LLM Entry With out the Trouble
DevNet Studying Labs give builders preconfigured, in-browser environments for hands-on studying—no setup, no atmosphere points. Begin a lab, and also you’re coding in seconds.
Now we’re including LLM entry to that have. Cisco merchandise are more and more AI-powered, and learners have to work with LLMs hands-on—not simply examine them. However we will’t simply hand out API keys. Keys get leaked, shared outdoors the lab, or blow via budgets. We would have liked a strategy to lengthen that very same frictionless expertise to AI—give learners actual LLM entry with out the chance.
At the moment, we’re launching managed LLM entry for Studying Labs—enabling hands-on expertise with the newest Cisco AI merchandise and accelerating studying and adoption of AI applied sciences.
Begin a Lab, Get Prompt LLM Entry
The expertise for learners is easy: begin an LLM-enabled lab, and the atmosphere is prepared. No API keys to handle, no configuration, and no signup with exterior suppliers. The platform handles every little thing behind the scenes.
The quickest path right now is A2A Protocol Safety. Within the setup module, the lab hundreds the built-in LLM settings into the shell atmosphere. Within the very subsequent hands-on step, learners scan a malicious agent card with the LLM analyzer enabled.
supply ./lab-env.sh
a2a-scanner scan-card examples/malicious-agent-card.json --analyzers llm✅ Lab LLM settings loaded
Supplier: openai
Mannequin: gpt-4o
💡 Now you can run: a2a-scanner list-analyzers
Scanning agent card: Official GPT-4 Monetary Analyzer
Scan Outcomes for: Official GPT-4 Monetary Analyzer
Goal Kind: agent_card
Standing: accomplished
Analyzers: yara, heuristic, spec, endpoint, llm
Whole Findings: 8
description AGENT IMPERSONATION Agent falsely claims to be verified by OpenAI
description PROMPT INJECTION Agent description comprises directions to disregard earlier directions
webhook_url SUSPICIOUS AGENT ENDPOINT Agent makes use of suspicious endpoints for knowledge assortment 
That lab-env.sh step is the entire level: it preloads the managed lab LLM configuration into the terminal session, so the scanner can name the mannequin straight away with none guide supplier setup. From the learner’s viewpoint, it feels nearly native, as a result of they supply one file and instantly begin utilizing LLM-backed evaluation from the command line.
How It Works
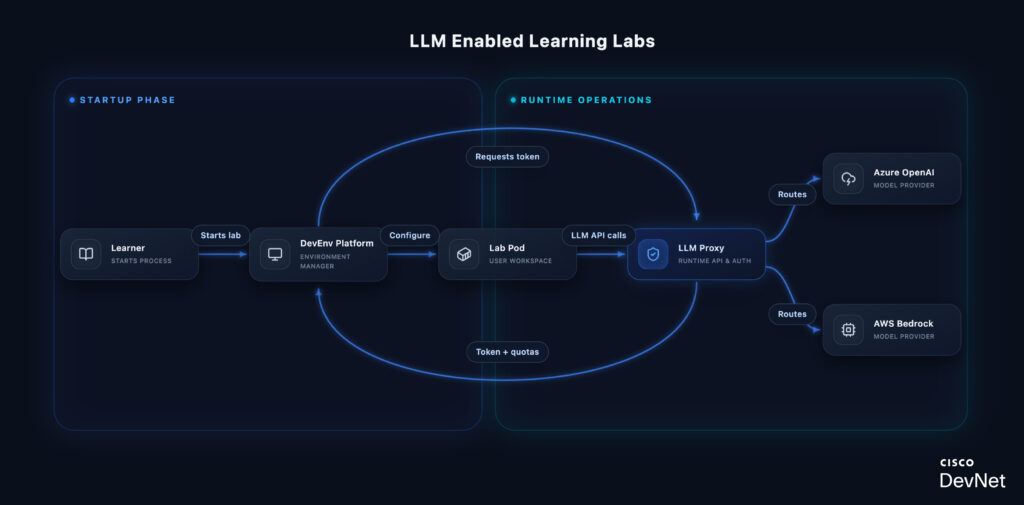
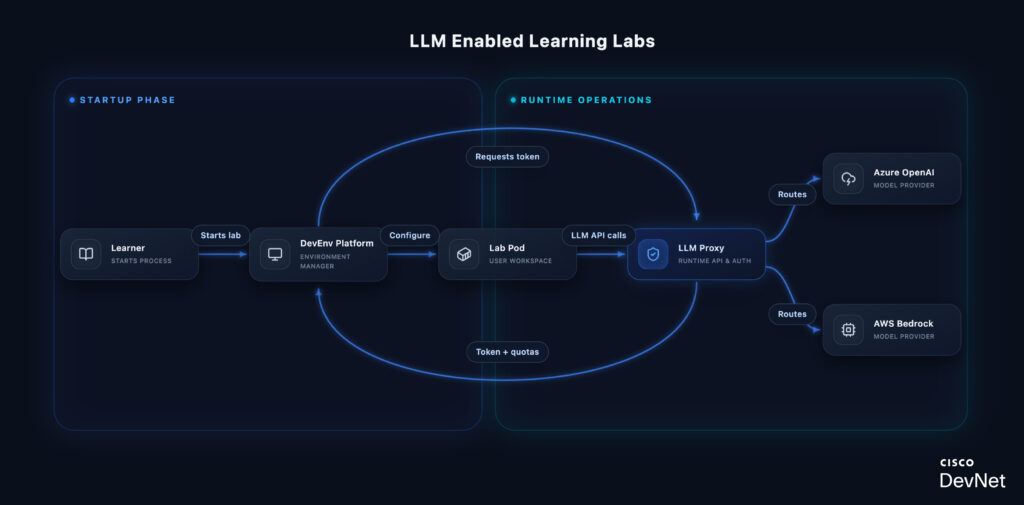
Why a proxy? The LLM Proxy abstracts a number of suppliers behind a single OpenAI-compatible endpoint. Learners write code in opposition to one API—the proxy handles routing to Azure OpenAI or AWS Bedrock primarily based on the mannequin requested. This implies lab content material doesn’t break once we add suppliers or change backends.
Quota enforcement occurs on the proxy, not the supplier. Every request is validated in opposition to the token’s remaining finances and request depend earlier than forwarding. When limits are hit, learners get a transparent error—not a shock invoice or silent failure.
Each request is tracked with person ID, lab ID, mannequin, and token utilization. This offers lab authors visibility into how learners work together with LLMs and helps us right-size quotas over time.
Palms-On with AI Safety
The primary wave of labs on this infrastructure spans Cisco’s AI safety tooling:
- A2A Protocol Safety — built-in LLM settings are loaded throughout setup and used instantly within the first agent-card scanning workflow
- AI Protection — makes use of the identical managed LLM entry within the BarryBot software workout routines
- Talent Safety — makes use of the identical managed LLM entry within the first skill-scanning workflow
- MCP Safety — provides LLM-powered semantic evaluation to MCP server and gear scanning
- OpenClaw Safety (coming quickly) — validates the built-in lab LLM throughout setup and makes use of it within the first actual ZeroClaw smoke take a look at
These aren’t theoretical workout routines. Learners are scanning sensible malicious examples, testing dwell safety workflows, and utilizing the identical Cisco AI safety tooling practitioners use within the discipline.
“We needed LLM entry to really feel like the remainder of Studying Labs: begin the lab, open the terminal, and the mannequin entry is already there. Learners get actual hands-on AI workflows with out chasing API keys, and we nonetheless preserve the controls we want round price, security, and abuse. I additionally preserve my very own working assortment of those labs at cs.co/aj.” — Barry Yuan
What’s Subsequent
We’re extending Studying Labs to help GPU-backed workloads utilizing NVIDIA time-slicing. This can let learners work hands-on with Cisco’s personal AI fashions—Basis-sec-8b for safety and the Deep Community Mannequin for networking—working domestically of their lab atmosphere. For the technical particulars on how we’re constructing this, see our GPU infrastructure sequence: Half 1 and Half 2.
Your suggestions shapes what we construct subsequent. Strive the labs and tell us what you’d wish to see.