As cloud workloads change into extra agentic and AI programs deal with more and more delicate knowledge, belief have to be engineered instantly into infrastructure. Azure Built-in HSM brings {hardware}‑enforced key safety into Azure, extending cryptographic belief from silicon to providers by way of verifiable and clear design.
As cloud workloads change into extra agentic and AI programs more and more deal with mission‑vital knowledge, belief have to be engineered into the infrastructure at each layer. At Microsoft, safety is designed into the inspiration of our cloud infrastructure, from silicon to providers. With the Azure Built-in {Hardware} Safety Module (HSM), Microsoft is redefining how cryptographic belief is delivered within the cloud.
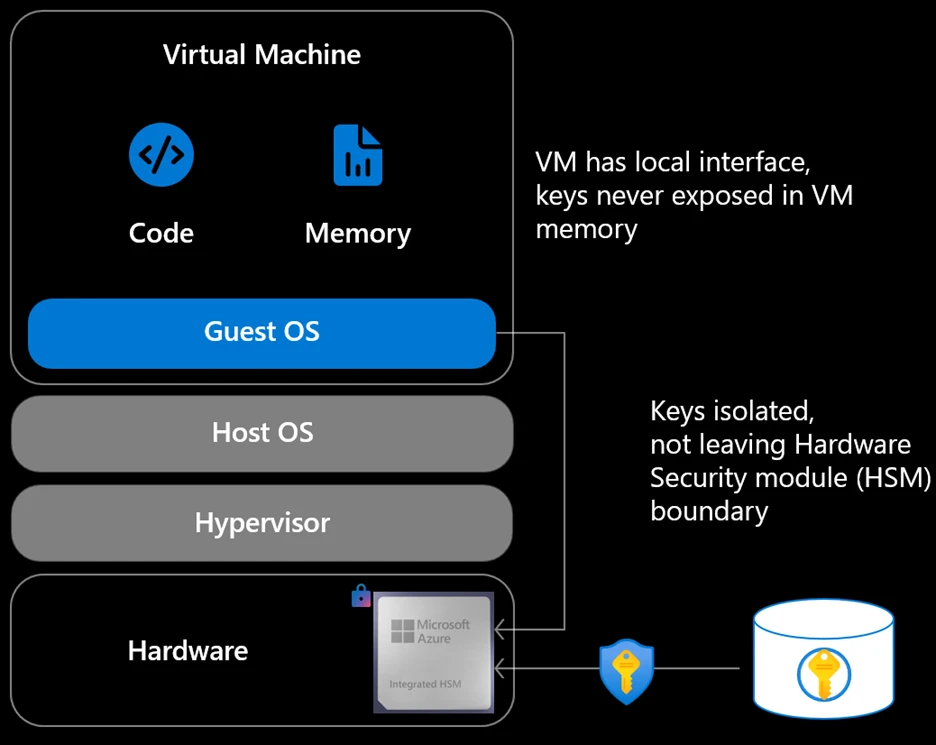
Azure Built-in HSM is a tamper‑resistant, Microsoft‑constructed {hardware} safety module built-in into each new Azure server, extending present key administration providers by bringing {hardware} enforced safety on to the place workloads execute. Slightly than relying solely on centralized providers, this strategy makes hardware-backed safety a local property of the compute platform itself.
Azure Built-in HSM is engineered to satisfy FIPS 140‑3 Stage 3, the gold customary for {hardware} safety modules utilized by governments and controlled industries worldwide. Stage 3 requires robust tamper resistance, hardware-enforced isolation, and safety in opposition to bodily and logical key extraction. By constructing these assurances instantly into the platform, Azure makes the best ranges of compliance a default property of the cloud, reasonably than a specialised configuration or premium add‑on.
Reinforcing transparency by way of belief with open-sourced designs
Our strategy to {hardware} safety is grounded in a easy perception: transparency builds belief, and trade collaboration strengthens safety. Openness strengthens belief by permitting prospects, companions, and regulators to validate design selections and safety boundaries.
This week, on the Open Compute Undertaking (OCP) EMEA Summit, we introduced plans to open the Azure Built-in HSM to the broader open {hardware} ecosystem. Via OCP, we plan to launch the Azure Built-in HSM firmware, driver, and software program stack as open supply, and launch an OCP workgroup to information ongoing improvement—spanning architectural design, protocol specs, firmware, and {hardware}. The Azure Built-in HSM firmware is now obtainable by way of the Azure Built-in HSM GitHub repository, alongside unbiased validation artifacts such because the OCP SAFE audit report.
This openness is especially vital for regulated industries and sovereign cloud situations, the place unbiased validation of safety controls is required. By making key elements obtainable for exterior overview, Azure Built-in HSM allows prospects, companions, and regulators to evaluate implementation particulars instantly reasonably than relying solely on vendor assertions.
This strategy strengthens confidence within the platform and helps set up a extra clear and verifiable basis for cloud safety, whereas lowering reliance on proprietary vendor particular protocols. At a time when cryptographic belief underpins all the things from AI inference to nationwide digital infrastructure, open sourcing the HSM is a sensible step towards interoperability, auditability, and buyer confidence.
A tiered strategy to key administration
This design enhances providers like Azure Key Vault and Azure Managed HSM, which proceed to supply centralized key lifecycle administration, governance, and coverage enforcement. Azure Built-in HSM provides a brand new layer; one which brings cryptographic safety all the way down to the person server, in order that keys are protected not simply when they’re saved however whereas they’re actively being utilized by workloads. The Azure Built-in HSM additionally helps trade requirements resembling TDISP, enabling safe binding between the HSM and confidential computing environments.
Within the coming weeks, Azure Built-in HSM will probably be obtainable in Azure V7 digital machines to all prospects globally.
Setting a brand new customary for server-local key safety at scale
With Azure Built-in HSM, encryption keys are generated, saved, and used fully inside hardened {hardware}. Keys are designed to by no means seem in host reminiscence, visitor reminiscence, or software program processes even throughout lively cryptographic operations. By protecting keys throughout the {hardware} boundary always, Azure Built-in HSM eliminates total lessons of key and credential exfiltration assaults that concentrate on reminiscence or software program layers.
The result’s true buyer management enforced by silicon, not coverage. Safety is now not depending on operational self-discipline or advanced isolation assumptions; it’s enforced by {hardware}.
Conventional cloud safety fashions depend on centralized HSM providers accessed over the community. Whereas efficient, these fashions introduce shared blast radius, scalability challenges, and efficiency constraints as workloads develop.
By anchoring cryptographic safety on to the server, safety scales naturally with compute. There are not any shared bottlenecks, no added community hops, and no have to commerce efficiency for cover. As Azure scales, safety scales with it.
With {hardware} roots of belief, measured boot, and attestation, Azure Built-in HSM makes belief verifiable reasonably than contractual. Prospects and regulators can cryptographically validate that accredited {hardware}, firmware, and configurations are in place. This may be additional verified by the open-source firmware. Belief is now not one thing you settle for; it’s one thing you may show.
Collectively, these capabilities set up a brand new baseline for cloud safety, one wherein hardware-enforced, verifiable belief is the default for contemporary workloads, from core infrastructure providers to the subsequent technology of AI. When mixed with confidential computing, open silicon roots of belief, Azure Enhance, and datacenter-level safe management modules, the Azure Built-in HSM helps set up a vertically built-in chain of belief, from silicon to software program.
We invite prospects, companions, and the broader open-source neighborhood to contribute to the structure and assist form future requirements. Collectively, we are able to construct safe, sovereign, and open cloud infrastructure for the challenges forward.
For added info, learn the announcement weblog and study extra about Azure Safety.