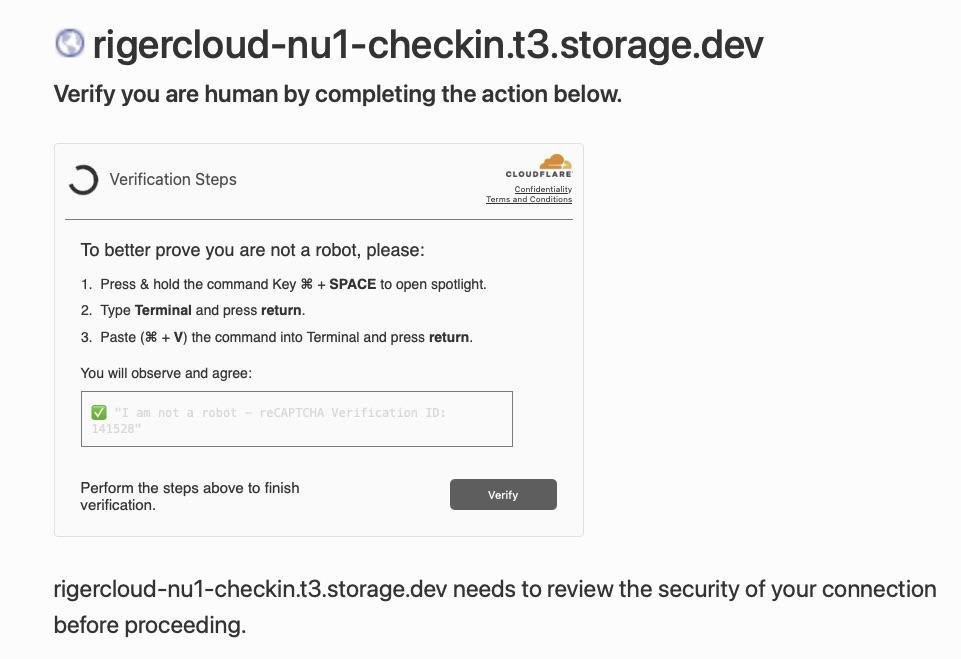
Hackers have a brand new device known as ClickFix. The brand new assault vector combines pretend human-verification prompts with malware, attempting to trick customers into operating Terminal instructions that bypass macOS safety.
The tactic, referred to as ClickFix, disguises malware supply as a routine human verification step. Victims are instructed to open instruments like Terminal or a command immediate and paste a command to finish verification.
Operating the command installs malicious software program on the system. Stolen knowledge can embody passwords, browser data, and cryptocurrency wallets.
Safety analysts say the method is spreading rapidly by compromised web sites, malicious commercials, and phishing campaigns.
CAPTCHAs are designed to tell apart human customers from automated bots and have change into a typical a part of shopping the net. Many websites depend on verification methods similar to Cloudflare safety checks or Google reCAPTCHA to filter automated visitors.
Attackers exploit customers’ familiarity with these safety screens. Faux verification pages seem after visiting compromised web sites or clicking malicious advertisements.
As an alternative of asking customers to establish photos or examine a field, the web page instructs guests to open a system device and paste a command into it. Operating the command downloads malware from a distant server and executes it regionally on the sufferer’s gadget.
ClickFix pretend CAPTCHA assaults are spreading quickly throughout the net
Safety researchers first recognized ClickFix campaigns in 2024 as attackers started experimenting with copy-and-paste malware supply strategies.
In contrast to older malware campaigns that relied on downloads or attachments, ClickFix convinces victims to run malicious instructions themselves. Eliminating apparent downloads has helped the tactic unfold rapidly throughout compromised web sites and phishing campaigns.
Researchers say detections of ClickFix-style assaults surged by greater than 500% between 2024 and 2025. Safety analysts now take into account it one of many fastest-growing social engineering threats on the web.
Latest campaigns have change into extra subtle, utilizing countdown timers and video directions in pretend CAPTCHA pages to information victims. Others use JavaScript to repeat malicious instructions to a person’s clipboard, growing the chance of an infection.
Though early ClickFix campaigns centered on Home windows methods, researchers now report variants designed particularly for macOS gadgets. Some malicious pages detect a customer’s working system and show directions tailor-made to Mac customers.
The prompts generally instruct victims to press Command-House to open Highlight, launch Terminal, and paste a command copied from the net web page.
As soon as executed, the command can set up information-stealing malware similar to Atomic macOS Stealer. The malware can harvest browser credentials, cookies, and cryptocurrency pockets knowledge from contaminated Macs.
Macs aren’t proof against assaults as a result of they depend on person conduct fairly than software program vulnerabilities. Whereas macOS safety protections can forestall an infection, they will not cease a person from intentionally operating a malicious command.
Why ClickFix pretend CAPTCHA scams bypass many safety defenses
Conventional malware detection usually focuses on blocking suspicious downloads or exploit exercise. ClickFix campaigns keep away from lots of these alerts by shifting the ultimate execution step to the person.
Safety researchers describe the tactic as a type of social engineering that exploits belief in routine system prompts. Victims find yourself executing the attacker’s code themselves.
Many assaults depend on official system utilities similar to PowerShell or Terminal to run instructions, a method usually known as “residing off the land.” Attackers use these built-in instruments as a substitute of customized malware loaders.
Safety software program might deal with the exercise as regular as a result of the instructions run inside trusted system utilities.
The right way to keep secure from pretend CAPTCHA malware and ClickFix scams
We all know that almost all AppleInsider customers in all probability will not fall for this. We assure you already know someone that may.
Inform them that probably the most dependable warning signal is easy. Official CAPTCHA methods by no means ask customers to open Terminal, PowerShell, or every other command interface and paste instructions to finish verification.
A verification immediate that instructs you to run instructions or paste textual content right into a system device is sort of definitely malicious. Closing the web page instantly is the most secure response.
Faux CAPTCHA scams usually seem on compromised web sites, malicious advertisements, or phishing pages designed to mimic official safety checks. Keep away from interacting with sudden verification prompts or suspicious pop-ups.
Updating browsers and working methods reduces publicity to malicious websites, whereas trendy safety instruments block identified threats. Consciousness is the best protection, as ClickFix assaults depend on deception fairly than software program vulnerabilities.