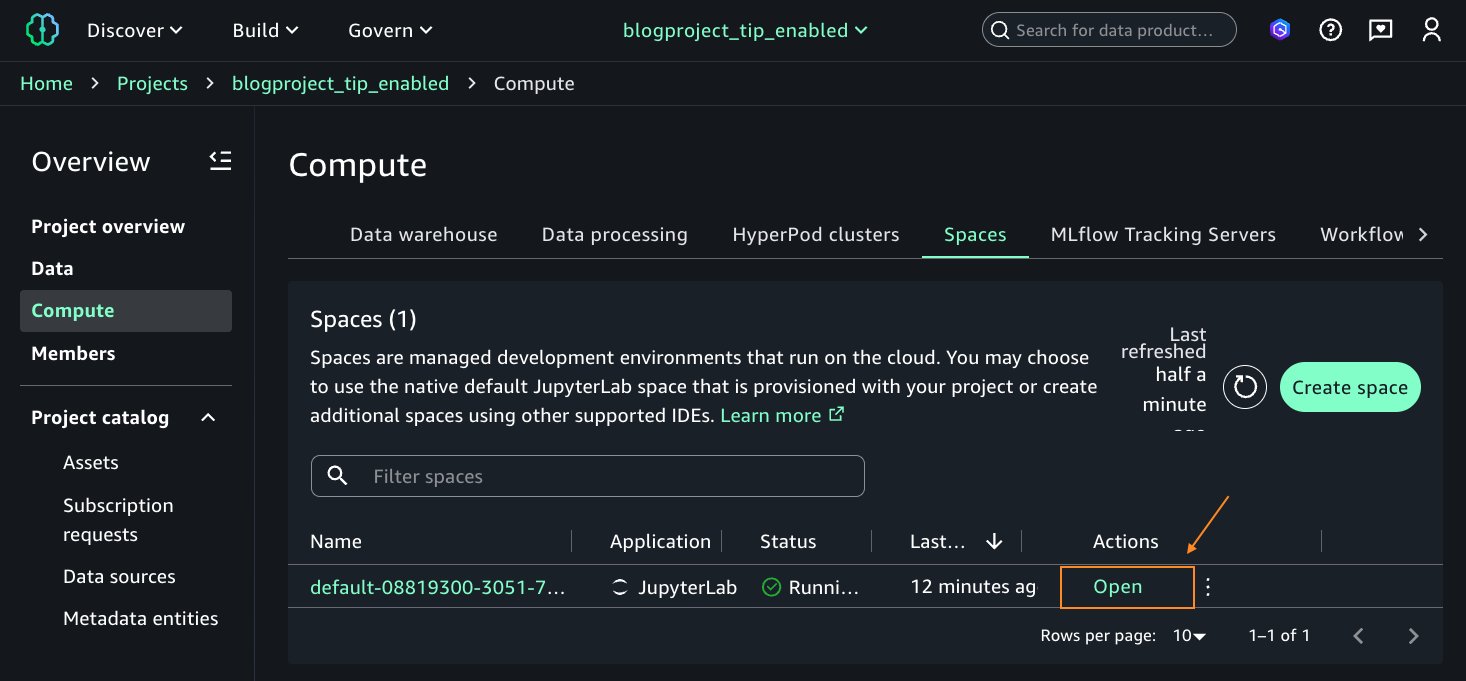
- After the EMR Serverless compute is in Created standing, on the Actions dropdown record, select Open JupyterLab IDE. This can open a Jupyter Pocket book session.
- When the Jupyter pocket book opens, you will note a banner to replace the SageMaker Distribution picture to model 2.9. Observe the directions in Modifying an area and replace the house to make use of model 2.9. Save the house and restart after replace.
- Open the house after it finishes updating. This can open the Jupyter pocket book.
Now, your surroundings is prepared, and you may run Spark queries and take a look at your entry to the deskbankdata_icebergtbl. - On the Launcher window, below Pocket book, select Python 3(ipykernel).
- On the highest a part of the pocket book cell, select PySpark from the kernel dropdown record and emr-s.blog_tipspark_emrserverless from the Compute dropdown record.
- Run the next question:
As a result of Arnav is a part of the DataScientists group, he ought to see all columns of the desk, as proven within the following screenshot.
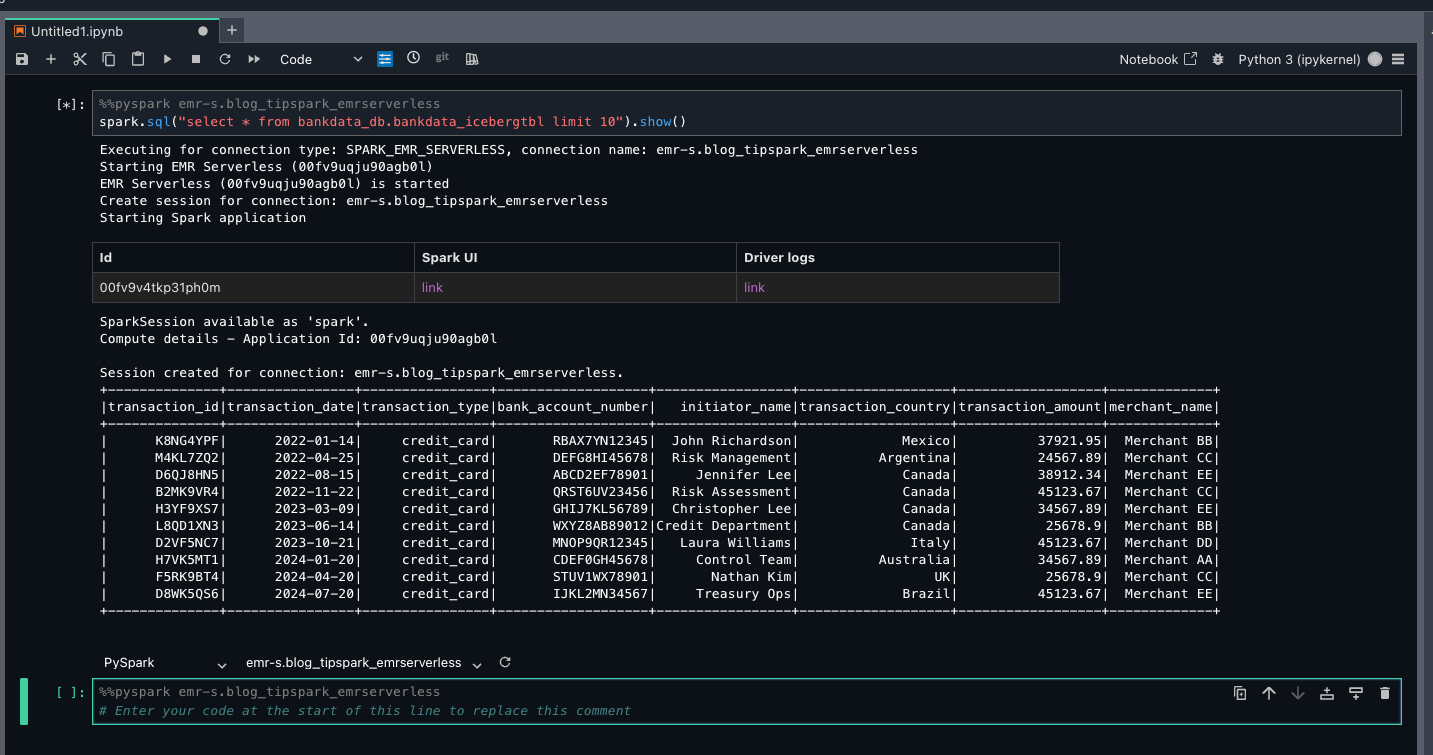
This verifies LF-Tags primarily based entry for Arnav on the bankdata_db.bankdata_icebergtbl utilizing a Spark session in EMR Serverless compute.
Arrange AWS Glue 5.0
On this part, we arrange AWS Glue compute and run a Spark interactive session as Maria.
- Sign up to the SageMaker Unified Studio area as the one sign-on person Maria.
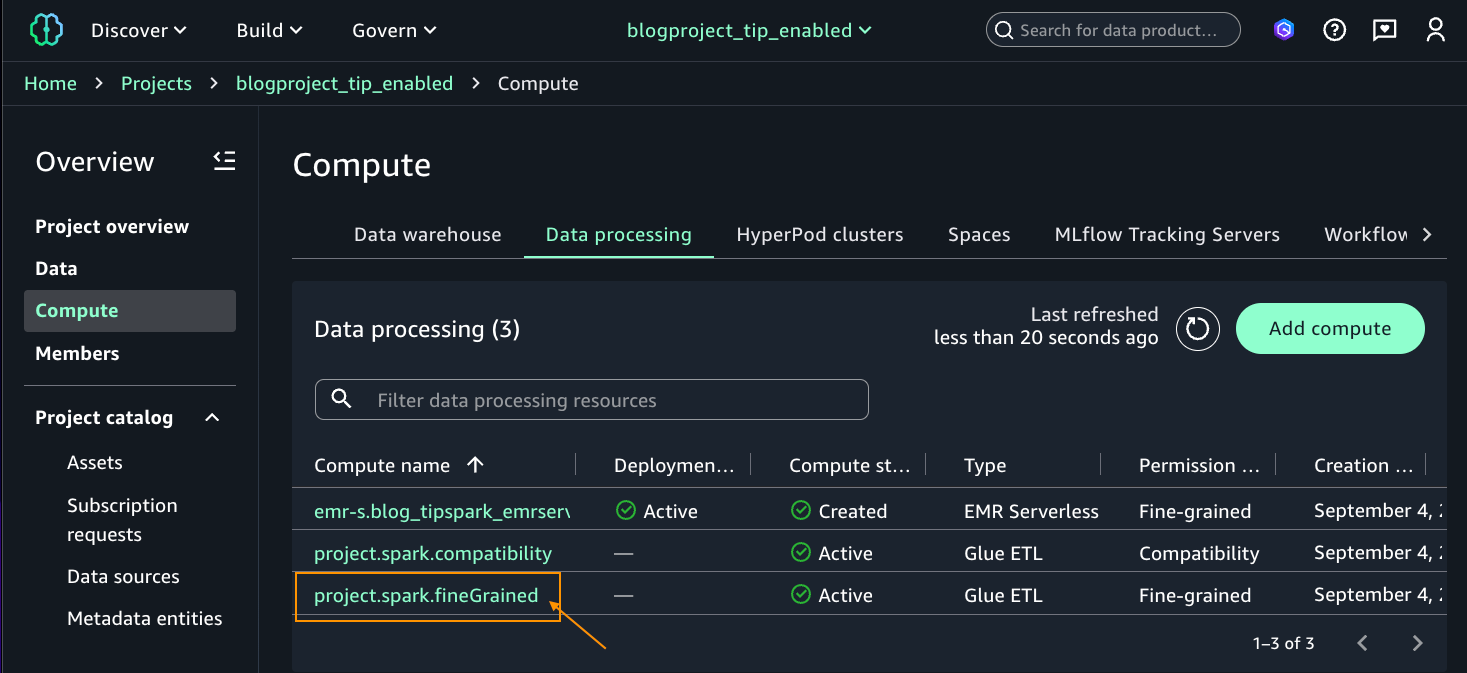
- Select the undertaking
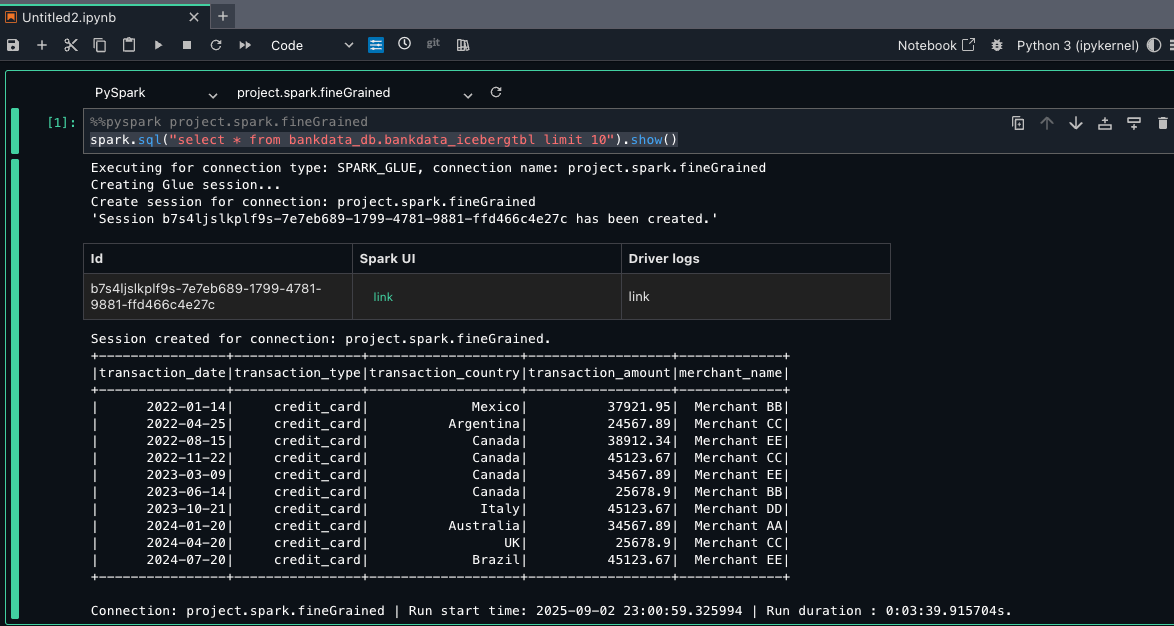
blogproject_tip_enabled. From the left navigation pane, select Compute. On Knowledge processing tab, you must see two computes created by default in Energetic standing (undertaking.spark.compatibility and undertaking.spark.fineGrained) with Sort Glue ETL. For added particulars on these compute varieties, check with AWS Glue ETL in Amazon SageMaker Unified Studio. - Choose the undertaking.spark.fineGrained and launch the Jupyter pocket book with the PySpark kernel.
- For the pocket book cell, select pySpark for kernel and undertaking.spark.fineGrained for compute. Enter the next question:
As a result of Maria is a part of the DataScientists group, she ought to see all columns of the desk, as proven within the following screenshot.
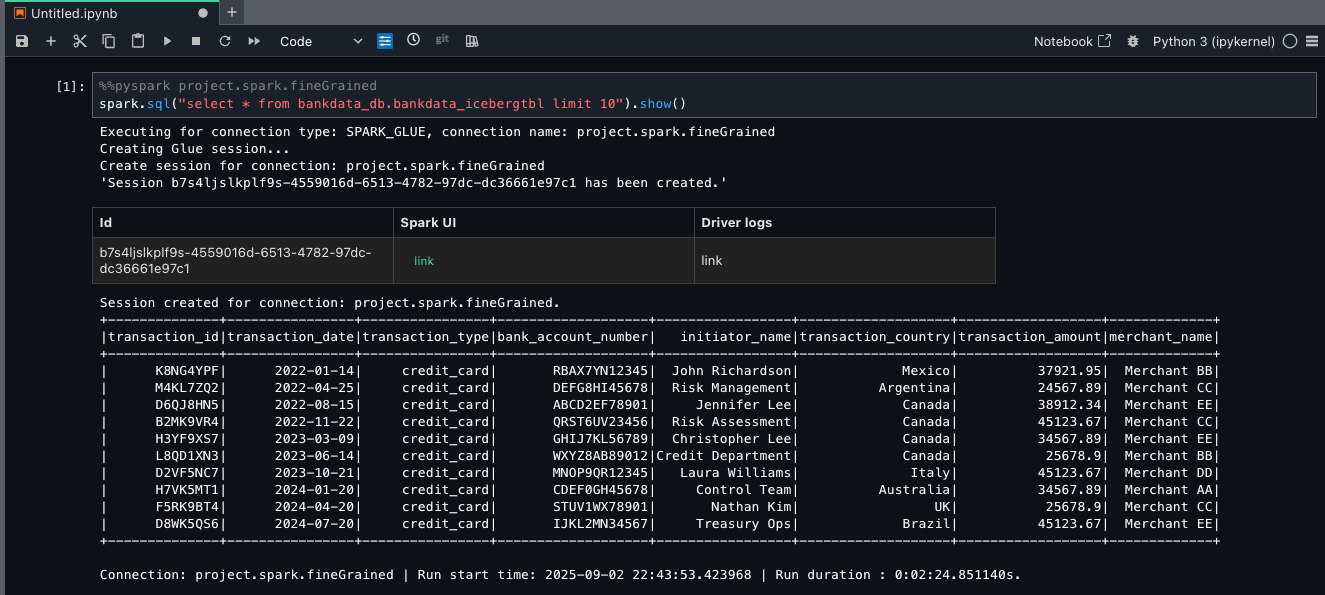
This verifies LF-Tags primarily based entry to Maria on the bankdata_db.bankdata_icebergtbl utilizing Spark session in AWS Glue fine-grained entry management (FGAC) compute.
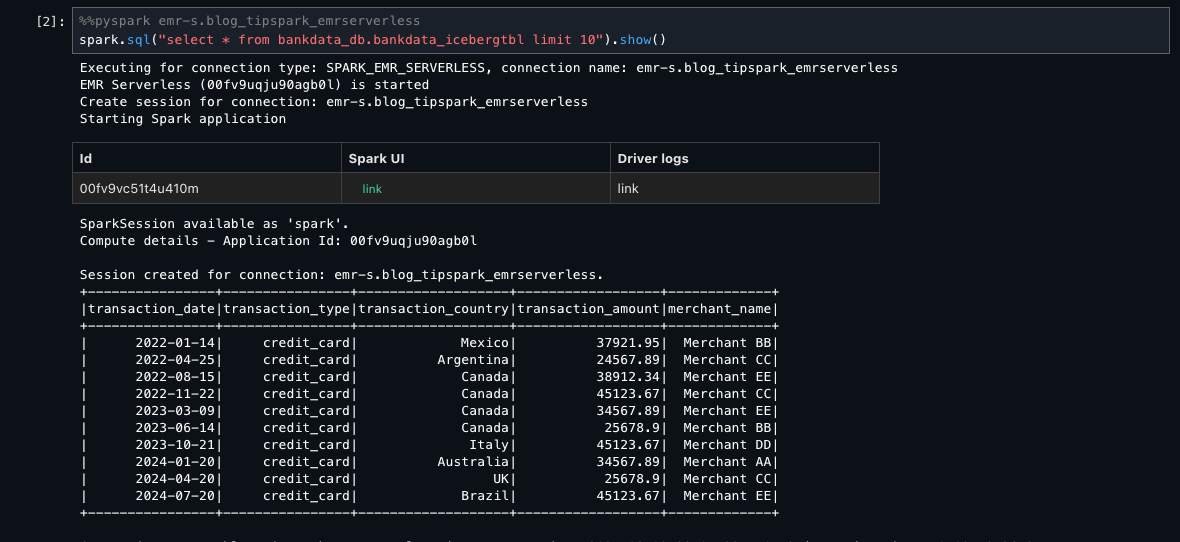
To confirm what entry Wei has utilizing EMR Serverless and AWS Glue, you possibly can signal out and register as person Wei. Enter the Spark SELECT queries on the identical desk. Wei shouldn’t see the three personally identifiable info (PII) columns transaction_id, bank_account_number, and initiator_name, which had been tagged as transactions=secured.
The next screenshot reveals the identical desk for Wei utilizing EMR Serverless.
The next screenshot reveals the identical desk for Wei utilizing AWS Glue FGAC mode.
Arrange Amazon EMR on EC2
On this part, we arrange an Amazon EMR on EC2 compute and run a Spark interactive session as Wei.
- Sign up to the SageMaker Unified Studio area as the one sign-on person Wei.
- Create Amazon EMR on EC2 compute utilizing the steps for EMR Serverless in Setup EMR serverless however select EMR on EC2 cluster as an alternative of EMR Serverless. For the EMR configuration, select the MemoryOptimized or GeneralPurpose configuration, relying on which one you selected to add your PEM certificates to within the undertaking profiles blueprint within the Conditions part. Select an Amazon EMR launch label larger than or equal to 7.8.0.
- After the cluster is provisioned, find the occasion profile function identify within the compute particulars web page, as proven within the following screenshot.
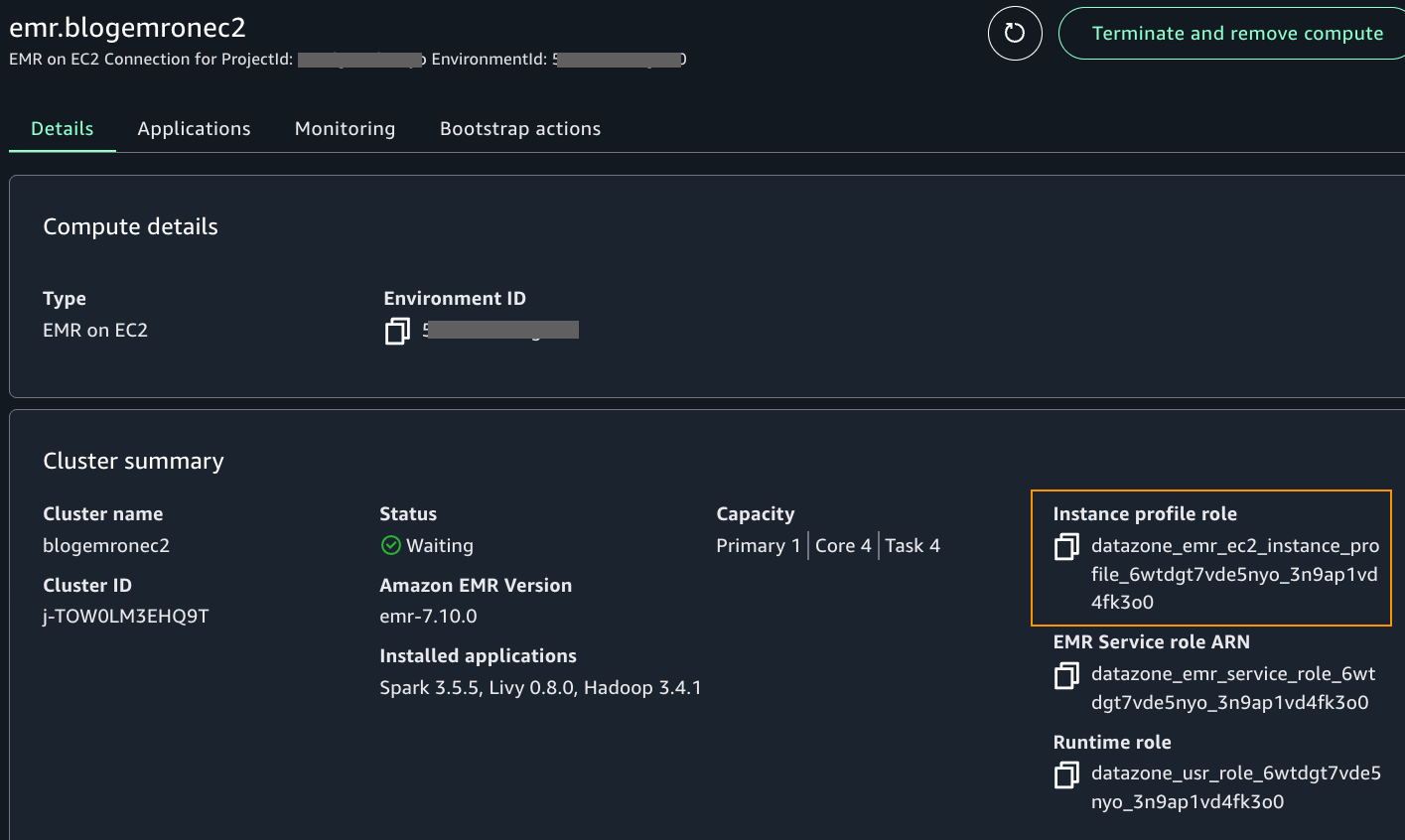
- As an admin person who can edit IAM insurance policies in your account, add the next inline coverage to the occasion profile function. A guide intervention exterior SageMaker Unified Studio is required at present to carry out this step. This might be addressed sooner or later.
- After updating the function’s coverage, you need to use the Amazon EMR on EC2 connection to provoke an interactive Spark session. Just like the way you launched a pocket book as Arnav and Maria, do the identical steps to launch the pocket book as person Wei.
- On the Construct tab, select JupyterNotebook from the undertaking house web page. Select Python3(ipykernel) to launch the pocket book. Select Configure house to replace to model 2.9. Refresh the pocket book browser.
- Contained in the pocket book, on high of the cell, select PySpark for kernel and emr.blog_tip_emronec2 that you simply launched for the compute.
- Enter a choose question on the desk as follows:
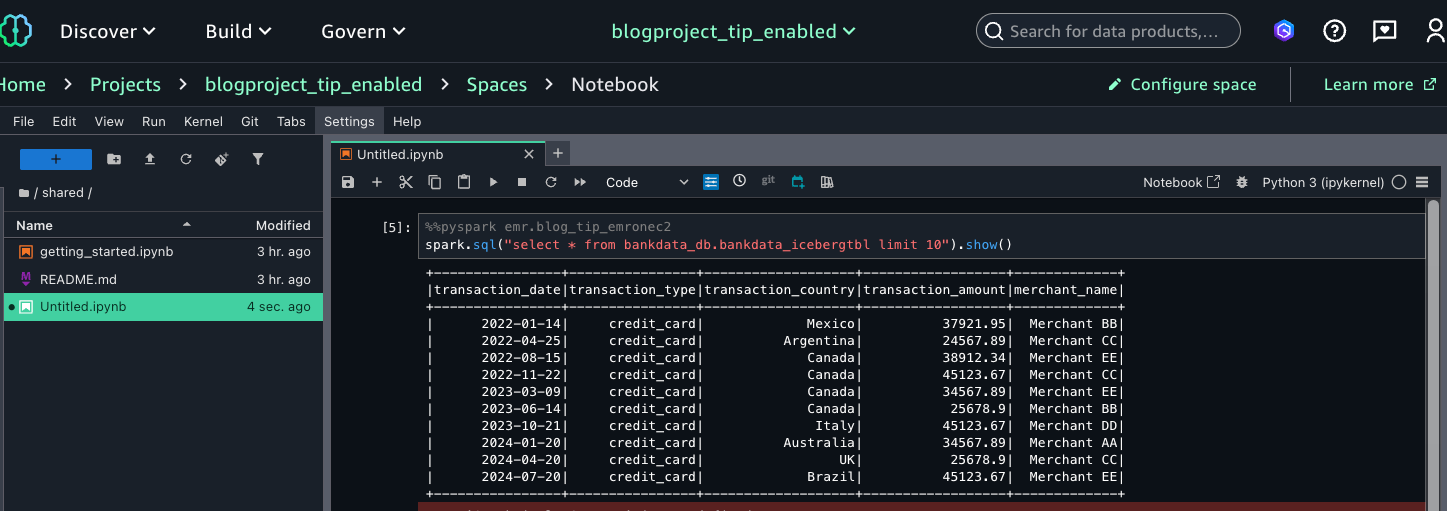
This verifies that Wei, as a part of the MarketAnalytics group, sees all columns of the desk with LF-Tags transactions=accessible however doesn’t have entry to the three columns that had been overwritten with LF-Tags transactions=secured (transaction_id, bank_account_number, and initiator_name).
You’ll be able to hint the person entry of the desk within the CloudTrail logs for EventName=GetDataAccess. Within the related CloudTrail log proven under, we discover that the UserID for Wei is offered below additionalEventData discipline, whereas requestParameters has the tableARN.
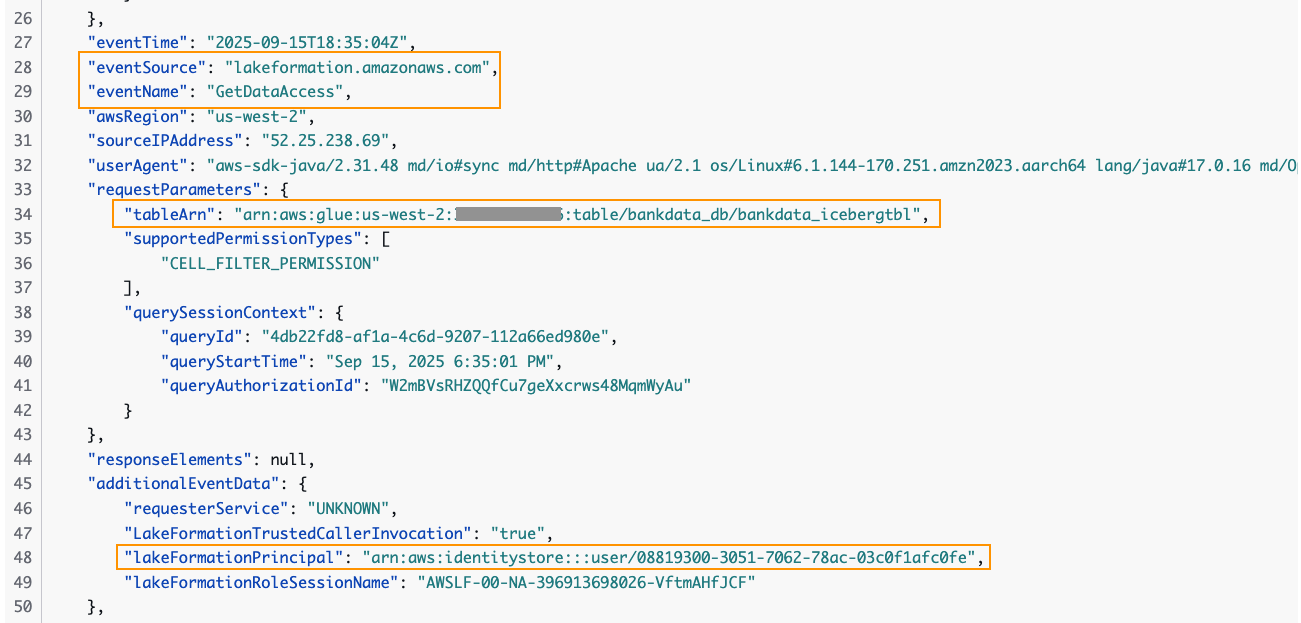
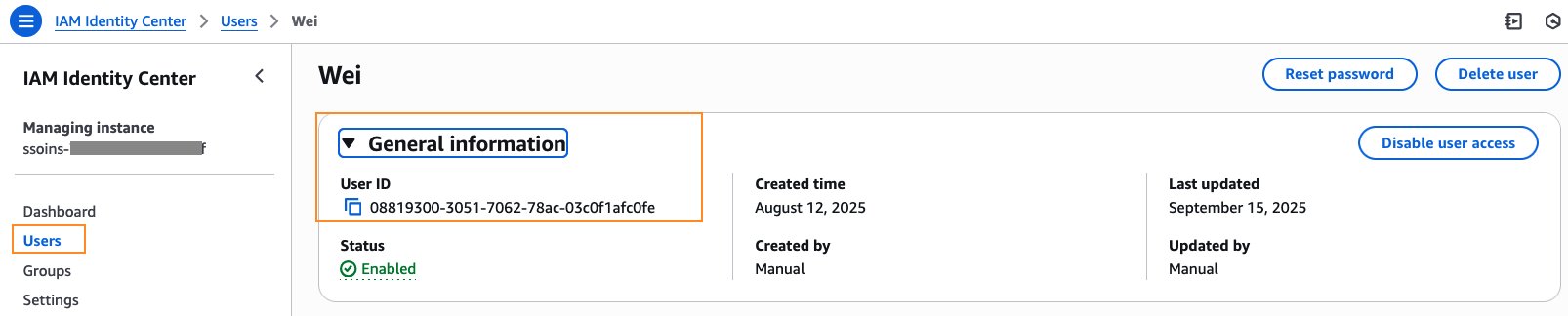
The person ID for Wei is out there within the IAM Id Middle console below Normal info.
Thus, we had been capable of register as a person IAM Id Middle person to the SageMaker Unified Studio area and question the Knowledge Catalog tables utilizing Amazon EMR and AWS Glue compute. These IAM Id Middle customers had been capable of question the tables that they had been granted entry to, as an alternative of the SageMaker Unified Studio undertaking’s IAM function.
Cleanup
To keep away from incurring prices, it’s necessary to delete the sources launched for this walkthrough. Clear up the sources as follows:
- SageMaker Unified Studio by default shuts down idle sources resembling JupyterLab after 1 hour. Should you’ve created a SageMaker Unified Studio area for this submit, bear in mind to delete the area.
- Should you’ve created IAM Id Middle customers and teams, delete the customers and delete the teams. Additional, if you happen to’ve created an IAM Id Middle occasion just for this submit, delete your IAM Id Middle occasion.
- Delete the database
bankdata_dbfrom Lake Formation. This will even delete the tables and all related permissions. Delete the LF-Tagtransactionsand its values. - Delete the desk’s corresponding information out of your S3 bucket two subfolders
bankdata-csvandbankdata-iceberg.
Conclusion
On this submit, we walked via how you can allow a SageMaker Unified Studio area with IAM Id Middle trusted identification propagation and question Lake Formation managed tables in Knowledge Catalog utilizing Apache Spark interactive classes with EMR Serverless, AWS Glue, and Amazon EMR on EC2. We additionally verified in CloudTrail logs the IAM Id Middle person ID accessing the desk.
Amazon SageMaker Unified Studio with trusted identification propagation supplies the next advantages.
Enterprise advantages
- Enhanced information safety
- Improved workforce information entry and insights
Technical capabilities
- Permits information entry primarily based on workforce identification
- Offers unified governance via Lake Formation for Knowledge Catalog tables when accessed via SMUS
- Ensures remoted and safe classes for every IAM Id Middle person
- Helps a number of analytics choices:
- Spark classes by way of EMR Serverless, EMR on EC2, and AWS Glue
- SQL analytics via Athena and Redshift Spectrum
Organizational benefits
- Direct use of company identities for enterprise information entry
- Simplified entry to information platforms and meshes constructed on Knowledge Catalog and Lake Formation
- Permits varied person roles to work with their most well-liked AWS analytics companies
- Reduces information exploration time for Spark-familiar information scientists
To be taught extra, check with the next sources:
We encourage you to take a look at the brand new trusted identification propagation enabled SageMaker Unified Studio for Spark classes. Attain out to us via your AWS account groups or utilizing the feedback part.
Acknowledgment: A particular due to everybody who contributed to the event and launch of this characteristic: Palani Nagarajan, Karthik Seshadri, Vikrant Kumar, Yijie Yan, Radhika Ravirala and Jerica Nicholls.
APPENDIX A – Desk creation in Knowledge Catalog
- We’ve created an artificial financial institution transactions dataset with 100 rows in CSV format. Obtain the dataset dummy_bank_transaction_data.csv
- In your S3 bucket, create two subfolders:
bankdata-csvandbankdata-icebergand add the dataset tobankdata-csv. - Open the Athena console, navigate to question editor, and enter the next statements in sequence:
- Enter a preview and confirm the desk information:
APPENDIX B – Creating LF-Tags, attaching tags to the desk from Appendix A, and granting permissions to IAM Id Middle customers.
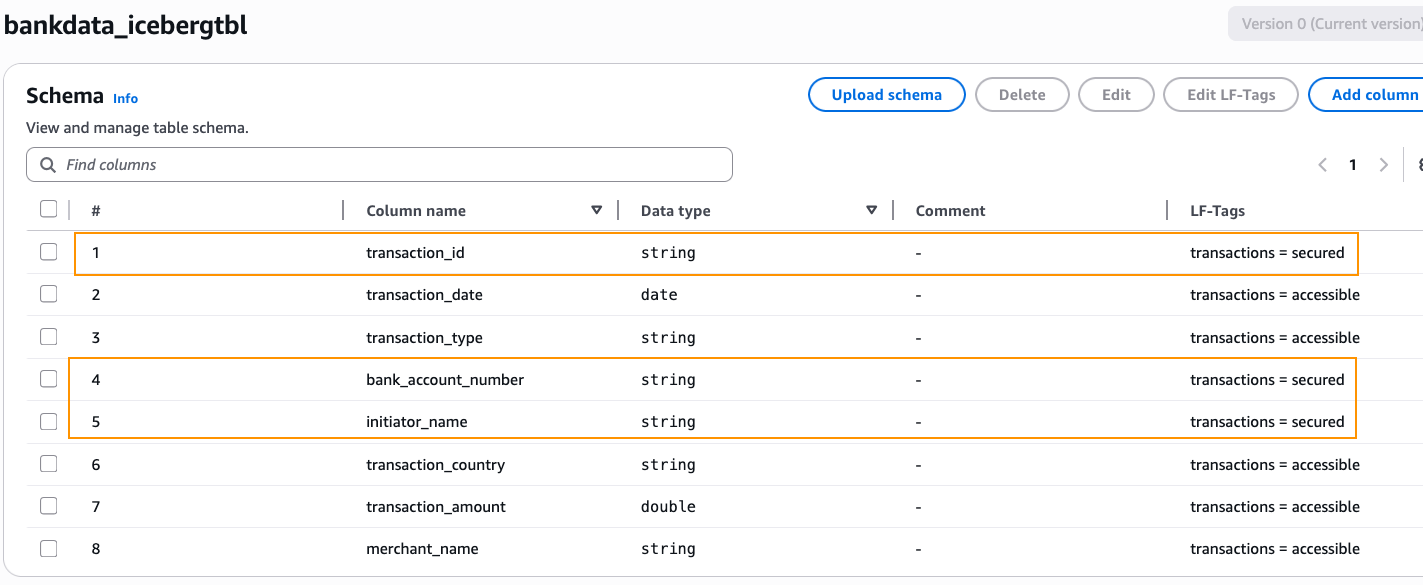
We create a Lake Formation tag with Keyname = transactions and Values = secured, accessible. We affiliate the tag to the desk and overwrite a couple of columns as summarized within the desk.
|
Useful resource |
LF-Tag affiliation |
|
|
Database |
bankdata_db |
transactions = accessible |
|
Desk |
bankdata_icebergtbl |
transactions = accessible |
| Columns | transaction_id | transactions = secured |
| bank_account_number | transactions = secured | |
| initiator_name | transactions = secured |
We then grant Lake Formation permissions to the 2 IAM Id Middle teams utilizing these LF-Tags as follows:
|
IAM Id Middle group |
LF-Tags |
Permission |
|
DataScientists |
transactions = accessible AND transactions = secured |
Database DESCRIBE, Desk SELECT |
|
MarketAnalytics |
transactions = accessible |
Database DESCRIBE, Desk SELECT |
- Sign up to the Lake Formation console and navigate to LF-Tags and permissions. Create an LF-Tag with Keyname =
transactionsand Values =secured,accessible. - Choose the database
bankdata_dband affiliate the LF-Tagtransactions=accessible. - Choose
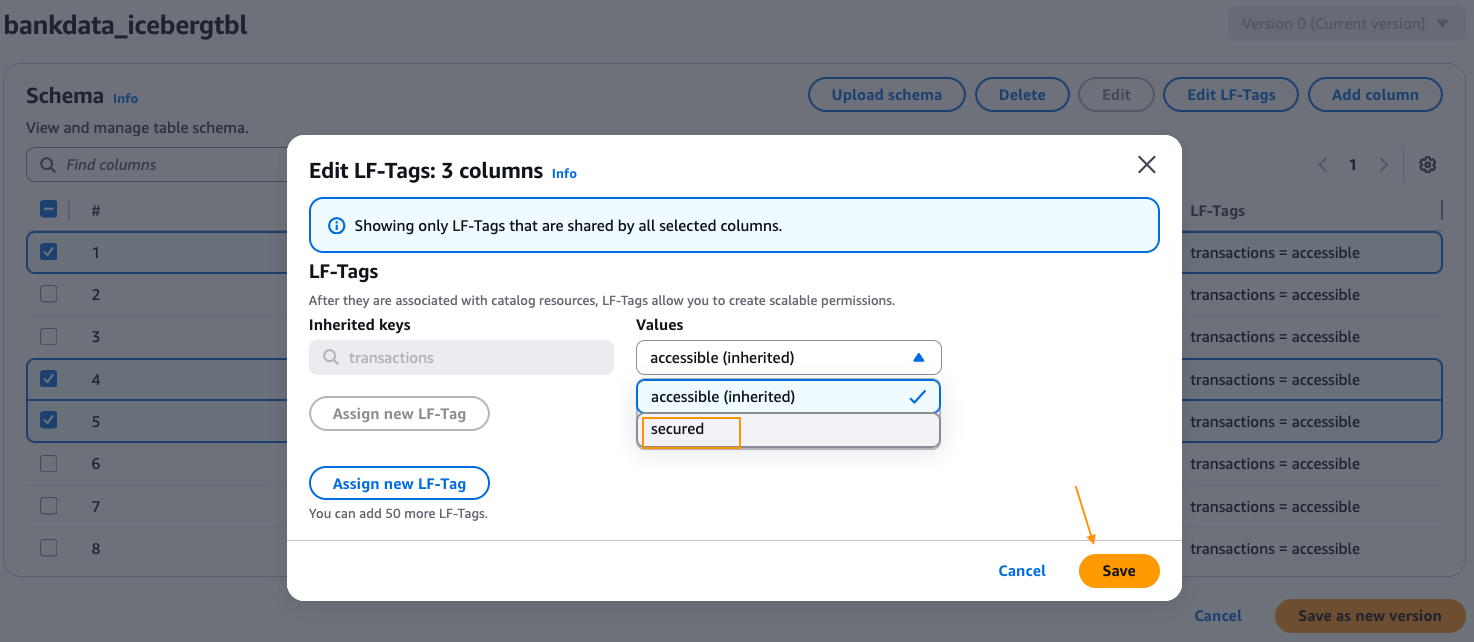
bankdata_icebergtbland confirm that the LF-Tagtransactions=accessibleis inherited by the desk. - Edit the schema of the desk and alter the LF-Tag worth on the columns
transaction_id,bank_account_number, andinitiator_nametotransactions=secured. After altering, select Save as new model.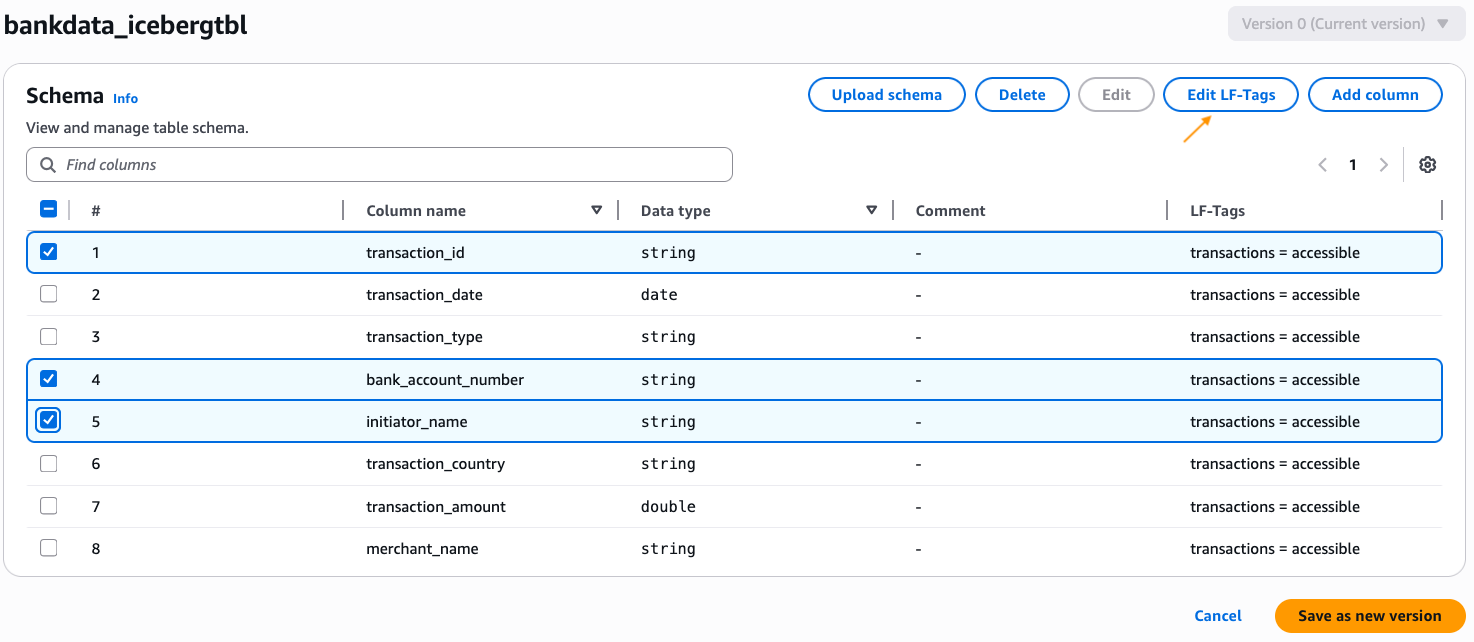
- Navigate to the Knowledge permissions web page on the Lake Formation console. Select Grant to grant permissions.
- Choose the IAM Id Middle group
DataScientistsfor Principals. Choose LF-Tagstransactionsand each the valuesaccessible,secured. Select Database DESCRIBE and Tables SELECT permissions. Select Grant.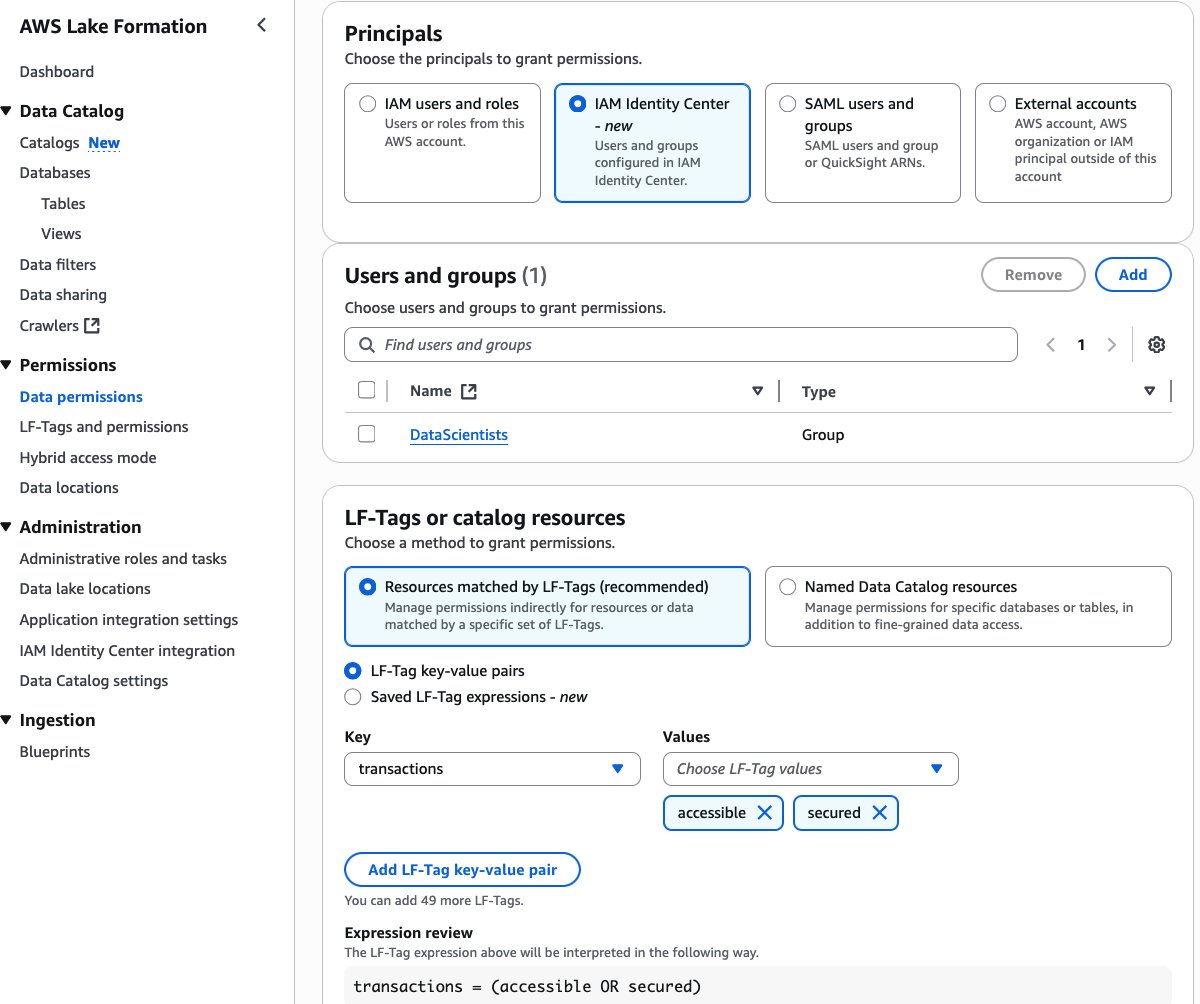
- On the Knowledge permissions web page on the Lake Formation console, select Grant once more.
- Choose the IAM Id Middle group
MarketAnalyticsfor Principals. Choose LF-Tagstransactionsand solely one of many values,accessible. Choose Database DESCRIBE and Tables SELECT permissions. Select Grant.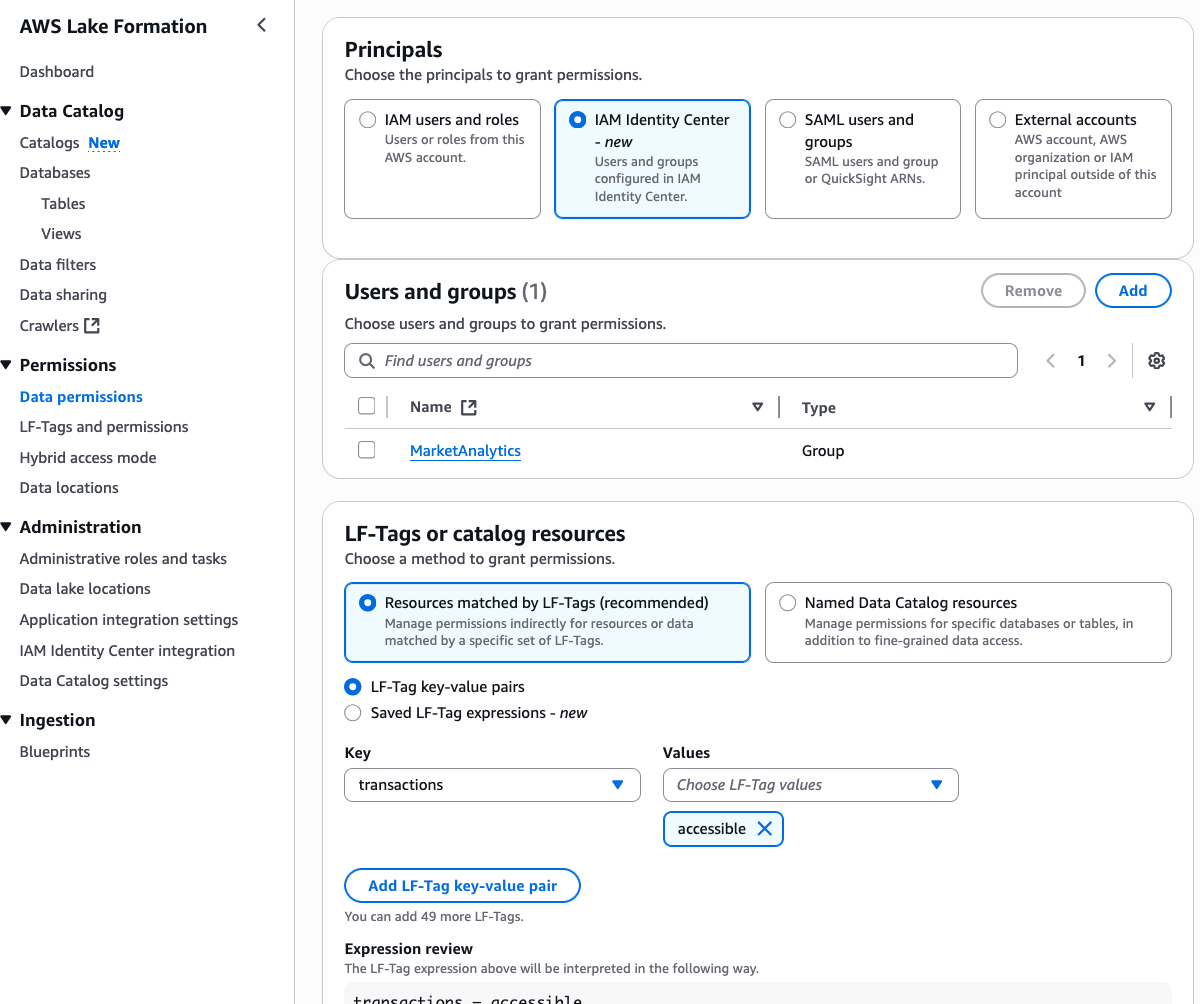
- Additionally grant DESCRIBE permission on the
defaultdatabase to each the IDC teams. - Confirm the granted permissions within the Knowledge permissions web page, by filtering with expression Principal sort = IAM Id Middle group.
Thus, we’ve granted all column entry on the desk bankdata_icebergtbl to the DataScientists group whereas securing three PII columns from the MarketAnalytics group.
In regards to the Authors